China and the United States have been hacking each other for years. But the U.S. distinguishes between military espionage and “economic espionage”, the official U.S. position being that military espionage (which the U.S. does) is acceptable, while economic espionage (which China does along with military espionage) is not acceptable. Now the U.S. has indicted 5 Chinese military officials – members of the People’s Liberation Army elusive “Unit 61398” – with economic espionage for hacking into Westinghouse, Alcoa, U.S. Steel, SolarWorld, United Steel Workers Union, and Allegheny Technologies. (Full text of first 20 pages of indictment and link to full text below.)
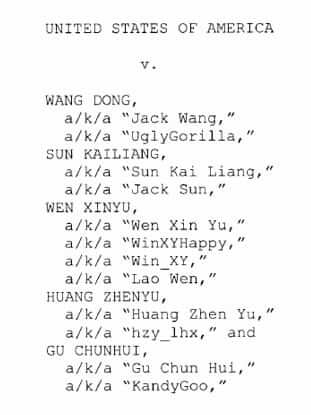
The five members of the PLA Unit 61398 – a unit described as being the PLA’s “cybertroops” – are Gu Chunhui, Wang Dong, Sun Kailiang, Wen Xinyu, and Huang Zhenyu, using, among others, the nickname handles KandyGoo, UglyGorilla, Jack Sun, WinXYHappy, and hzy_lhx, respectively.
Said John Carlin, Assistant U.S. Attorney General for National Security, “While the men and women of our American businesses spent their business days innovating… these members of Unit 61398 were spending their business days in Shanghai stealing the fruits of our labour.”
Of course, China is loudly protesting this action, pointing to, among other things, the fact that the U.S. NSA has had privacy issues of its own. The U.S. counters that the U.S. spies only to keep its citizens safe (military espionage), not to gain economic advantages by spying on corporations as China has done (economic espionage).
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
So what will come of this? Likely not much, as it is exceedingly unlikely that China would extradite their cybertroops to the U.S. for prosecution, even if they conceded wrongdoing.
Full Text of United States Indictment Against 5 Chinese Members of China’s People’s Liberation Army Unit 61398 for Economic Espionage Against Westinghouse, U.S. Steel, Alcoa, SolarWorld, United Steel Workers Union, and Allegheny Technologies (First 20 pages)
UNITED STATES DISTRICT COURT
WESTERN DISTRICT OF PENNSYLVANIA
UNITED STATES OF AMERICA
v. Criminal No.
WANG DONG,
a/k/a “Jack Wang,” a/k/a “UglyGorilla,” SUN KAILIANG,
a/k/a “Sun Kai Liang,” a/k/a “Jack Sun,”
WEN XINYU,
a/k/a “Wen Xin Yu,” a/k/a “WinXYHappy,” a/k/a “Win___XY,”
a/k/a “Lao Wen,”
HUANG ZHENYU,
a/k/a “Huang Zhen Yu,” a/k/a “hzy lhx,” and GU CHUNHUI,
a/k/a “Gu Chun Hui,” a/k/a “KandyGoo,”INDICTMENT
CLERK U.S. DISTRICT COURTWEST. DIST. OF PENNSYLVANIA
COUNT ONE
(Conspiracy to Commit Computer Fraud and Abuse) The Grand Jury Charges: INTRODUCTION 1. From at least in or about 2006 up to and including at least in or about April 2014, members of the People’s Liberation Army (“PLA”), the military of the People’s Republic of China (“China”), conspired together and with each other to hack into the computers of commercial entities located in the Western District of Pennsylvania and elsewhere in the United States, to maintain unauthorized access to those computers, and to steal information from those entities that would be useful to their competitors in China, including state-owned enterprises (“SOEs”).
2. In some cases, the conspirators stole trade secrets that would have been particularly beneficial to Chinese companies at the time they were stolen.
For example, as described in more detail below, an Oregon producer of solar panel technology was rapidly losing its market share to Chinese competitors that were systematically pricing exports well below production costs; at or around the same time, members of the conspiracy stole cost and pricing information from the Oregon producer. And while a Pennsylvania nuclear power plant manufacturer was negotiating with a Chinese company over the construction and operation of four power plants in China, the conspirators stole, among other things, proprietary and confidential technical and design specifications for pipes, pipe supports, and pipe routing for those nuclear power plants that would enable any competitor looking to build a similar plant to save on research and development costs in the development of such designs.
