Tag: risk
Got the “Earnings at risk – You need to fix some ads.txt file issues to avoid severe impact to your revenue” Warning? This May be Why
Did you get the “Earnings at risk – You need to fix some ads.txt file issues to avoid severe impact to your revenue” pink stripe of death in your Adsense account (or do you want to know how to remove a domain or site from Adsense)? Read on.
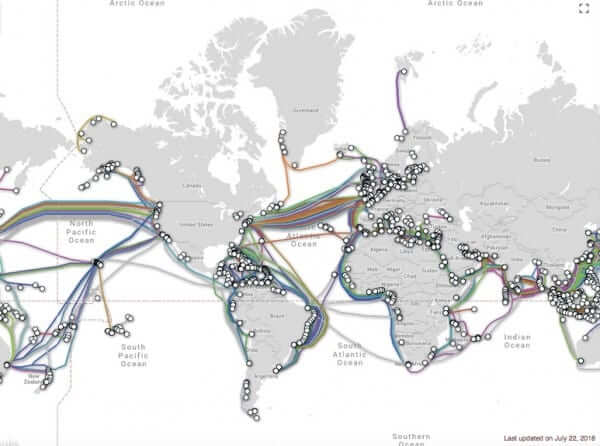
Scientists Say Much of U.S. Internet in Serious Jeopardy from Rising Sea Levels
Computer scientists at the University of Wisconsin and the University of Oregon have determined that the United States’ Internet infrastructure is at serious risk of being flooded owing to the rising sea levels. According to Paul Barford (UW) and Ramakrishnan Durairajan (UO), this is because much of the land-based underground fiber optic cabling through which the Internet is carried is in shallow underground trenches along the coasts.
Computer Users Urged to Disable Java Because of Security Flaws
The U.S. Department of Homeland Security alerted users of Java to a serious and urgent security risk, recommending that users disable Java until a suitable fix has been released. In the statement, the United States Computer Emergency Readiness Team (US-CERT), the branch of the federal government that manages computer security risks, warned that any system using Oracle Java 7 (1.7, 1.7.0) including Java Platform Standard Edition 7 (Java SE 7), Java SE Development Kit (JDK 7) and Java SE Runtime Environment (JRE 7) are at risk.
Massive Android Security Hole Affects up to 99% of All Android Users
Three researchers in Germany at the University of Ulm have discovered a massive security hole in Android – so big, in fact, that it affects at least 97%, and as many as 99%, of all Android users. The researchers, Bastian Könings, Jens Nickels, and Florian Schaub, have discovered that the security flaw allows anyone who is sniffing around your connection on an unsecured wireless network to acquire your Google authorization credentials from a specific token (the authToken), giving them access to your contacts, your calendar and, well – really any application that authenticates you by using your Google authorization credentials contained within that authToken.