That USB thumbdrive or flash drive that you have in your pocket may be a vector for all kinds of malware in the firmware, and once infected it cannot be fixed. In fact that’s true of any USB device, not just thumb drives. That’s the conclusion that Jakob Lell and Karsten Nohl, security researchers who have developed BadUSB, have reached.
The reason this is so urgent, and dire, say Lell and Karsten, is because there is the real potential that malware that ends up on your USB thumb drive will not be in a file that can be detected and deleted: it can persist in the very core of the USB drive, where it can infect any computer that it plugs into, which in turn will pass it on to any other USB devices that are plugged in to it.
To prove their point, Nohl and Lell developed BadUSB. BadUSB infects the firmware of the USB device, and will take over the computer to which it is connected, and alter files, and/or redirect the computer’s internet traffic, all undetected.
Once on a computer, it will also install itself on any other USB device that connects to that computer.
Because it resides within the firmware for the USB device, the average anti-virus software will not detect it, and even if all files are deleted off the USB device, it will persist.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
And because it infects the USB firmware, it can reside on any USB device, not just thumb drives. Any device that is driven by plugging it into your USB port can be infected with malware like BadUSB. That’s mice, keyboards, wifi dongles, you name it, if it plugs into your USB port it is at risk for being a vector for this sort of malware.
And, say Lell and Nohl, it is not simple to fix. In fact, an article in Wired on BadUSB suggests that the only way to address this is “banning the sharing of USB devices or filling your port with superglue.”
Says Nohl, “These problems can’t be patched. We’re exploiting the very way that USB is designed.”
“In this new way of thinking, you have to consider a USB infected and throw it away as soon as it touches a non-trusted computer,” adds Nohl.
Now remember, this is all at the “proof of concept” phase, meaning that Lell and Nohl had a theory, and now they have proven it with their own BadUSB code – no such malware has been discovered in the wild…yet. Also, as some argue, it may (or may not) be that the firmware can only be modified if it is upgradeable or otherwise writeable (this is open to discussion, and in fact just such a debate is going on in the comments to the Wired article).
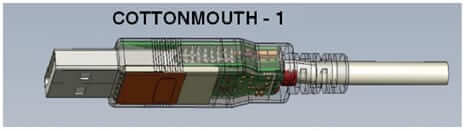
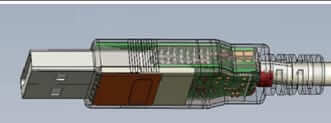
But if Lell and Nohl figured it out, you can be sure that others have or will. In fact, some believe that the NSA’s Cottonmouth USB device, which the NSA describes as “a Universal Serial Bus (USB) hardware implant which will provide a wireless bridge into a target network as well as the ability to load exploit software onto target PCs” may be exactly this sort of ware.
To address this would require that the manufacturers of USB devices start code-signing their USB devices. In this case code-signing would look like the trusted manufacturers and vendors embedding a cryptographic code in their firmware so that your computer can confirm that the only code on your USB device is code that should be there, from trusted sources.
Unless and until that happens, it turns out that plugging a USB drive or other USB device into an untrusted computer is a bit like having unprotected sex, where either the computer or the USB drive can become infected, and once infected, your USB drive can never get rid of it.
Kind of like computer herpes.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.