3. In the case of both of those American victims and others, the conspirators also stole sensitive, internal communications that would provide a competitor, or adversary in litigation, with insight into the strategy and vulnerabilities of the American entity.
4. Meanwhile, during the period relevant to this Indictment, Chinese firms hired the same PLA Unit where the defendants worked to provide information technology services. For example, one SOE involved in trade litigation against some of the American victims mentioned herein hired the Unit, and one of the co-conspirators charged herein, to build a “secret” database to hold corporate “intelligence.”
THE DEFENDANTS
5. At various times relevant to this Indictment, Defendants WANG DONG, a/k/a “Jack Wang,” a/k/a “UglyGorilla” (hereinafter “Defendant WANG”); SUN KAILIANG, a/k/a “Sun Kai Liang,” a/k/a “Jack Sun” (hereinafter “Defendant SUN”); WEN XINYU, a/k/a “Wen Xin Yu,” a/k/a “WinXYHappy,” a/k/a “Win XY,” a/k/a “Lao Wen” (hereinafter “Defendant WEN”); HUANG ZHENYU, a/k/a “Huang Zhen Yu,” a/k/a “hzylhx,” (hereinafter “Defendant HUANG”); and GU CHUNHUI, a/k/a “Gu Chun Hui,” a/k/a “KandyGoo” (hereinafter “Defendant GU”), whose photographs are attached as Exhibits A through E, respectively, worked together and with others known and unknown to the Grand Jury for the PLA’s General Staff, Third Department (“3PLA”), a signals intelligence component of the PLA, in a Unit known by the Military Unit Code Designator 61398 (“Unit 61398”), and in the vicinity of 208 Datong Road, Pudong District, Shanghai, China.
6. The co-conspirators’ hacking activities are described in more detail below but are summarized here as follows:
a. In or about 2007, Westinghouse Electric Company (“Westinghouse”), which is headquartered in the Western District of Pennsylvania, reached an agreement with a Chinese state-owned nuclear power company (“SOE-1”) to construct and operate four nuclear power plants in China. Negotiations regarding the details of that transaction, such as limitations on which technology would be provided to SOE-1 and under what conditions, continued up to and including 2013. In or about 2010 and 2011, while negotiations were ongoing, Defendant SUN stole from Westinghouse’s computers, among other things, proprietary and confidential technical and design specifications for pipes, pipe supports, and pipe routing within the nuclear power plants that Westinghouse was contracted to build, as well as internal Westinghouse communications concerning the company’s strategy for doing business with SOE-1 in China and the potential that SOE-1 may eventually become a competitor.
b. In or about May and July 2012, Defendant WEN hacked into the computers of U.S. subsidiaries of SolarWorld AG, a German solar products manufacturing company, including a production facility located in Hillsboro, Oregon, and a sales facility located in Camarillo, California (collectively, “SolarWorld”). From in or about May 2012 up to and including at least in or about September 2012, Defendant WEN and at least one unidentified co-conspirator stole thousands of e-mails and related attachments that provided detailed information about SolarWorld’s financial position, production capabilities, cost structure, and business strategy. Meanwhile, contemporaneous with that hacking, SolarWorld was an active litigant in trade cases against Chinese solar manufacturers, several of which reported in filings with the U.S. Securities and Exchange Commission (“SEC”) that their sales revenues had increased each year from 2009 through 2011. In or about May 2012, the Department of Commerce imposed significant duties on Chinese imports of solar products, based on its finding that those manufacturers had received unfair subsidies from China and had “dumped” large volumes of solar products into U.S. markets at prices below fair value, severely undercutting competitors like SolarWorld and, in some cases, helping to drive the most vulnerable American solar products manufacturers out of business. Several Chinese solar manufacturers subsequently reported in SEC filings that, in 2012, their sales revenues had decreased from 2011, and their net income and profit margins had dropped to five-year lows.
