Ransomware has been in the news a lot lately, ever since, a month ago, the City of Baltimore had their city government computer system shut down by the Robbinhood ransomware. Baltimore has refused to pay the ransom, and we applaud them for it. However, it all could have been avoided, or at least mitigated. Here’s how to protect a business or an individual from ransomware.
Ransomware is a specific type of malware which, once it infects your computer, encrypts and locks up your data, and holds your files hostage, and the only way to unlock it is to pay the hacker who did it. In other words, it is Internet extortion. There are other types of malware (some of which can end up being lethal), however ransomware is often the hacker’s method of choice when targeting large organizations that store vital information, such as hospitals and municipalities.
Originally identified by the FBI as an “Internet infection“, ransomware has been in widespread circulation since at least 2005. Just a few months ago ransomware called B0r0nt0K (like ‘BorontoK’ only the Os are replaced with 0s) was in the news for locking up computers and demanding a 20 Bitcoin (BTC) ransom (approximately $75,000 USD).
I don’t want people to think that Baltimore doesn’t have a backup. – Mayor Jack Young
However, this leaves the city without access to most of its data and many of its online services, including online payments, permits, program registration and municipal service requests.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
It’s important to note here that the City of Baltimore does have backups. In fact, says Mayor Young, “There is a backup system with the IT department, but we can’t just go and restore because we don’t know how far back the virus goes. So I don’t want people to think that Baltimore doesn’t have a backup.”
So the question is how could the City of Baltimore have better protected itself so that this didn’t happen, or, at least, so that they could have had their system up and running more quickly?
First, it has to be said: according to various security professionals, Baltimore was running an old Windows system that had a known security hole – the very security hole that the Robbinhood ransomware exploited – for which Microsoft had issued an advisory and a patch 2 years ago. Some, notably in the The New York Times, have suggested that the Baltimore hack was facilitated by the NSA’s hacking tool gone amuck, EternalBlue. Others, including in, again, The New York Times have attempted to discredit – or at least downplay – the idea that EternalBlue was involved. In the latter Times piece, they note that “More recently, according to cybersecurity experts, EternalBlue has turned up in attacks on local governments in the United States, which often used aging equipment and fail to keep their software up to date. A patch issued by Microsoft in 2017, but apparently never installed in Baltimore, should have made Windows secure against EternalBlue.”
That said, even given that, there are also ways that Baltimore could have ensured that if a ransomware attack did occur, they would be able to ameliorate it with alacrity.
Here’s how to protect yourself from ransomware whether a private individual or an organization.
How to Protect Yourself or Your Business from Ransomware
Security
1. Security. Be sure to apply all security updates and software patches as soon as they come out or you are notified of them. Also be sure that you are running a robust anti-virus program and that you have it updating. The same for your anti-spam program. If you are a business or other organization, make sure that all of your employees do the same, and also minimize the number of people who have the ability to compromise your system, either unwittingly or intentionally.
Attending to step 1 is what will protect you against getting hit with ransomware (and other malware) in the first place.
Backups
2. Backups. Back up your system. Period. No excuses. And not just to one place, and not just with one method, and not to just one type of media. And not just every few days or, heaven forbid, once a week.
We recommend backing up at least every day, and retaining at least a week’s worth of backups or 5 backups from alternating days or backups from the last 4 Mondays (or Tuesdays, etc., pick a day of the week). Each of these backup retention schedules has their advantages and disadvantages, but they all will be insurance against ransomware (as well as catastrophic system failures such as hard drive crashes).
At least one of these these backup media should be offline as much as possible (and ideally always except when you are backing up). For example, we have a portable hard drive which we use specifically as one of our backup media, and it is only connected to the system it is backing up when we manually back it up. Is it a bit of a hassle? Sure, but having everything locked up or gone is exponentially more of a hassle.
Another can be in the cloud, although as we are fond of telling anyone who will listen (and many who won’t) ‘the cloud’ is just another name for someone else’s computer.
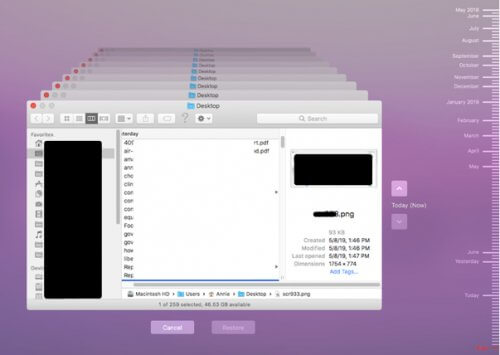
We are a Mac shop, so one of our backup methods is Time Machine to an external hard drive. Time Machine makes hourly backups for the past 24 hours, daily backups for the past month, and weekly backups for all previous months. As you can see from this picture from our Time Machine install, our backups go all the way back to more than a year ago.
This is in addition to the backups we do to the external drives.
Security and backups – it’s really that simple, although not necessarily easy.
But no matter how time or labor intensive it is to make sure both your security and backups are robust and up-to-date, it is orders of magnitude easier than trying to recover from a ransomware lock up.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.