Category: Security
Gmail’s Spam Problem and What You Can Do About It
Google’s Gmail has been hailed as one of the best free email services around the world. Gmail has great security features, including 2-step authentication that provides industry-standard protection against hackers. In addition, it has robust spam filters, which will send all your bad incoming mail to the spam folder.
State of Colorado Pandemic Unemployment System Compromised
The State of Colorado has issued a statement indicating that their Pandemic Unemployment System was compromised over the weekend.
EasyJet Hacked Compromising 9Million Customers Including Credit Card Info
EasyJet has been hacked, compromising the data of 9 million people including credit card information, names, email addresses, and travel details.
The Story of CTRL + ALT + DEL: How these Shortcut Keys Became Famous
You probably do not think much about it as you press the three-key combination of Control-Alt-Delete, commonly known as security keys or the “three-finger salute” whenever Windows acts up. You probably also use it when locking or logging out of Remote Desktop. But did you know that this combination came…
The Cognizant Breach: What You Should Know About Maze Ransomware Attacks
Cognizant, an American company providing IT services based in Teaneck, New Jersey, is one of the latest victims of the infamous Maze ransomware. The IT services provider operating in more than 37 countries, with a turnover of $16bn, said the attack took place on Friday, April 17th. According to the…
What is Zoom and Why is Everyone Using It?
Zoom is Becoming a Lifeline During COVID-19. As the coronavirus pandemic continues to ravage the world, global gatherings and conferences are shutting down. First, it was the Mobile World Conference, then Facebook’s F8 and Microsoft’s MVP summit. Many other gatherings were canceled or rescheduled as the world sought to fight…
Sen. Moran Introduces Federal Data Privacy Legislation
U.S. Senator and Consumer Protection Subcommittee Chairman, Jerry Moran, has introduced a Consumer Data Privacy and Security Act. The bill seeks to strengthen the laws governing personal data and create regulations and standards for American businesses that gather, process and use consumers’ personal data. The Consumer Data Privacy and Security…
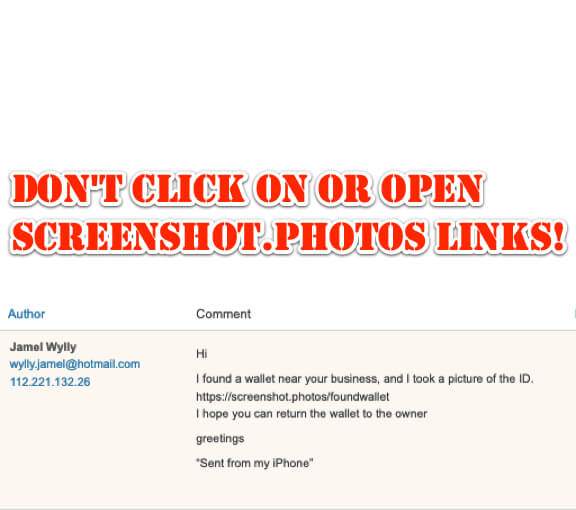
Don’t Click On or Open Screenshot[.]photos Links!
If out of the blue you get a message with a link to screenshot.photos in it, don’t click on it! It is a scam trying to get you to click on the link.
250 Million Microsoft Customer Support Records Exposed
As many as 250 million Microsoft customer records have been exposed, being wide open to anyone with a web browser, and not requiring a password.
Update Windows Immediately! NSA and Microsoft Announce Critical Security Flaw in Windows
The NSA is urging Windows users to update Windows 10 right now with the CVE-2020-0601 patch, owing to a critical security flaw discovered by the NSA caused by “essentially a mistake in the computer code.”
Urgent: Update Firefox NOW! In Rare Move Immediate Firefox Update Urged by Homeland Security
In a rare move, Firefox users are being urged to update Firefox immediately by the Department of Homeland Security.
If You Get a Notice from GoDaddy that They are Suspending an Email Address DON’T Click on It!
If you receive an email like the one below from GoDaddy saying that they are suspending your email address and that you need to verify your account, don’t click on it!