c. Between in or about 2009 and in or about 2012, United States Steel Corporation (“U.S. Steel”), which is headquartered in the Western District of Pennsylvania, litigated a number of trade cases against the Chinese steel industry, including specifically one large, Chinese state-owned steel company (“SOE-2”). About two weeks before the anticipated decision in one of those disputes in 2010, Defendant SUN targeted one of the employees working in the relevant division of U.S. Steel with an e-mail message, known as a “spearphishing” message, that was designed to trick the employee who received it into allowing SUN access to the employee’s computer. At or about that time, Defendant WANG stole hostnames and descriptions for more than 1,700 servers, including servers that controlled physical access to the company’s facilities and mobile device access to the company’s networks.
d. Allegheny Technologies Incorporated (“ATI”), a specialty metals manufacturer headquartered in the Western District of Pennsylvania, has since in or about 1995 been a partner in a joint venture with SOE-2 and was, between 2009 and 2012, also an adversary of SOE-2 in litigation before the World Trade Organization (“WTO”). In April 2012, the day after a board meeting for the joint venture in Shanghai, China, Defendant WEN stole network credentials for virtually every employee at the company, which would have allowed wide-ranging and persistent access to ATI’s computers.
e. The United Steel, Paper and Forestry, Rubber, Manufacturing, Energy, Allied Industrial and Service Workers International Union (“USW”), headquartered in the Western District of Pennsylvania, has long been a vocal opponent of Chinese trade practices. In 2012, on or about the day that the USW’s President issued a “call to action” against Chinese policies, Defendant WEN stole e-mail messages containing strategic discussions from senior union employees. And two days after the union publicly urged Congress to pass legislation that would have imposed duties on Chinese imports, Defendant WEN stole more e-mail messages containing internal, strategic discussions.
f. In or about 2008, Alcoa Incorporated (“Alcoa”), an aluminum manufacturer whose principal office is located in the Western District of Pennsylvania, announced a partnership with a Chinese state-owned aluminum company to acquire a stake in another foreign mining company. Approximately three weeks later, Defendant SUN targeted senior Alcoa managers with spearphishing messages designed to trick the recipients into providing SUN with access to the company’s computers.
7. As described above, Defendants WANG, SUN, and WEN, among others known and unknown to the Grand Jury, hacked or attempted to hack into at least the U.S. companies described above.
8. Contemporaneously, beginning at least in or about 2006 and continuing until at least in or about 2012, Defendant HUANG was a computer programmer within the same military Unit. He facilitated hacking activities by registering and managing domain accounts that his co-conspirators, including at least Defendants WANG, SUN, and WEN, used to commit those crimes. Meanwhile, beginning at least in or about 2006 and continuing until at least in or about 2009, Unit 61398 assigned Defendant HUANG to perform programming work for SOE-2, including the creation of a “secret” database for SOE-2 designed to hold corporate “intelligence” about the iron and steel industries, including information about American companies.
9. Like Defendant HUANG, beginning at least in or about 2006 and continuing until at least in or about 2010, Defendant GU managed domain accounts used to facilitate hacking activities against American companies. Defendant GU also tested spearphishing messages in furtherance of the conspiracy.
MANNER AND MEANS OF THE CONSPIRACY
10. The members of the conspiracy, who are both known and unknown to the Grand Jury, used the following manner and means to accomplish their objectives, which included gaining unauthorized access to computers and using that access to steal information.
11. As described above, the co-conspirators used e-mail messages known as “spearphishing” messages to trick unwitting recipients into giving the co-conspirators access to their computers. Spearphishing messages were typically designed to resemble e-mails from trustworthy senders, like colleagues, and encouraged the recipients to open attached files or click on hyperlinks in the messages. However, the attached or linked files, once opened, installed “malware” — malicious code – that provided unauthorized access to the recipient’s computer (known as a “backdoor”), thereby allowing the co-conspirators to bypass normal authentication procedures in the future.
12. After creating a backdoor, the malware typically attempted to contact other computers controlled by the coconspirators by sending them a short message known as a “beacon.” These beacons typically (1) notified the co-conspirators of the successful penetration of a victim’s computer; (2) provided some information about the victim’s computer useful for future intrusion activity; and (3) solicited additional instructions from the co-conspirators.
