Tag: malware
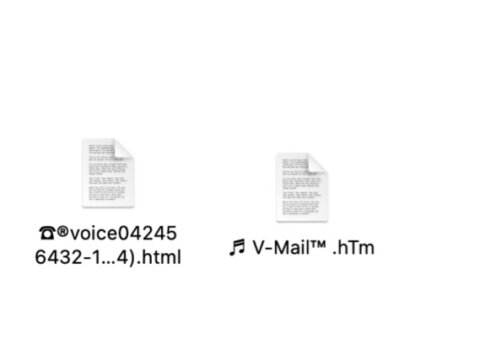
Don’t Open Any AudioFileWall V-Mail or ☎︎ Email Attachment: It’s a Trap!
Hello, 2019 called and wants their AudioFileWall (Audio File Wall) V-Mail “it says you have a voice mail but really it’s malware” spam back. Because that spam, carrying that malware, is back. Or at least carrying similar malware. Although some versions are actually voicemail phishing scams, meaning there is a real voicemail, telling you to call a certain number, or log into a certain account. Either way, delete with extreme prejudice!
The Cognizant Breach: What You Should Know About Maze Ransomware Attacks
Cognizant, an American company providing IT services based in Teaneck, New Jersey, is one of the latest victims of the infamous Maze ransomware. The IT services provider operating in more than 37 countries, with a turnover of $16bn, said the attack took place on Friday, April 17th. According to the…
Dance of the Pope Virus Warnings are a Hoax and Not True
Warnings going around Facebook warning about a video called Dance of the Pope that supposedly wipes your cell phone are themselves a hoax.
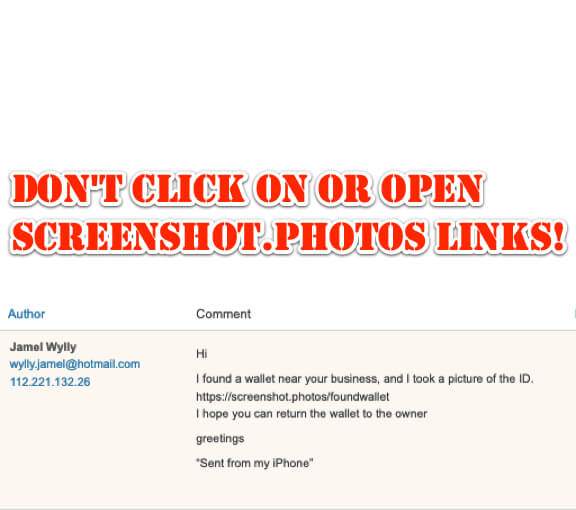
Don’t Click On or Open Screenshot[.]photos Links!
If out of the blue you get a message with a link to screenshot.photos in it, don’t click on it! It is a scam trying to get you to click on the link.
Memes Shared on Twitter Infected with Malicious Code
Memes. They’re cute. They’re funny. And they’re infected. That’s what researchers are saying about memes posted on Twitter from a particular account. The memes had commands embedded in their code, so that to look at the meme it looked normal, but when a computer infected with the particular malware encountered the meme, it would read the command and then execute it.
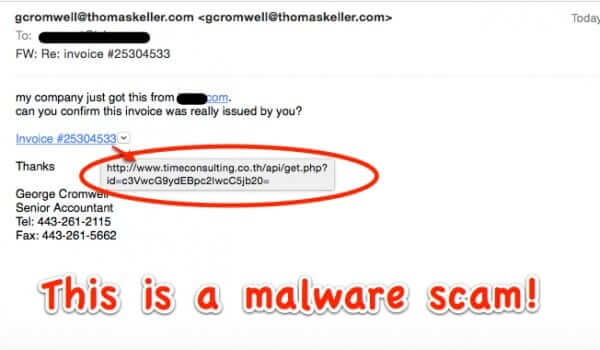
Do NOT Open Email Links from gcromwell@thomaskeller.com
A new malware scam is hitting email inboxes. The email sample that we have comes from an email address at thomaskeller.com (ours is specifically from gcromwell@thomaskeller.com), and claims to have received an invoice from your company. They even include your company name in the email, making it seem more legit. But it isn’t.
Nearly 100 Arrests Worldwide in Blackshades RAT (Remote Access Tool) Sting
The FBI and Department of Justice have jointly announced that over 90 people around the world have been arrested in a gigantic global takedown of those responsible for the Blackshades RAT (Remote Acccess Tool) malware – also known as “creepware”. In addition to arresting the Blackshades creator Alex Yucel (“Yücel” in his native Sweden), Yücel’s employees, including his marketing person, were arrested, as were customers who had purchased Blackshades and then used it against their own victims. Yücel’s partner and Blackshade co-creator Michael Hogue was arrested in a sting known as “Operation Cardshop” in 2012; Hogue’s arrest lead to the arrest of Yücel.
How Do I Know if I Have the Blackshades RAT on My Computer?
It is known that over 500,000 Windows computers worldwide are infected with the Blackshades RAT (Remote Access Tool) malware creepware. This means that if you have a Windows computer, or run Windows on your Mac, you need to check to see whether your computer has been infected with this silent privacy and security killer. The surest way is to check for any of the following files anywhere on your hard drive: dos_sock.bss, nir_cmd.bss, pws_cdk.bss, pws_chro.bss, pws_ff.bss, pws_mail.bss, pws_mess.bss
Beware the Flood of Boston Marathon Bombing and Texas Explosion Scam Emails
As was to be expected, there has been a massive swell of scam emails riding on the coattails of the back-to-back tragedies of the Boston Marathon bombing, and the Texas fertilizer plant explosion. “CAUGHT ON CAMERA: Fertilizer Plant Explosion” reads one bogus subject line; “Aftermath to explosion at Boston Marathon” reads another.
SuperClean and DroidCleaner: Android Malware That Jumps to Your PC and Infects Your Computer
If you are an Android user and have either of the apps called Superclean or DroidCleaner (AKA DroidClean), you are advised to remove them immediately to avoid malware jumping to your PC. The app, which has been removed from the app store, infects the computer with a virus that will open files, gather photos and obtain contact information.
Google Identifies 3.5 Million Malicious Sites Per Year (That’s 9500 New Malicious Sites a Day!)
Google is hard at work on a lot of things, including one of the most important and difficult things of all: improving Internet security. Five years ago, Google introduced Safe Browsing, an effort designed to protect Internet users – people who browse with Chrome, Firefox, or Safari, as well as anyone who searches the Web with Google – from malware and phishing. Through this effort, Google detects, among other things, 9,500 malicious sites every day. Allow us to repeat that: Google detects 9,500 malicious sites every day.
First Serious Mac Infection: Flashback Trojan
Up until now Mac owners have been relatively safe (and smug) when it came to the infectability of their computers. Worms, trojans, viruses, and other malware were considered to be primarily the domain of Windows. That may have changed last week, however, when the Russian security company, Dr. Web, reported that as many as a half a million Macs are already infected with what is being called the “Flashback Trojan”. Here’s how to know if you have Flashback Trojan, and how to get rid of Flashback Trojan.
Fatal Commerical Airplane Crash Caused by Computer Malware
Two years ago, almost to the day, a Spanish airliner belonging to Spanair crashed just after takeoff. Of the 172 people on board, 154 were killed. New information now reveals that one of the airplane’s central computer systems was infected with malware, and that the crash was likely directly attributable to this malware infection.