Category: Privacy
Walmart Looking to Offer Walmart-Branded Vizio TVs to Further Exploit Customer Data
Walmart is rumored to be looking to acquire smart television company Vizio (the potential deal is said to be around $2billion), so that they can enhance their own line of Walmart-branded television sets. Lest you think that this is simply an ego move on Walmart’s part, let us disabuse you of that notion right now: smart TVs are an incredibly rich source of consumer data – your data – just ripe for the mining.
AI Under Scrutiny: US Government to Monitor Foundation Model Developments
In a groundbreaking development that signals a shift in how artificial intelligence (AI) is managed at the national level, the US government, through the Defense Production Act, is setting up new measures to oversee the development of foundational AI models. This new directive, which requires AI powerhouses like OpenAI and Google to report their advances, brings the rapidly evolving field of AI under closer governmental scrutiny.
Google and the EU’s DMA
In a world where your every click, search, and scroll is a breadcrumb leading back to you, big players like Google hold more power than you might realize. It’s 2024, and Google is back in the news, this time for tweaking its online search results. Why? Well, it’s all thanks to the European Union’s new tech rules, the Digital Markets Act (DMA). These rules are like a referee in a game where Google’s been both a player and a scorekeeper.
The Incognito Illusion: Google’s Chrome and the Privacy Paradox
In a recent and quite revelatory turn of events, Google has conceded a point that privacy advocates have long suspected: even when you’re browsing in ‘Incognito’ mode in Google Chrome, you’re not quite as incognito as you might think. This acknowledgment comes in the wake of a $5 billion settlement to dodge a lawsuit from 2020, shining a spotlight on the often-misunderstood realm of digital privacy.
Facebook Meta Responds to Lawsuit Filed by 33 State Attorneys General Plus 9 More
Facebook parent company Meta has responded to a coordinated series of lawsuits (list of states and the complaint below) which include one filed in Federal court on behalf of 33 states and state Attorneys General, and 9 other related suits each filed in individual states in state court.
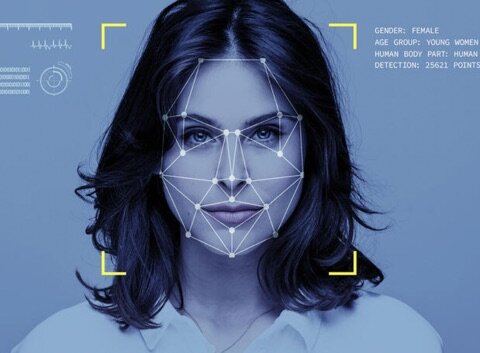
Clearview AI’s Benefits Not That Clear – Privacy Concerns Very Clear
Have you heard about Clearview AI, the “we can identify anyone who has a picture on the Internet” outfit? Privacy has emerged as a key concern in the era of technology’s ubiquity in our daily lives. Holding a controversial position in this ongoing debate is Clearview AI, a company specializing in facial recognition technology. Pledged to revolutionize law enforcement and security, Clearview AI has sparked apprehension over issues surrounding privacy and the invasive nature of surveillance.
Is Your Partner Cheating? These Online Loyalty Test Services Find Out for You
Worried that your partner is cheating on you? Now you can hire a loyalty tester who will put them to the loyalty test by coming on to them online. Maybe you’re here because you heard about the Loyalty Test service on Wait Wait Don’t Tell Me, Or maybe you’re here through a search for “is my partner cheating on me online?” However you arrived here, you’re probably here now because you’re curious about loyalty testing services that put your partner to the loyalty test by having a loyalty tester slide into their online private messages, whether on Instagram, Twitter, Facebook, or wherever they are online.
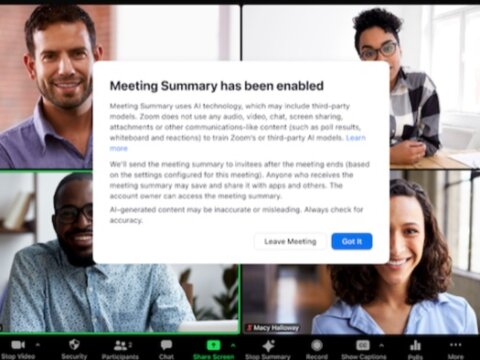
Zoom’s Dubious ToS Update: An Alarming Invasion of Privacy or Tempest in a Zoompot?
In an alarming move, video conferencing giant Zoom recently updated its Terms of Service (ToS), raising serious concerns about user privacy and data exploitation. The new ToS allows Zoom to collect and use your Zoom audio, video, and chat data to train its artificial intelligence (AI) algorithms. This update has raised eyebrows and sparked a debate regarding the true intentions of the company and the extent to which user privacy is being compromised and user data is being exploited.
Meta’s Grand Misstep: EU’s Top Court Decimates Legal Ground for Facebook’s Targeted Ads
This Independence Day was nothing short of explosive for Meta, and not in the festive sense. The tech behemoth, alongside its industry cohorts, got a shocking present from the European Union’s top court. The verdict? A full-frontal attack on the legal framework that supports Meta’s key business model of targeted advertising.
Meta Plans to Suspend News Distribution on Facebook and Instagram in Canada Amid New Legislation
In response to the passing of the Online News Act by the Canadian Senate, tech giant Meta, the parent company of Facebook and Instagram, announced it is preparing to cease the dissemination of news on these platforms within Canada. This decision arises in direct reaction to Bill C-18, a legislative piece that requires tech companies such as Meta and Google to negotiate agreements with news publishers regarding compensation for the usage of their content.
Update Your Apple Products ASAP
In an ongoing effort to secure its products against cyber threats, Apple has successfully addressed three new zero-day vulnerabilities that were under exploitation. These vulnerabilities, weaponized by cyber attackers, facilitated the installation of Triangulation spyware on iPhones using zero-click exploits in iMessage.
Elon Musk Encourages Twitter Spectators to Join the Conversation
In the ever-evolving world of social media, a significant portion of users are content to observe from the sidelines. However, tech billionaire Elon Musk, who now owns the popular microblogging platform Twitter, has a message for those who just can’t bring themselves to hit that ‘Tweet’ button.
The Inside Scoop on IP Addresses: Why You Should Care About Yours
IP address – ever stumbled upon this term? Perhaps you’ve spotted it in your computer settings or received an email warning about a login from an unknown IP address. Let’s make sense of this internet jargon and explore why it matters to you.
AI Explained in Plain English
In our rapidly advancing digital age, artificial intelligence (AI) is a buzzword you’re likely to encounter frequently. It’s a fascinating concept that’s sweeping the tech industry and society at large. But what exactly is it? Today, we’re going to demystify AI for you, clearing up misconceptions, discussing some genuine risks, and revealing what the future could hold.
Mind-Reading Technology Must Include Neurodivergent Individuals to Prevent Bias and Discrimination, Warns UK Data Watchdog
The development of mind-reading technologies raises concerns about potential discrimination and bias, according to the Information Commissioner’s Office (ICO) in the UK. The ICO is developing specific guidance for companies operating in the field of neurodata, as technology that monitors information from the brain and nervous system is expected to…