13. During the conspiracy, the co-conspirators controlled compromised computers in the United States besides those belonging to the six entities named above. The co-conspirators generally used those computers, known as “hop points,” to access other victims’ computers, and in so doing, the co-conspirators attempted to mask the true identity and location of the computers in China from which they were actually conducting their hacking activity. Among other things, the co-conspirators used hop points to research victims, send spearphishing e-mails, store and distribute additional malware, manage malware, and transfer exfiltrated data. Some hop points were used as command-and-control servers, which received communications from, and returned instructions to, malware on other compromised computers.
14. The co-conspirators commonly used domain names to hide malicious communications to and from hop points and other victim computers. “Domain names” are labels used to indicate ownership or control of a resource on the Internet, and they are governed by the rules and procedures of the Domain Name System (“DNS”). Domain names resolve back to specific Internet Protocol (or simply “IP”) addresses, which are unique, numeric addresses assigned to computers to route traffic on the Internet.
15. The function of the DNS is to translate an alphanumeric domain name into an IP address of the computer hosting that domain; using the DNS is analogous to using a phone book to look up the phone number of a particular person. Typically, an Internet user attempts to navigate to a website using its domain name, but computers navigate to a website using an IP address. When a computer user types the domain “websitename.com” into a web browser, for example, the user’s computer contacts a DNS server, which then translates the domain name into an IP address, like “58.247.27.223,” and sends that IP address back to the user’s computer. The user’s computer can then immediately communicate directly with websitename.com, because it has identified the corresponding IP address. Dynamic DNS providers enable owners or operators of domain names to change the IP addresses to which the domain names resolve, usually by logging into domain accounts at the providers over the Internet and configuring the settings for the domain names to include the destination IP addresses.
16. The co-conspirators, either directly or through intermediaries, purchased, leased, or otherwise registered domain names from domain registrars, obtained accounts at dynamic DNS providers, and assigned the domain names to those domain accounts (if the domain names were not already assigned to the desired DNS providers as part of the original purchase, lease, or registration). Using those domain accounts, the coconspirators managed the resolutions of those domain names (that is, the assignments of those domain names to particular IP addresses on the Internet, to which lookup requests for those domain names would be directed). Often, those domain names were designed to mimic the domain names of legitimate websites, but with slight differences in spelling, such as “finaceanalysis.com,” “gmailboxes.com,” and “busketball.com.” The co-conspirators then used the domain names with their malware. After the malware was installed on victim computers, the domain names served as the destination points for the malware to contact, or beacon, for further instructions. The table below lists some of the other malicious domains used by the conspiracy during the period relevant to this Indictment:
Malicious Domain Names
arrowservice.net
bigish.net
businessconsults.net
businessformars.com
marsbrother.com
purpledaily.com
newsonet.net
comrepair.com
oplaymagzine.com
hugesoft.org
17. The co-conspirators used the domain accounts at dynamic DNS providers to assign their domain names to the IP addresses of different computers depending on their needs at the time. For example, when the co-conspirators wished to proceed with particular intrusions, they used the applicable accounts at dynamic DNS providers to turn malicious domains associated with their malware “on,” that is, to assign the domains to the IP addresses of computers under their control, like hop points. Then, between intrusions, the co-conspirators used the domain accounts to reassign the malicious domain names to non-routable or innocuous IP addresses (e.g., IP addresses for popular webmail services, like Gmail or Yahoo), which would obscure any beacons their malware sent during that period. At one dynamic DNS provider, for example, domains were typically turned “on” at the beginning of business hours in Shanghai, Monday through Friday, and turned “off” (reassigned to non-routable or innocuous IP addresses) at lunchtime and the close of business, and left off over the weekend, as the charts attached as Exhibit F to this Indictment show.
18. After obtaining a foothold in a victim’s computers, the co-conspirators performed a variety of functions designed to identify, collect, package, and exfiltrate targeted data from the victim’s computers to other computers under the coconspirators’ control.
