Tag: Security
Millions of Iphones and iPads at Risk as Apple Rushes Security Update
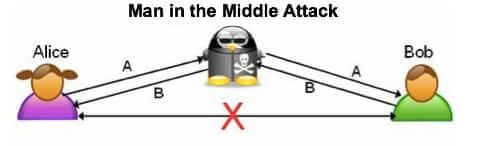
Apple has released a critical security update for iPhone and iPad iOS 7 and iOS 6. This urgent update is to fix the critical security vulnerability that exposes your data (including usernames, passwords, and other account credentials at nearly any website or service) to a “Man in the Middle” (MitM) attack.
Phone Number Reputation (“PhoneID Score”) Being Created Based on Two-Factor Authentication
It’s time to worry about your phone number reputation and mobile identity. The company that provides two-factor authentication for the users of sites such as Google and Facebook has been quietly amassing the phone numbers of those users, and is now assigning a phone number reputation, which it calls a PhoneID Score – or your Mobile Identity – to all of those phone numbers being used for two-factor authentication and, it seems, any other phone numbers the data for which they have access.
Concerns Voiced Over Possibility that Russians and Chinese May Already Have All of the Secrets that Edward Snowden Has in His Possession
Experts think that it is entirely possible that the Russians and the Chinese have already accessed the most confidential information that Edward Snowden has on his laptops.
Did You Get a “Warning: Please Slow Down” Captcha When Messaging Someone on Facebook?
The Facebook security check warning says “Warning: Please Slow Down. It looks like you’re using this feature in a way it wasn’t meant to be used. Please slow down, or you could be blocked from using it.” This is what some people are seeing when they try to send, or reply to, a message within the Facebook messaging feature. The only problem is, people who rarely send messages at all are seeing it.
Founder of Internet Security Company John Mcafee Using Internet Connections to Stay on the Lam in Belize Murder Case.
Do you know the name John McAfee? Well, if you have a PC with McAfee virus protection, then you just might. John McAfee is a computer programmer and the founder of the McAfee security software that just about anyone with a PC has already installed on their computers. McAfee is one of the first people ever to develop both an anti-virus software, and a virus scanner.
A Coffee Shop’s Plea to Customers Using Their Free Wifi – Stop Getting Our Wifi Suspended!
Many of us take free wifi at coffee shops for granted. Many, if not most – or even all – coffee shops now offer free wifi, and lots of people don’t give it a second thought before connecting to and using the free wifi. Some people even make a point of going to a coffee shop and using their wifi rather than using their own home wifi, particulary if they are going to do something of questionable legality. But even if you are not planning on doing anything illegal, certain actions on your part while logged onto the coffee shop’s wireless Internet could cause that coffee shop to have their Internet services suspended! Betcha never thought of that before, did you?
Massive Android Security Hole Affects up to 99% of All Android Users
Three researchers in Germany at the University of Ulm have discovered a massive security hole in Android – so big, in fact, that it affects at least 97%, and as many as 99%, of all Android users. The researchers, Bastian Könings, Jens Nickels, and Florian Schaub, have discovered that the security flaw allows anyone who is sniffing around your connection on an unsecured wireless network to acquire your Google authorization credentials from a specific token (the authToken), giving them access to your contacts, your calendar and, well – really any application that authenticates you by using your Google authorization credentials contained within that authToken.
List of Companies Affected by the Epsilon Data Breach
If you received a notice from one or another company with whom you do business or have done business in the past, saying that your email address has been compromised due to a data security breach at email service provider (ESP) Epsilon (due to their customers’ email lists being hacked and stolen), you’re not alone. Oh, you are so not alone. Banks, large merchants, and others, have all had their entire list of customers’ email addresses swiped and leaked due to the Epsilon data breach. Chase Bank, Citi Bank, Best Buy, Krogers – even Disney, have all been affected – as have their customers. Of course, lots of people receiving these notices will assume that they are phishing attempts (and there will undoubtedly be phishing attempts riding on the coat tails of this fiasco). Here is the complete list as we know it today – if you have received a notice saying that your email address has been compromised, please add the name of the company involved to the list here.
Gizmodo, Lifehacker, Gawker and other Gawker Media User Accounts Compromised in Security Breach
If you have ever had an account – even just to leave comments to articles and posts – on Gizmodo, Lifehacker, Gawker, Jezebel, io9, Kotaku, Deadspin, Fleshbot or Jalopnik, then you are in for a nasty surprise. Odds are good that your account has been compromised, and your user name and password posted on the Internet, as the result of security breach of Gawker Media’s servers that happened over the weekend. Gawker media does get points for alerting all of their users as soon as they discovered the breach (about 10 minutes ago as of the time of this posting on 6:20 p.m. PST on Monday, December 13th, 2010).
iPhone Owners at Risk for Their iPhone Joining Fake AT and T Hotspots
iPhones will join any old hotspot so long as it claims to be an attwifi hotspot, says a researcher who discovered the security hole this week. This security hole can lead unsuspecting iPhone users to give up all sorts of personal information to anyone who knows how to change the name of their wireless access point.
Microsoft Issues Urgent Windows Update to Protect Internet Explorer and Office Products
Microsoft has just announced an emergency patch for both Internet Explorer (IE) and Office Products, and it is recommended that everyone install this patch ASAP (link to patch included below). This affects Internet Explorer 6 (IE6), Internet Explorer 7 (IE7) and Internet Explorer 8 (IE8) as well as any Microsoft Office Product with ActiveX, including Microsoft Word, Excel, PowerPoint and Microsoft Access.
Palm’s Pres Spying on Palm Pre Users and Reporting Back to Palm
Holy privacy and security issue! A Palm Pre user who is also a securitygeekstud has discovered that Palm Pres (or should that be Palm Pri? Palm Prie? What is the plural of “Pre”?) are spying on Palm Pre users and on how they are using their Palm Pre, and reporting back to Palm!
Warning: Malware Exploits Norton Pifts.exe File – Trust Nobody But Norton! (Link Here)
Malware pushers have been quick to exploit confusion over a patch that was released yesterday by Norton Security for users of older versions of Norton. The patch was accidentally unsigned, which caused Norton to throw an error referencing the “pifts.exe” file. As a result, hords of Norton users have been searching Google for pifts.exe (or searching in their other favourite search engine for pifs.exe).
Emergency Windows Patch Issued by Microsoft – Get It Now!
Microsoft has gone outside their usual patch release schedule and has released an emergency patch which everyone running affected versions of Windows is urged to get and install immediately.
Study Proves Hotel Internet NOT Safe to Use
A new hotel network security study by Cornell University entitled “Hotel Network Security: A Study of Computer Networks in U.S. Hotels” has proven that using the wireless Internet – and even cabled Internet – at your hotel is almost always inherently insecure and unsafe.