Earlier this year Firefox ramped up its speculative pre-connections ‘feature’ (which some call “predictive preconnections”), so that when you even just hover over a link or thumbnail, Firefox may start preloading certain parts of the linked page (this is different from prefetching). Here’s how to disable it.
First, why did they add speculative preconnections to Firefox?
To improve load speed, and for your viewing pleasure.
Says Firefox, “Firefox will open predictive connections to sites when the user hovers their mouse over thumbnails on the New Tab Page or the user starts to search in the Search Bar, or in the search field on the Home or the New Tab Page. In case the user follows through with the action, the page can begin loading faster since some of the work was already started in advance.”
Well, that’s all well and good – except, as Techworm points out, it can use a lot of unnecessary data and, more importantly, can potentially pose a privacy and even a security risk.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
For example, says Techworm, “What if a link on which the user hovers on belongs to a malicious website which the user has no intent of visiting. Mozilla Firefox would send the users data to this site without discrimination causing huge privacy and security related problems.”
Some people have doubted that this is really happening, because they don’t see any indication of something happening while it happens – but that’s the insidiousness of it. Mozilla Firefox cops to it themselves, and explains how to disable it (but we explain how to do that, with pictures, below).
So, after updating Firefox recently, we checked this out, and sure enough, speculative pre-connection was enabled by default.
So, here’s how to disable it.
How to Disable Speculative (Predictive) Preconnections in Firefox
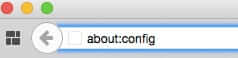
Go to your address bar in Firefox (the place where you type the web address (URL) of a site you want to go to), and type:
about:config
If you get a warning that says something like “This might void your warranty!” click on “I’ll be careful, I promise!”
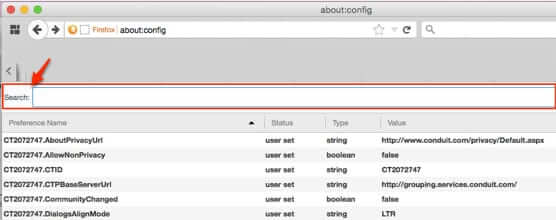
When you arrive at the about:config page, you’ll see a search bar at the top.
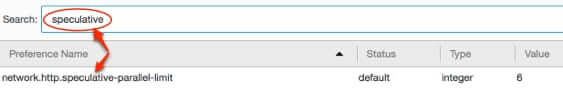
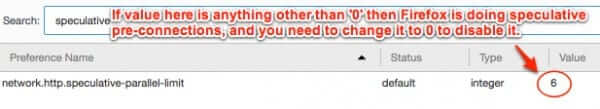
Type the word ‘speculative’ into the search bar, and the result will be the setting for the Firefox speculative preconnections ‘feature’, network.http.speculative-parallel-limit:
Now, if the value in the ‘Value’ column is 0, then it is already turned off, but if it is any other number, then your Firefox is performing speculative preconnections.
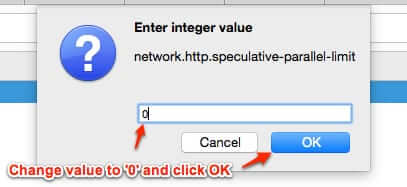
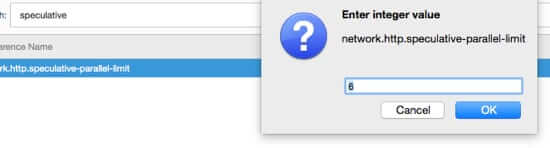
To change it, either hit ‘enter’ (‘return’), or double-click (either will work) and you will get a little window that allows you to change the value.
Change the value to ‘0’, and click on ‘OK’.
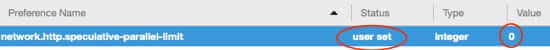
When you have successfully done this, the Value value will be 0, and the Status will have changed from ‘default’ to ‘user set’.
And that’s how to disable Firefox’ speculative pre-connections!
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.











Thanks for the heads up. about:config contains a mind-bobbling list of options.
In response to Kelson – I agree that it doesn’t do much, but what it does do takes time. Lots of time. I’m using FireFox. When browsing FaceBook, the further down the page I am the longer it takes for a hover (or a click) to react. Excluding speculative preconnection has reduced the delay – not to an acceptable level, but reduced nonetheless.
Thanks, again for helping us out. I was set on the speculative preconnection
It’s also important to understand what this *does* and *does not* do. It’s opening network connections, not making an actual HTTP request.
That means it’s not sending cookies, browser info, or anything of that sort. It’s not telling the server which URL you’re hovering over (or in the case of shared hosting, which site). It’s not producing an entry in the remote web server’s log. (Try hovering over links to your own site and watch the logs.) It’s not triggering action on a web-based application. It’s not retrieving any files.
A legit web server is not going to be tricked into action, thinking a hover is a click.
A malicious server is not going to get your cookies or browser info, or what page you were on, or what link you were looking at. It could get your IP address, or figure out what OS you’re using based on how your system makes the connection. If it actually does pre-negotiate SSL it might get a little more info on what kind of browser you’re using, or at least what SSL library it uses. And in that case, it’s not hard to imagine the impact of an SSL library vulnerability.
There’s still a case for telling it not to even open a connection. But it does a lot less that most people will think on reading the headlines.
Thanks for posting this. I didn’t know about it either. This is the first place I’ve seen it.
Great info. I did not know about the ‘speculative’ preconnection.
Thank you