THE CONSPIRACY’S INTRUSIONS AT SIX VICTIMS
Westinghouse
19. Westinghouse is one of the world’s leading civilian nuclear power developers, providing fuel, services, and plant design to customers in the commercial nuclear industry worldwide. The company’s designs are the basis for approximately half of the world’s currently operating nuclear power plants. Westinghouse’s AP1000 Nuclear Power Plant is a particularly well-known power plant design, with unique safety features, which took Westinghouse significant resources to develop over a 15-year period.
20. After two years of negotiations, on July 24, 2007, Westinghouse and SOE-1, a Chinese state-owned enterprise in the nuclear power industry, signed contracts for the construction and operation of four AP1000 power plants in China, subject to further negotiations on certain unresolved issues. Those contracts provided for the transfer of some technology to SOE-1, but they limited what SOE-1 was permitted to do with it. For example, SOE-1 was not authorized to send materials and components outside China, to use them in reactor plants that competed with Westinghouse’s products outside China, or to use them for military purposes. Further, the technology transfer contracts limited SOE-1’s ability to provide such technologies to entities other than those listed in the contracts without notifying and receiving approval from Westinghouse.
Negotiations regarding the other details, including additional technology transfer issues, continued for years thereafter, up to and including 2013.
21. During the conspiracy, while Westinghouse was building the AP1000 plants and negotiating other terms with SOE-1, hackers repeatedly targeted Westinghouse’s computers, including computers in the Western District of Pennsylvania. For example, on or about May 6, 2010, Defendant SUN gained unauthorized access to Westinghouse’s computers and stole proprietary and confidential technical and design specifications related to pipes, pipe supports, and pipe routing within the AP1000 plant buildings. Among other things, such specifications would enable a competitor to build a plant similar to the AP1000 without incurring significant research and development costs associated with designing similar pipes, pipe supports, and pipe routing systems. During the same intrusion, Defendant SUN also stole Westinghouse network credentials that would facilitate additional, unauthorized access.
22. In addition to constructing the AP1000 plants and negotiating contractual details relating to those plants, in late 2010, Westinghouse began to explore other business ventures with SOE -1. For example, in or about September 2010, Westinghouse and SOE-1 began negotiating over the construction of additional power plants in China. Westinghouse sought to conclude these negotiations before the arrival’ of an SOE-1 official in Washington, D.C., as part of a January 2011 Chinese state visit, so that the agreement could be signed during the visit. Meanwhile, Westinghouse management internally discussed what approach to take during upcoming negotiations and-in future partnerships with SOE-1, as well as the potential that SOE-1 may eventually become a competitor.
23. While these business initiatives and discussions were underway, beginning at least in or about December 2010 and continuing until at least in or about January 2011, Defendant SUN repeatedly targeted Westinghouse’s computers.
For example, on or about December 30, 2010, January 3, 2011, and January 5, 2011, Defendant SUN gained unauthorized access to Westinghouse’s computers and stole sensitive, non-public, and deliberative e-mails belonging to senior decision-makers responsible for Westinghouse’s business relationship with SOE-1, including Westinghouse’s Chief Executive Officer.
Some stolen e-mails described the status of the four AP1000 plants’ construction. Many other stolen e-mails, however, concerned Westinghouse’s confidential business strategies relating to SOE-1, including Westinghouse’s (a) strategies for reaching an agreement with SOE-1 on future nuclear power plant construction in China; and (b) discussions regarding cooperation and potential future competition with SOE-1 in the development of nuclear power plants elsewhere around the world.
24. In total, between in or about 2010 and in or about 2012, members of the conspiracy stole at least 1.4 gigabytes of data, the equivalent of roughly 700,000 pages of e-mail messages and attachments, from Westinghouse’s computers.
SolarWorld
25. At times relevant to this Indictment, SolarWorld had significant business interests relating to China, including as a direct competitor with various Chinese solar products manufacturers. Beginning at least in or about October 2011 and continuing until in or about September 2012, SolarWorld was particularly active in trade litigation involving Chinese manufacturers: it was the lead petitioner in a case before the U.S. Department of Commerce and U.S. International Trade Commission.
