Members of USAA insurance and banking programs have been receiving email that appears to come from USAA (which stands for United Services Automobile Association), but which are actually phishing scams. The scam email comes from the nonexistent domain usaaservice.com (such as from “USAA.ServiceAccount@usaaservice.com”).
While it is unclear when and exactly how the scammers obtained the email addresses of the members, and we could find no announcement of USAA being hacked, USAA members have been complaining of being hacked over on the USAA member forums.
So far, most of the complaints have been of USAA member debit card and bank accounts being impacted (with some members saying that their accounts were wiped out), and in at least some cases the criminals had in their possession all of the credentials necessary to appear to be the account holder and to get full access.
– [destination content has been removed at other end :~( ]
The spoof email from USAA appears to come from “USAA.ServiceAccount@usaaservice.com” (the real USAA sends from “usaa.com” – the domain usaaservice.com doesn’t actually even exist as of the time of this writing), and the samples we’ve seen bear the subject line “Member Service Mail Alert”.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
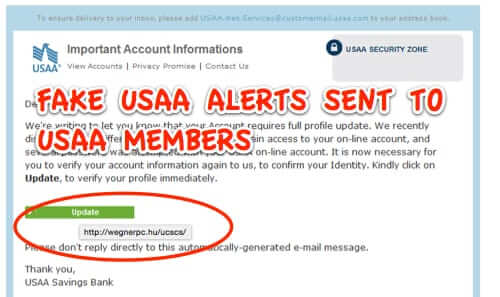
But perhaps the most immediately telling thing about this scam email is that it contains no text at all, it’s just one big image (legitimate companies never – or at least should never – do that).
Here’s what it looks like:
Looks pretty legitimate, doesn’t it?
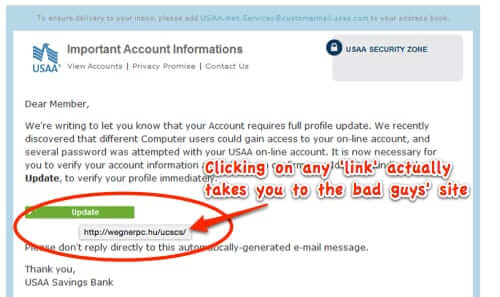
But here’s what happens when you hover over any part of the image – including the “links”, which they want you to click:
Of course, wegnerpc.hu is the scammers’ site. (.hu is the top level domain for Hungary.)
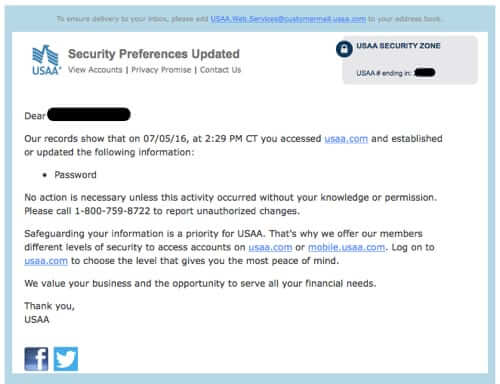
Here’s what an actual USAA notice, which will come from a subdomain with usaa.com as the primary domain, such as customermail.usaa.com or mailcenterusaa.com, looks like:
As is always, always the case, when you get an email from a company asking you to log in to your account, always, ALWAYS go directly to the site in your browser and log in, instead of clicking on any links in the email.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.










I recently also received an email asking me to go to a site to update my info…
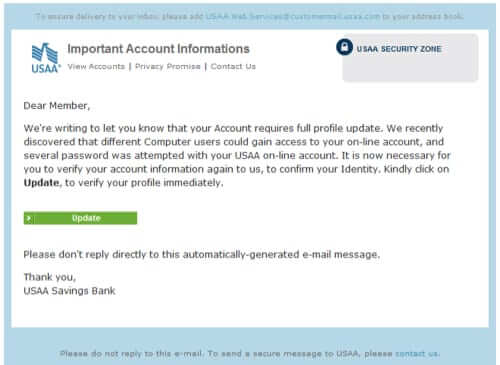
There are other features of that phishing message that betray its nature.
Firstly, the message does not address the recipient by name, or in any other way identify the account that has supposedly undergone suspicious activity.
Secondly, the pretext doesn’t make sense. Messages that describe (successful or unsuccessful) logins say something along the line of “If you performed this action, no further action is required of you. If not, let us know.” Making the customer log in will not help characterize the previous, unsuccessful login attempt.
Thirdly, if login attempts failed, that contradicts the statement that different users could access the account.
Thirdly, in at least four places the grammar is erroneous or clumsy. This is a situation in which the grammar that we learned in school is useful.
I actually received that email but deleted it as I don’t bank with USAA, but it looked fairly legitimate. Good article.