Wired’s Joseph Cox has a brilliant idea: what is the best, most readily available consumer device to use to make completely secure calls, and to use for secure text messages and secure chat? (Well, at least as secure and locked down as the average consumer can easily make them?) An iPod Touch! Brilliant! Here’s why.
It was just a little over two years ago that Edward Snowden blew the lid off the NSA surveillance program, which revealed the depths to which government agencies were snooping on U.S. citizens as well as those from other countries.
And, of course, to nobody’s surprise, the NSA is also mining smartphone data.
And the NSA isn’t the only one. Law enforcement agencies across the country, and at all levels, love them some cellphone data, as demonstrated by the deployment around the country of the Stingray cell phone tower emulator, that grabs all sorts of data from your cell phone.
And don’t even get us started about Carrier IQ (CIQ)!
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
This has left the average citizen in something of a quandry. We know that there is all sorts of snooping and eavesdropping of our private calls and text messages going on, and even if you figure that you’re an unlikely target of covert snooping, you know that your records can be subpoenaed from your carrier (whether you as a ‘person of interest’ or caught up in a fishnet when they are looking for someone else).
Well, if you have above-average concern about this (by which we mean, actually care about it, as the vast majority of the cell phone using public seems not to), then Joseph Cox has a great idea for you.
In his Wired article The Most Secure Way to Communicate? An iPod Touch, Cox argues that “the most secure communications device available to anyone, anywhere, right now is the humble iPod Touch.”
And we agree that it is a fairly brilliant, in fact a so-obvious-why-didn’t-we-think-of-it, idea.
It makes perfect sense when you think about it.
- The iPod Touch has no onboard cellular network connection
- The iPod Touch can run just about any app that an iPhone can
- There are tons of proven encrypted messaging and/or calling communications apps for the iPod Touch
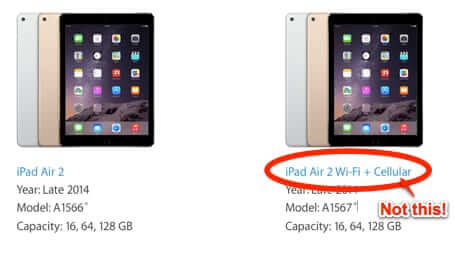
We would also add that this applies to the iPad as well. You just have to be sure that you are using a wifi only version, not one of the cellular-enabled models! (For the most part, iPod Touches are not natively cellular-enabled, but there are ways to make them so – you don’t want to do this. iPads do come in 3G and other cellular-enabled versions, so make sure you are using one that is wifi only.)
Once you have your device, Cox points out, it’s up to you to make it as secure as possible, by setting up a strong device password, keeping the OS fully up-to-date and updating with each security update as soon as it’s released, and by not using iCloud (read our article on how law enforcement doesn’t need a warrant to get your data if it’s stored in the cloud here) or any streaming or other apps that have lots of access to your personal data.
In fact, we would advise that you use this device only for your secure communications. The less you have on it, the less likely you are to be subjected to unexpected data mining on the part of any of the app makers.
Then it’s only a matter of choosing your encrypted communications apps. We have no one app in particular that we would recommend over another, but Cox does. In his article he comes out with a strong recommendation for Signal – and we recommend that you read his article to get the full skinny on why he recommends it.
Read Cox’ article The Most Secure Way to Communicate? An iPod Touch here.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.