Category: Security
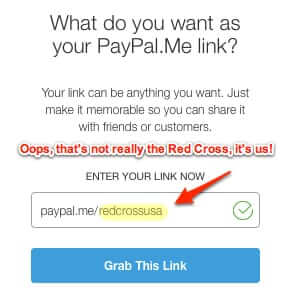
Paypal.me an Open Invitation for Scammers
The new Paypal.me service is being hailed as a simpler way to request money, and by Paypal as “the link to getting paid,” but it also turns out to be a great way for scammers to get you to send them money.
Ashley Madison Knew Security was Weak; Courts say Feds can go after Companies with Weak Security
Evidence in the form of leaked email demonstrates that Ashley Madison execs knew that their security was weak. A Federal court ruling last week says that the Federal Trade Commission (FTC) can go after companies whose Internet security is weak. Hrrm…
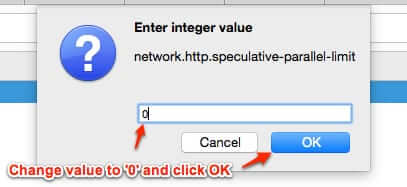
You NEED to Know about Firefox Speculative Pre-Connections and How to Disable It
Earlier this year Firefox ramped up its speculative pre-connections ‘feature’ (which some call “predictive preconnections”), so that when you even just hover over a link or thumbnail, Firefox may start preloading certain parts of the linked page (this is different from prefetching). Here’s how to disable it.
The Best Consumer Device for Secure Calls and Text Messaging
Wired’s Joseph Cox has a brilliant idea: what is the best, most readily available consumer device to use to make completely secure calls, and to use for secure text messages and secure chat? (Well, at least as secure and locked down as the average consumer can easily make them?) An iPod Touch! Brilliant! Here’s why.
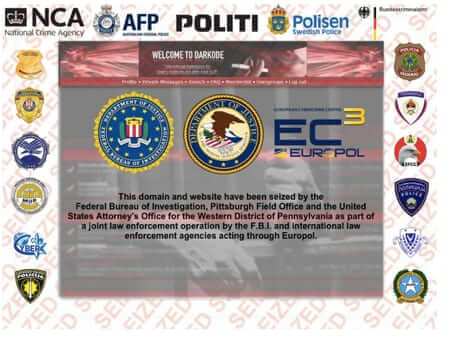
What the Darkode Cybercrime Ring Sting and Bust Means for You
Last month the U.S. Justice department announced the takedown of the Darkode (get it? DarkCode – Dark Code?) international cybercrime ring, which the DOJ called one of the “gravest threats” to the security of online data. But what exactly does that mean to you, the average user sitting at home behind your computer?
About the Jeep Hack and Hackers Hacking Cars and What to Do About It
By now you’ve probably heard about Andy Greenberg’s expose in Wired about driving a Jeep while hackers – wireless carjackers – hacked into it. Of course, Internet Patrol readers who read our Can Your Car Be Hacked Through its Onboard Wireless were probably not surprised by this turn of events, because they already knew that the answer to that question was “yes”.
FBI, Feds Want to be Able to Decrypt Your Encrypted Email and Messages
Both the Federal Senate Judiciary Committee and the Senate Intelligence Committee heard today from FBI Director James Comey, and from Deputy Attorney General Sally Quillian Yates, that they need a backdoor (or a “front door”, as Comey calls it) that allows them to decrypt encrypted email and messages in order to fight terrorism.
Hyatt Gold Passport Accounts Hacked
Hyatt Hotels, owners of among others the Hyatt Regency brand, has quietly announced that their Hyatt Gold Passport system has been hacked.
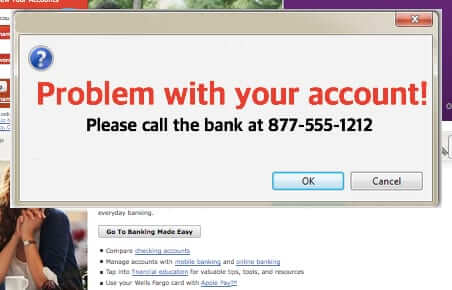
Dyre Wolf Wire Transfer Malware Gets Around 2-Factor Authentication
The Dyre Wolf phishing malware targets primarily businesses and organizations (rather than individuals). This is because it tricks the victim into giving up bank credentials, and then does a wire transfer. However it works by tricking individuals using social engineering, which is also how it gets around 2 factor authentication (2FA). Dyre Wolf is distinct from the dire wolf – Dyre Wolf is phishing malware, the dire wolf is an extinct member of the wolf family (and the direwolf is a mythical dire wolf featured in Game of Thrones).
Yes Hackers Really Do Hack Baby Monitors
It sounds like urban legend: “Hacker hacks video baby monitor web cam and screams at little girl.” But it’s true, and it happens more often than you think, primarily owing to people putting their baby monitors web cams online and never changing the default password.
What are the Odds that Your Hacked Personal Data Will be Used?
With massive security data breaches happening more and more frequently, there is almost no way to avoid your own personal data being compromised. But what is the likelihood that your compromised data will actually be used for identity theft, fraud, or financial theft? Here’s how it breaks down.
Sony Movie “The Interview” Hack and Terror Threat Explained
Here is what is going on around the Sony hack tied to Sony’s ‘The Interview’ movie, and the The Interview threat from the Sony hackers. The Interview, with a Christmas release date, sees Seth Rogen and James Franco’s characters going to North Korea to interview North Korean leader Kim Jong Un, and convinced by the CIA to take the opportunity to kill Kim Jong Un. Ahead of its release, hackers hacked into Sony, grabbed all sorts of private employee and corporate data, including copies of the movie and other unreleased movies including Annie, Mr. Turner, Fury, and Still Alice, and then issued the following threat, including allusions to 9/11.
Online Version of the Bush Cheney CIA Interrogation and Torture Report
Early today the Senate declassified and made public the Senate Select Committee Study of the Central Intelligence Agency’s Detention and Interrogation Program (or, as some are calling it, the Bush Cheney CIA Torture Report). We know that many of you will be looking for the CIA torture methods report online, and so, we are giving it to you here.
Urgent Microsoft Vulnerability Update Patch for All Versions of Windows
Microsoft has released a critical update to patch a “privately reported” Microsoft Secure Channel (“Schannel”) vulnerability which affects all current versions of Windows and Windows Server. Says Microsoft, “This security update resolves a privately reported vulnerability in the Microsoft Secure Channel (Schannel) security package in Windows.”
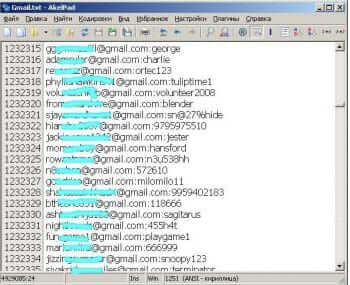
5 Million Gmail Addresses and Passwords Leaked – Should You Worry?
Outlets such as the Daily Dot and Life Hacker are reporting the leaking of five million Gmail addresses and passwords on a Russian Bitcoin forum.