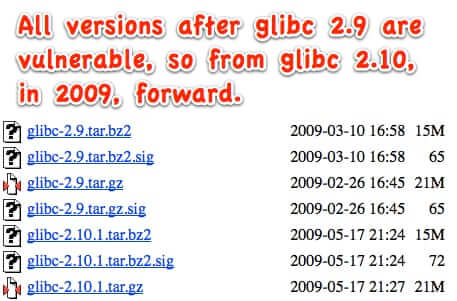
By now you have probably heard about the enormous security flaw that was recently discovered that, experts say, left thousands of applications and devices vulnerable to remote attacks and control. It is a flaw that has been around since 2009, and has the potential to affect any server that is running any post-2008 version of the Gnu C open source library called glibc. It is the function getaddrinfo() within the glibc library that has the flaw, and it is so widely distributed that it is impossible to estimate just how many applications and hardware installs are running the flawed versions (of which there are at least 7 main version and dozens of incremental update versions).
getaddrinfo() is the function used by software and devices that do domain lookups (think “DNS queries”). Which would be, well, a whole lot of programs and hardware.
Arstechnica calls it “a potentially catastrophic flaw in one of the Internet’s core building blocks,” and they’re right.
Fortunately, as soon as it was brought to their attention, the maintainers of the glibc library released a patch, which you can find here: Patch to fix the glibc library getaddrinfo() buffer overflow vulnerability
Unfortunately, while applying the patch will be relatively simple for those who actually run servers with the affected software, and know what they’re doing, the glibc library has been compiled into countless apps and software distributions, meaning that end users are using programs and apps containing the affected glibc, and will be unable to do anything about it. They will be stuck waiting for the software providers to recompile the software and release an updated version with the patched glibc library.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
All that said, if you have websites or other Internet-related services that are hosted at an Internet service provider, your Internet service provider should be taking care of this for you.
As one Internet service provider, LiquidWeb, advised their customers:
A vulnerability has been discovered via a stack-based buffer overflow that was found when libresolv libraries perform dual A/AAAA DNS
queries. This could, potentially, allow a remote attacker to create a
specially crafted DNS response, gaining permissions of the account owner
and enabling them to execute malicious code. The potential exploit of
the GNU C Library (glibc) was recently discovered and has been assigned
CVE-2015-7547.Liquid Web package repositories have been updated and managed servers
(barring those with updates disabled) will get an automatic update that
patches this vulnerability. A reboot will still be required in those
cases in order to ensure all potential threats have been neutralized. If
you are receiving this message, our records indicate that you may still
need to ensure that you have a patched update and/or take action to
reboot at your earliest convenience. In order to ensure the peak
security of our customers, we will be proactively patching and
initiating reboots on February 18th (2016) at 10:00PM (EST) for all
remaining vulnerable servers that we can access.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.










” has the potential to affect any server, be it Linux, Windows, or something else, that is running any post-2008 version of the Gnu C open source library called glibc”
Arguably true in its full conditional sense, however just about the only systems that actually use glibc are most (but not all) versions of Linux and a handful of niche/experimental systems. Not AT&T or OSF/1-derived commercial Unices, not Windows (not even the Cygwin layer that supports running most Linux software on Windows) not Mac OS X, not any of the BSD family (except for Debian’s experimental forks which are barely functional.) If *anything* on Windows uses glibc, it would need to be a rare bit of software, since Windows has long had its own implementations of the POSIX interfaces that glibc provides, largely descended from a BSD ancestry. Note also that the most common place where average users have Linux doing direct DNS resolution for them is in small routers and WiFi access points, which in most cases are members of that minority of Linux systems which DO NOT use glibc.
One reason this vulnerability is getting so much freak-out response is that Linux is unusually popular in the IT security community as a personal computing platform and dominant as a platform for security-oriented infrastructural software.
Beyond the fact of this being a risk for the personal laptops and desktops of infosec professionals and the mostly-unseen servers they work with, this flaw is disturbing because its most vulnerable targets are Internet-facing (SMTP) email servers running Linux, which do quite a lot of name resolution using their system resolver functions and often can be made to resolve specific arbitrary names by anyone who can send a piece of email. This sets them apart from web servers, which typically do very little name resolution outside of their own and a few related and trusted domains, or caching/recursing DNS servers which do a lot of name resolution of unfamiliar names but in nearly all cases use specialized resolver functions implemented in the DNS server software rather than the glibc functions of the system resolver. Email is over-trusted and email servers are under-attended, so a flaw that *MIGHT* be exploitable to quietly gain control of email servers is a bit of a nightmare.