Law enforcement agencies have come up with a new tactic for investigating crimes: location-based warrants, served on Google, demanding that Google disclose Google accounts in use on all mobile devices that were in a given area at a certain time, thus giving detectives and other LEOs a pool of potential suspects and persons of interest who may have committed or have information about whatever crime they are trying to solve.
Think about this for a minute. All Google account IDs on all mobile devices in an area.
First, of course, there are all of the Android devices which are linked to Google accounts.
But even many, if not most (indeed, if not all) iOS devices have at least one app on them that has Google account credentials, be it Google Maps, Gmail, YouTube, Chrome, Google Search, Google Drive, Google Photos, Hangouts, Google Play, Google Calendar..you get the idea.
And so, the Google account information of many innocent people gets caught up in this extremely broad dragnet. In fact, pretty much anybody who happens to have been in, or even just passed through, the defined area at the time in question.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
Most recently, detectives in North Carolina have employed this technique in two different murder cases, an arson case, and two sexual assault cases. In each of the two murder cases, a person of interest was seen using a cell phone at or near the time of the murder.
In one case, after neighbors heard an argument and then gunshots, the suspect was seen using the flashlight on their cell phone to illuminate where they were walking.
In the other case, the suspect was caught on camera the day before the murder talking on their cell phone, and again was caught on camera right around the time of the murder.
In the latter case, according to Raleigh television station WRAL, Nwabu Efobi, a local taxi driver, was shot dead in the latter half of 2016. Says WRAL, “Security camera video caught Efobi in some kind of confrontation with the shooter before the unknown man opened fire. The day before, cameras caught the same guy several times walking around the building with what appeared to be a cell phone at his ear.”
Just a few months later, in March of 2017, investigators served a location-based warrant on Google, outlining a sector that included the murder scene, for the dates leading up to and when Efobi was shot.
As it turns out though, a suspect – one Tyron Cooper – was arrested in the Efobi case before the data was produced by Google. Of course if that data shows that Cooper (or, rather, Cooper’s device) was at the crime scene, that – while circumstantial – is rather damning (or prejudicial, depending on whether you are prosecuting or defending).
While in each of the murder cases there was a suspect, or at least a ‘person of interest’, either witnessed or captured on video, whom the police were trying to identify, in the other cases there was no suspect at the time of the warrants being issued. It was a fishing expedition.
In one of those cases, in 2017, Raleigh police served a search warrant on Google for all accounts that had been in the vicinity of a 5-alarm fire in which arson was suspected. The warrant, according to WRAL, requested “Google account IDs that showed up near the block of the Metropolitan between 7:30 and 10 p.m. the night of the fire.”
Observes WRAL, “The area just east of Glenwood Avenue is close to heavily trafficked bars, restaurants and apartments.”
In other words, the Google account IDs of countless restaurant patrons and apartment residents were delivered to the police.
In the sexual assault cases, a search warrant was served on Google which WRAL describes as “nearly identical to the arson investigation for any Google account IDs that appeared in either area within the timeframe of the crimes.”
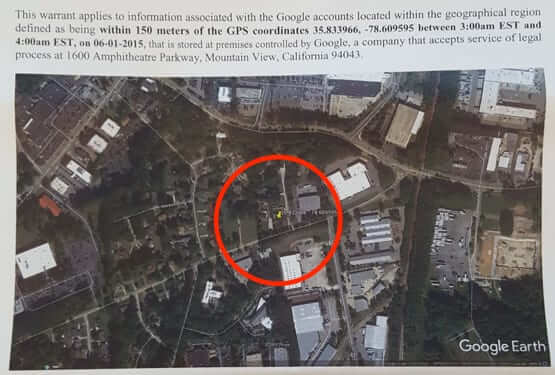
In order to convince a judge to issue the warrants, police printed out satellite images, and drew the boundaries of the crime scenes on the images, so that the judge could issue the warrant for those specific locations.
Actual image used in warrant application to convince judge to issue location-based warrant
That said, North Carolina officials don’t believe they should even have to get a warrant to force Google to give up the information about the Google accounts. A footnote in the warrants says “The State of North Carolina maintains that the information sought herein consists entirely of “record[s]” other than the “content of communications…” Such records, require only a showing that there are reasonable grounds to believe the information sought is relevant and material to an ongoing criminal investigation… Despite this, Google has indicated that it believes a search warrant, and not a court order, is required to obtain the location data sought in this application. Although the Government disagrees with Google’s position, because there is probable cause to believe the information sought herein will contain evidence of the criminal offenses specified in this affidavit, the Government is seeking a search warrant in this case.”
Warrants? We don’t need no stinkin’ warrants
Counters Google, “We have a long-established process that determines how law enforcement may request data about our users. We carefully review each request and always push back when they are overly broad.”
North Caroline law enforcement are not the only ones to be using this tactic. In 2017 a similar warrant was issued in Orange County, California.
Concerned?
You should be.
And, if you are concerned enough, you probably should turn off location tracking in all of your apps – or at least all of your Google apps. But we’re betting that you won’t, because convenience and fun seem to always trump concerns for personal privacy. Of course, the app makers and mobile carriers are betting on that too.
You can read the full warrant from one of the cases here.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.