That litigation ultimately resulted in a finding that Chinese solar manufacturers had received unfair subsidies from China and had “dumped” large volumes of solar products into U.S. markets at prices below fair value. As a result, the Department of Commerce imposed significant countervailing and antidumping duties on Chinese imports of solar products.
26. On or about May 3, 2012, following one preliminary determination by the Department of Commerce and about two weeks before a second determination was scheduled, Defendant WEN hacked into SolarWorld’s computers and stole e-mails and files belonging to three senior executives.
Then, from on or about May 9, 2012 up to and including on or about September 26, 2012, Defendant WEN and at least one other, unidentified coconspirator conducted at least twelve more intrusions into and exfiltrations from SolarWorld’s computers. Through those intrusions, they stole thousands of e-mail messages and other files from at least seven identified SolarWorld employees who, based on their positions, would be expected to have comprehensive and highly detailed information about SolarWorld’s financial position, production capabilities, cost structure, business strategy, or trade litigation strategy.
27. Collectively, the data stolen from SolarWorld would have enabled a Chinese competitor to target SolarWorld’s business operations aggressively from a variety of angles. For example, the stolen data included: (1) cash-flow spreadsheets maintained by the Chief Financial Officer that would enable a Chinese competitor to identify the length of time that SolarWorld might survive a financial or market shock; (2) detailed manufacturing metrics, technological innovations, and production line information that would enable a Chinese competitor to mimic SolarWorld’s proprietary production capabilities without the need to invest time or money in research and development; (3) specific production costs for all manufacturing inputs that would enable a Chinese competitor to undermine SolarWorld financially through targeted and sustained underpricing of solar products; and (4) privileged attorney-client communications related to SolarWorld’s ongoing trade litigation with China, including confidential Question-and-Answer documents submitted to the Department of Commerce that were not discoverable by the Chinese respondents.
U.S. Steel
28. U.S. Steel is the largest steel company in the United States. During the period relevant to this Indictment, U.S. Steel had significant business interests relating to China, including as a competitor of several Chinese steel manufacturers like SOE-2.
For example, beginning at least in or about 2009 and continuing until at least in or about 2012, U.S. Steel participated in several international trade disputes with Chinese steel manufacturers, including SOE-2. These disputes involved allegations that China subsidized the Chinese steel industry and that the Chinese steel industry “dumped” steel into U.S. markets at below-market prices.
29. In or about 2010, U.S. Steel was particularly active in that litigation. That year, U.S. Steel was one of several lead petitioners in protracted litigations before the U.S. Department of Commerce and U.S. International Trade Commission involving imports of (a) oil country tubular goods (“OCTG”), which are steel piping used by oil and gas companies; and (b) seamless standard line pipes (“SSLP”), which are steel pipes specifically constructed without a welded seam down the length of the pipes.
In both cases, the Department of Commerce found that the respondents — various Chinese steel manufacturers including SOE-2 received unfair subsidies from China and “dumped” billions of dollars’ worth of steel into U.S. markets at prices below fair value. As a result, the Department of Commerce imposed significant countervailing and antidumping duties worth millions of dollars on Chinese imports of OCTG and SSLP. Thereafter, the amount of OCTG and SSLP steel imported by Chinese manufacturers fell dramatically.
30. In or about February 2010, while U.S. Steel was participating in at least the two international trade disputes described above, Defendants SUN and WANG hacked into U.S. Steel’s computers.
a. On or about February 8, 2010, approximately two weeks before the U.S. Department of Commerce was scheduled to release its preliminary determination in the SSLP trade dispute, Defendant SUN sent a spearphishing e-mail purporting to be from U.S. Steel’s Chief Executive Officer to approximately 20 U.S. Steel employees affiliated with the U.S. Steel division responsible for OCTG and SSLP. The e-mail contained a link to malware, which some of the recipients clicked on, installing malware on computers located in the Western District of Pennsylvania and providing Defendant SUN and his co-conspirators with backdoor access to U.S. Steel’s computers.
b. On or about February 23, 2010, Defendant SUN sent spearphishing e-mails purporting to be from two U.S. Steel e-mail accounts to approximately eight U.S. Steel employees, including U.S. Steel’s Chief Executive Officer.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.









