Category: Security
Facebook Messenger Read Receipts Huge Risk for the Abused, Bullied and Stalked
Facebook enables abusers. And they know that they do it. In a world full of online stalking, cyber bullying, and intimidation of the abused and traumatized, the fact that Facebook has never given users the ability to turn off Facebook Messenger read receipts may be one of the most egregious hand-offs of power to abusers ever to be perpetrated by a social media platform.
Fraudulent Charges from Surveymak.org and Receptionistway.com Appearing on Compromised Credit and Debit Cards
Check your statements carefully, as compromised debit cards and credit cards are being used to steal small-dollar charges by surveymak.org and receptionistway.com. Here’s what to do if your card is stolen or compromised; for example if you find charges from either of surveymak.org or receptionistway.com it’s time to dispute them and to cancel your card (we explain how below).
UPDATE: FBI Responds to Apple’s 3 New Cybersecurity Measures
This is a continuation of a previous post. URGENT UPDATE: The FBI informed the newshounds at the Wall Street Journal that it opposed many of the new modifications introduced by Apple. Another online source indicated that the FBI was, indeed, unhappy with several of the proposed adjustments to the encryption…
LastPass Hack Update: Customer Information Accessed
LastPass, the password storage service, has just revealed that customer information was accessed during the hack of their data that occurred at the end of August 2022. The data was stored with a 3rd-party cloud storage provider. Previously they had said that it was “limited to the LastPass Development environment in which some of our source code and technical information was taken.”
TikTok Toxic: Is TikTok Safe? FCC Commissioner and Others Say “No”
Among the massive number of Google searches about TikTok, such as “where are TikTok drafts” and “TikTok canvas size”, a new search is rising to the top: Is TikTok safe? And according to some very high level folks who should know, the answer is “no”. (By the way, you access your TikTok drafts folder from your profile page, and the TikTok canvas size is 1080 by 1920.) But back to the question of is TikTok safe: when an FCC commissioner says that TikTok is not only not safe, but should be banned due to ongoing reports of the private data of U.S. TikTok users being funneled to the Chinese government, it at least bears a closer look.
Yes, Facebook’s Data Mining is a Problem
Yes, Facebook has once again admitted that there is seriously a problem with the way they are handling user data. Are we really that surprised? Maybe this is the first time you’ve seen the news that Facebook’s privacy issues are spiraling out of control. Or perhaps this is the first time you’ve cared to search for it. This isn’t a new occurrence.
“Remember This Browser?” and Other Cookie-Pushing Questions
Cookies are delicious, depending on your palate. Some like sugar, I’m partial to oatmeal raisin. Others may prefer chocolate chip, and advertisers like the digital ones. And while the wording must be confusing for many, many people, there is no shortage of digital cookies. The majority of modern websites rely extensively on several different types of cookie to provide their users with services. Some are completely innocent, others may be more insidious. The thing is, a cookie by any other name is still a cookie, although the end-user may not realize it.
FBI Urges 2022 China Olympics Athletes to Leave Phones at Home and Use Temporary ‘Burner’ Phones (Includes Full Text of Warning)
The FBI is warning U.S. Olympic athletes who are attending the 2022 Olympics in Beijing, China, to leave their cell phones at home, and instead pick up and bring temporary mobile phones, so-called ‘burner phones’ or disposable phones. The warning, put out last night (January 1, 2022), came from the FBI’s Cyber Division, and was announced as a warning to private industry. While the warning was also geared towards network operators and other industries, the warning specifically, and unusually, speaks directly to individuals as well.
Yes the FBI Got Hacked. Yes They Know. Yes It’s Worrying.
Over the weekend none other than the FBI had their system hacked. The hackers then proceeded to send email out ‘from’ eims@ic.fbi.gov with the subject “Urgent: Threat actor in systems”, using the FBI’s own mail servers and warning that of a threat from “Vinny Troia” whom, the email says, is part of an extortion gang called “TheDarkOverlord”.
Internet Crime Gang Stealing Reward Points and Gift Cards Out of Email Inboxes
Talk about cherry picking! An international Internet crime gang is gaining access to as many as 100,000 compromised email inboxes a day, and all they are doing is searching for and stealing digital gift cards and rewards points.
Massive T-Mobile Data Breach of User Personal Information Includes Social Security Numbers
A massive security breach at T-Mobile has exposed the personal private data of nearly 50million T-Mobile customers and prospects, including social security numbers and drivers license numbers. And it doesn’t matter whether you are a current, past, or even prospective customer of T-Mobile, your data has been compromised. By “prospective” we mean someone who has applied for an account with T-Mobile even if they never actually signed up. And that is because the T-Mobile data breach includes those social security numbers which are, of course, required for just about every service that is going to extend credit to you.
Parler Shut Down but Not Before Massive Data Scrape of its Users and Their Posts, Videos and Pictures
As Parler sues Amazon for shutting them down, more than 70 TB of identifying Parler user data revealed to have been grabbed and archived.
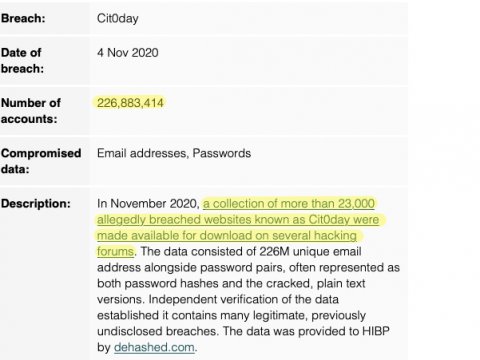
Enormous Collection of Over 23000 Breached Databases Leaked with the Cit0Day Data Breach – and What to Do About It
The Cit0Day index collection contains the breached user email addresses and passwords of more than 23000 services, likely including yours.
Multi-factor Authentication and Why You Need It
As the threat of cyberattacks keeps on increasing, individuals and organizations need to take the necessary steps to protect their data. One of the tried and tested ways of deterring data breaches is using multi-factor authentication, commonly known as MFA. The primary reason MFA is hailed as an effective method…
The NSA is Telling Mobile Users to Turn Off Find My Phone, WiFi, and Bluetooth. Here’s Why
The National Security Agency (NSA) is recommending that people who are concerned about privacy turn off Wi-Fi, Find-My-Phone, and Bluetooth whenever they do not need to use those services. Yes, this is the same NSA about whom we have written in the past, including for being spanked by the court…