Tag: warrant
Geofence Warrants and Google’s Huge Sensorvault Location Database Provide Law Enforcement with Lists of All People Near a Crime Scene
While in the news currently, geofence warrants (also referred to as ‘geo-fence warrants’) are nothing new (and our article includes a real example of a geofence warrant). We first wrote about geofence warrants and how Google is providing law enforcement agencies with lists of devices it has identified as being in the area of a crime scene at the time of the crime almost exactly 3 years ago to the day. Once serving the geofence warrant, and receiving the data from Google’s massive device location database called Sensorvault, law enforcement agencies can then create lists of possible suspects and witnesses, all based on their knowing that the person was simply in the area, based on the tracking of their device.
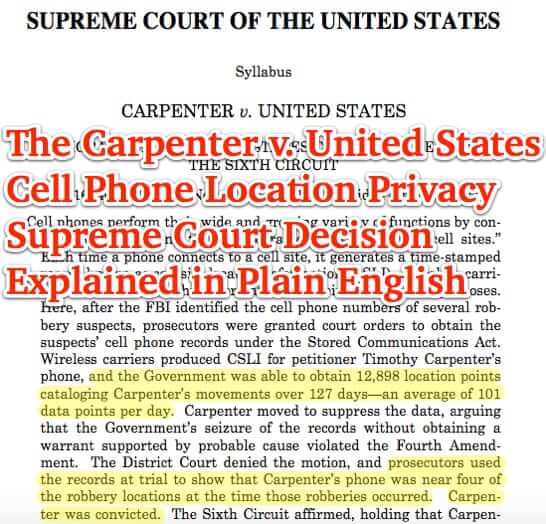
The Carpenter v. United States Cell Phone Location Privacy Supreme Court Decision Explained in Plain English (plus link to full text of decision)
In a fairly stunning win for mobile phone privacy, the Supreme Court has ruled that law enforcement agencies must obtain a warrant before they can demand and receive from mobile carriers and mobile providers access to the cell phone location data (known as ‘cell site location information’, or CSLI for short) of a given cellular phone. In the case of Carpenter v. United States, the Supreme Court held that tracking a cell phone is barely different than putting an ankle bracelet on an individual and monitoring their movements, and so overturned related case law that has been around for (up to) decades.
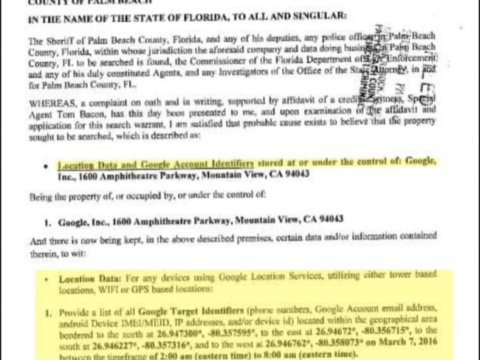
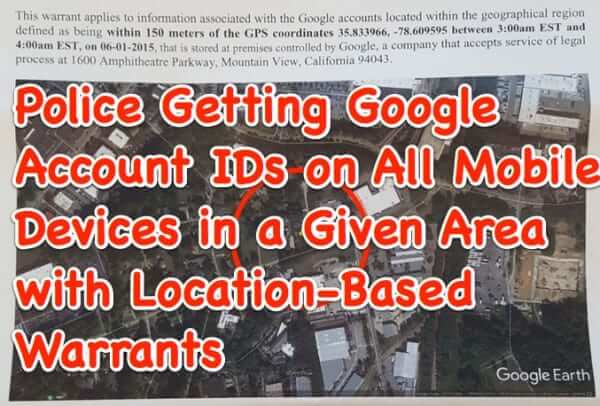
Warrants for Google Account Info on All Mobile Devices in a Given Area Now Being Served on and Responded to by Google
Law enforcement agencies have come up with a new tactic for investigating crimes: location-based warrants, served on Google, demanding that Google disclose Google accounts in use on all mobile devices that were in a given area at a certain time, thus giving detectives and other LEOs a pool of potential suspects and persons of interest who may have committed or have information about whatever crime they are trying to solve.
U.S. House of Representatives Passes Email Privacy Act
For more than four years we have been telling you that law enforcement can get to any electronic communications you have stored for more than 180 days in the cloud (and that ‘cloud’ is just a fancy word for “somebody else’s computer”). This is because the Electronics Communication Privacy Act (ECPA) only requires a subpoena in order for a governmental agency to get at those communications records that you have stored on that third-party server – they do not need a warrant.
FBI, Feds Want to be Able to Decrypt Your Encrypted Email and Messages
Both the Federal Senate Judiciary Committee and the Senate Intelligence Committee heard today from FBI Director James Comey, and from Deputy Attorney General Sally Quillian Yates, that they need a backdoor (or a “front door”, as Comey calls it) that allows them to decrypt encrypted email and messages in order to fight terrorism.
The Supreme Court Cell Phone Search Decision in Riley in Plain English
Today the Supreme Court unanimously held that a warrant is required to search a cell phone, in the case of Riley v. California. Warrentless searches of a cell phone are not ok.
Microsoft Fights Federal Warrant to Access Email Data in Ireland
Yesterday we told you about how Microsoft is one of several companies who are encrypting their services and hardening their systems against the prying of nosy agencies like the NSA. Now Microsoft is fighting a Federal court order that they turn over the data for a user’s email account whose email data resides on a server outside of the U.S. (in Ireland, to be specific).
Google Reveals Law Enforcement Requests
Google is making clear how they will be handling warrants and subpoenas for users’ personal information. With January 28th being Data Privacy Day, Google Senior Vice President and Chief Legal Officer, David Drummond, shared three initiatives on the Google blog, which detail how Google plans to protect user privacy when faced with a warrant or subpena to hand over private user information.
Senator Patrick Leahy and the ECPA Privacy Amendment That Proposed Only a Subpeona, With a Warrant Not Required, to Search Private Email
Update: We have just learned that Senator Leahy has withdrawn his support for the amendments to the Electronic Communications Privacy Act (ECPA). He received resounding criticism from many groups and private citizens who felt that the revisions are unconstitutional and a gross invasion of privacy. In a series of tweets, below, Senator Leahy said that he did not support the bill amendments, and seems to deny that he ever did.
No Warrant Necessary for Law Enforcement to Access Data Stored in the Cloud
With the recent decision in the Fricosu case, ruling that one can be forced to provide the password to your encrypted hard drive, you may be thinking it is better to store things “in the cloud”. In fact, it can be worse, as cloud storage currently requires no warrant for law enforcement to access any of your data which has been stored in the cloud for at least 180 days.
Police Execute Warrant, Seize Gizmodo Computers Over iPhone 4G Brouhaha
From our “We told you so” department, San Mateo County sheriffs have executed a warrant, seizing computers and other items from Gizmodo editor Jason Chen’s residence, following the appearance of a lost secret iPhone 4G prototype both in Gizmodo’s possession, and on their blog, where they fully disclosed Apple’s proprietary prototype. Jason Chen was not arrested, although he was patted down.