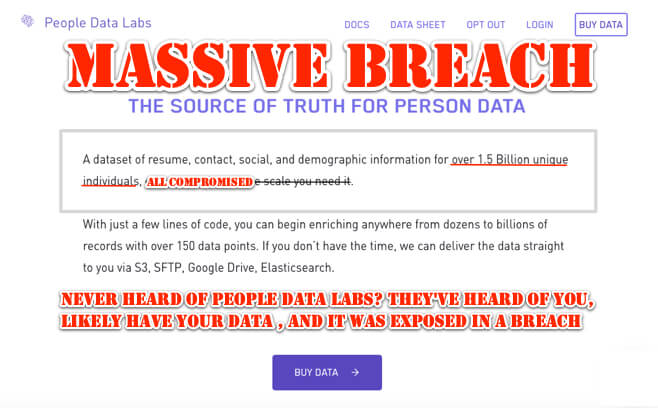
Never Heard of People Data Labs? They’ve Heard of You, Likely Have Your Data and It Was Exposed in a Breach
People Data Lab (PDL), a data “enrichment” company, boasts that they have data on 1.5 billion people, almost certainly including you. That data, stored on an Elasticsearch server, was all breached in November.
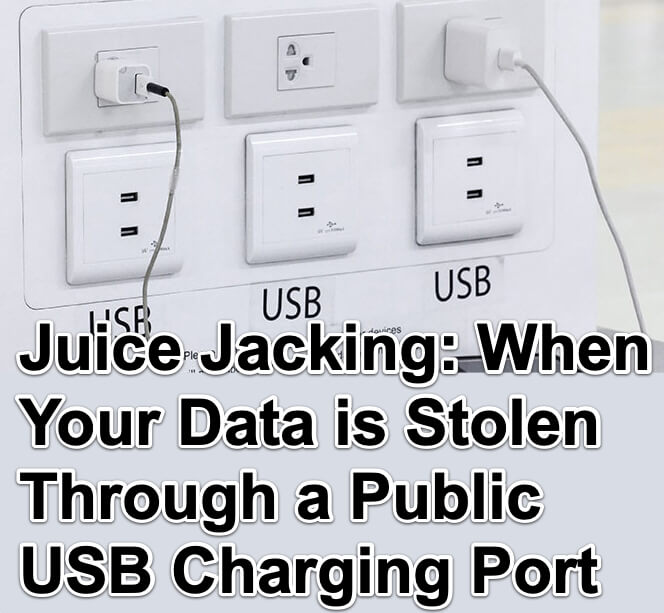
Juice Jacking – When Your Data is Stolen Through a Public USB Charging Port
Juice Jacking: the LA DA’s office is warning about it, Snopes says it’s real, alright. But just what is juice jacking? And how real is the threat? Here’s all of the info you need about juice jacking and the threat it poses to you.
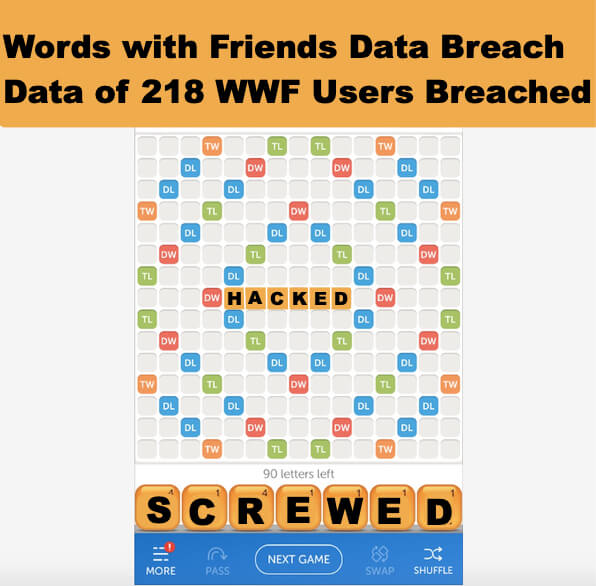
Words with Friends Hacked – Data of 218 Million WWF Users Breached Along with Zynga Draw Something
Sometime in the past few weeks a hacker calling himself Gnosticplayers hacked into Zynga’s Words with Friends database; the Words with Friends hack breached the personal data of more than 218 million Words with Friends players.