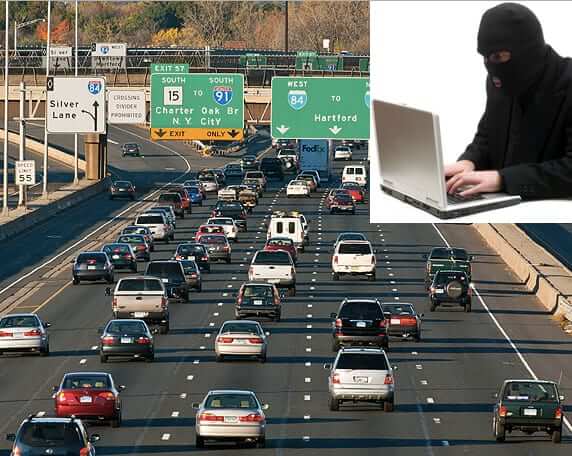
By now you’ve probably heard about Andy Greenberg’s expose in Wired about driving a Jeep while hackers – wireless carjackers – hacked into it. Of course, Internet Patrol readers who read our Can Your Car Be Hacked Through its Onboard Wireless? were probably not surprised by this turn of events, because they already knew that the answer to that question was “yes”.
As Greenberg explains it, he was driving at 70 miles per hour when “Though I hadn’t touched the dashboard, the vents in the Jeep Cherokee started blasting cold air at the maximum setting, chilling the sweat on my back through the in-seat climate control system. Next the radio switched to the local hip hop station and began blaring Skee-lo at full volume. I spun the control knob left and hit the power button, to no avail. Then the windshield wipers turned on, and wiper fluid blurred the glass.”
Then the two hackers responsible for the Jeep hack, Charlie Miller and Chris Valasek – who we should emphasize were doing this with Greenberg’s permission, specifically for the article and to prove the point – caused a picture of themselves to be displayed on the car’s display screen.
But wait, there’s more. Because they also managed to stop the Jeep’s transmission. At that moment, Greenburg was on a highway, heading up a hill, with a semi-truck bearing down behind him.
So how is this nightmare situation even possible?
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
Last year (2014) we told our readers about how General Motors stated that by this year (2015) many of their cars would have native onboard wifi hotspots. This means that your GM car will have an IP address!
And, according to Miller and Valasek, there is a security flaw that will allow anyone who knows a car’s IP address to access the car remotely, from anywhere, and attack the car, and take over and control those systems.
In fact, said Miller, in the Wired article, “From an attacker’s perspective, it’s a super nice vulnerability.”
And it’s not hard to take advantage of it. In fact Miller and Valasek are able to scan for other GM cars with UConnect and immediately determine where they are (onboard GPS coordinates), the make, model, vehicle identification number, and IP address, using a laptop tethered through a Sprint cell phone (UConnect uses the Sprint network, so – at least so far – you have to be on the Sprint network to see cars that have UConnect onboard).
Using this (relatively) low tech mechanism, they were able to find cars anywhere in the country. In fact, discovering that they could see cars anywhere in the U.S. freaked them out.
Said Valasek, “When I saw we could do it anywhere, over the Internet, I freaked out. I was frightened. It was like, holy fuck, that’s a vehicle on a highway in the middle of the country. Car hacking got real, right then.”
So what can you, the consumer, do about this?
Well the first thing is to be an aware consumer – when buying a new (or newer) car, be sure to find out before buying it if it has onboard wireless. And if it does, demand that it be turned off – if it can’t be turned off, don’t buy it. (Think that’s extreme? Do you think it’s more extreme than having a hacker turn your car off on the middle of the highway?)
If for some reason you simply must have a car with onboard wireless (although why you would have to is beyond us), be sure that it is up-to-date with all patches. For example, UConnect issued a [Page no longer available – we have linked to the archive.org version instead] shortly after Valasek and Miller revealed their findings.
Of course, what would be awesome would be if there would be enough of a consumer backlash that automakers would stop putting in stuff that consumers aren’t actually asking for, and that put consumers at risk.
If you want more information on this all, we highly recommend reading the full Wired article.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.









