Let us cut to the chase right up front and then circle back to explain: the Cit0Day file collection of more than 23,000 breached databases, and the associated user email addresses and passwords, is a collection of the breached data of more than 23,000 different websites and services, with user email addresses and passwords for most (if not all) of those 23,000+ websites and services.
In other words it is, if you will, the breach of breaches. Each one of the 23,000+ (23,600 by most counts) breached databases represents the data breach of one particular website or service. And the Cit0Day index and collection has been found on at least two different sites, meaning that it is definitely out there in the wild.
In fact, Troy Hunt, widely considered a top authority on whether an alleged collection of breached data is actually legitimately something to worry about, and also the creator of HaveIBeenPwned, went through a long analysis of the Cit0Day data before determining that a) it was absolutely legit (in that it really did contain email addresses and associated cracked passwords) and b) it was bad enough to merit uploading them all into the HaveIBeenPwned database.
It’s worth noting here that Troy’s HaveIBeenPwned service is very much worth signing up for, particularly as it is essentially hand-curated by Troy himself. HaveIBeenPwned notifies you by email if your data shows up in a data breach, and includes information about which of your data has been breached. You can sign up for HaveIBeenPwned here.
Notification from HaveIBeenPwned
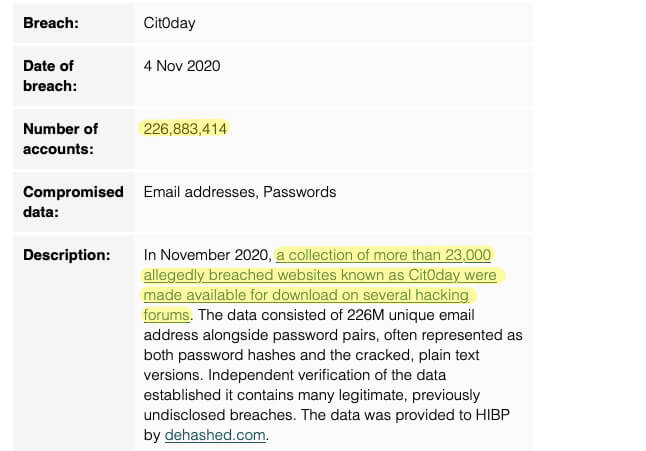
In November 2020, a collection of more than 23,000 allegedly breached websites known as Cit0day were made available for download on several hacking forums. The data consisted of 226M unique email address alongside password pairs, often represented as both password hashes and the cracked, plain text versions. Independent verification of the data established it contains many legitimate, previously undisclosed breaches. The data was provided to HIBP by dehashed.com.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
Basically, if you have ever used an online service, or visited a website where you had to create an account, you can assume that your email address and password associated with that site are now being circulated and traded and potentially used against you by at least one, and possibly more, bad people.
So what does one do when one has to assume that every single one of their online accounts has been potentially compromised?
Well, you need to act as if you know that each of your accounts has been compromised. Here’s what we do:
What to Do When All of Your Online Accounts Have Been Compromised
Let’s face it: we all have lots and lots of online accounts. More than we can remember. And so we have to triage. And what we mean by that is, we have to figure out which accounts to worry about first, and we do that by determining which accounts can have the most serious, negative impact on our lives if they were to be breached. Such accounts include:
- Bank accounts
- Brokerage, retirement, and other financial services
- Credit card and loan accounts
- Health care, pharmacy, and other medical accounts
- Insurance accounts
For all of the above accounts, change your password. And for the love of Pete (and just who is this Pete? Is he related to the Bob who is your uncle?) enable 2FA (2-factor authentication) if you haven’t already!
Once you’ve attended to the most critical of these accounts, turn your attention to your social media accounts. While you may not think of social media accounts, such as Facebook, Twitter, Instagram, and TikTok, as particularly important, if someone starts impersonating you, they can influence your friends, trick your friends into giving up their own credentials, or even get money out of your friends by pretending to be you and in distress.
Next, no doubt as you go through your day you will interact with, and therefore remember, other sites and services for which you signed up and which have your email address, username, and password. Start keeping a running list of such sites, and for each one change your password. By creating the list of such sites this time you’ll be that much ahead of the game next time. And make no mistake, there will be a next time.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.









