Tag: Privacy
Walmart Looking to Offer Walmart-Branded Vizio TVs to Further Exploit Customer Data
Walmart is rumored to be looking to acquire smart television company Vizio (the potential deal is said to be around $2billion), so that they can enhance their own line of Walmart-branded television sets. Lest you think that this is simply an ego move on Walmart’s part, let us disabuse you of that notion right now: smart TVs are an incredibly rich source of consumer data – your data – just ripe for the mining.
The Incognito Illusion: Google’s Chrome and the Privacy Paradox
In a recent and quite revelatory turn of events, Google has conceded a point that privacy advocates have long suspected: even when you’re browsing in ‘Incognito’ mode in Google Chrome, you’re not quite as incognito as you might think. This acknowledgment comes in the wake of a $5 billion settlement to dodge a lawsuit from 2020, shining a spotlight on the often-misunderstood realm of digital privacy.
Google’s $5 Billion Privacy Settlement
In yet another chapter of the ongoing saga of tech giants and their questionable privacy practices, Google finds itself settling a $5 billion privacy lawsuit. This lawsuit revolves around Google’s alleged tracking of users in Chrome (and other browser’s) “incognito” mode, a practice that we’re sure is continuing unabated.
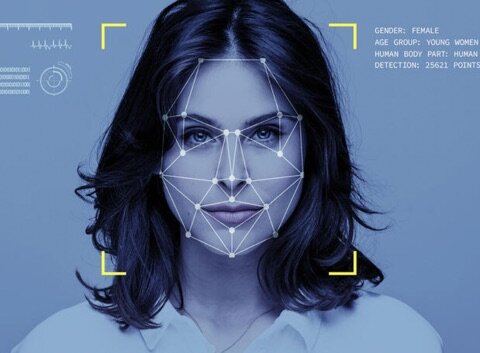
Clearview AI’s Benefits Not That Clear – Privacy Concerns Very Clear
Have you heard about Clearview AI, the “we can identify anyone who has a picture on the Internet” outfit? Privacy has emerged as a key concern in the era of technology’s ubiquity in our daily lives. Holding a controversial position in this ongoing debate is Clearview AI, a company specializing in facial recognition technology. Pledged to revolutionize law enforcement and security, Clearview AI has sparked apprehension over issues surrounding privacy and the invasive nature of surveillance.
Amazon Ring Doorbell Footage Shared With Police Without User Consent
Amazon was caught red-handed, handing over Ring doorbell footage to law enforcement agencies without user permission, subpoenas, warrants, without any of the traditional legal controls which prevent liberal disclosure of non-public data to law enforcement. This disclosure was set to further ignite ongoing debates about privacy and civil liberties in relation to the tech giant’s video-sharing agreements with police departments nationwide.
Concerns Raised Over Privacy Breach as Suicide Hotline Websites Transmit Sensitive Data to Facebook
In a worrisome revelation, dozens of mental health crisis center websites across the United States, which are designed to ensure the anonymity of users, have been discovered to discreetly transfer sensitive visitor data to Facebook, according to an investigation by The Markup. These websites, linked to the national mental health crisis 988 hotline, reportedly transmit user data through a tool known as Meta Pixel. This breach of privacy, particularly significant given the sensitive nature of the data involved, exposes users in critical emotional states to potential data misuse.
Report Highlights Scary New iOS Exploit via iMessage, Putting iPhone Security at Risk
Digital security firm Kaspersky has posted information about a recent cyberattack that targeted the iPhones of Kaspersky employees, which were infected with spyware that is part of a campaign the company dubbed, “Operation Triangulation.”
UK Government Silently Intensifying Controversial Web Surveillance Measures
In what is seen by many as an alarming move, the UK Government has been discretely expanding a contentious surveillance technology with the potential to log and store the internet histories of millions of individuals.
UK Government Silently Intensifying Controversial Web Surveillance Measures
In what is seen by many as an alarming move, the UK Government has been discretely expanding a contentious surveillance technology with the potential to log and store the internet histories of millions of individuals.
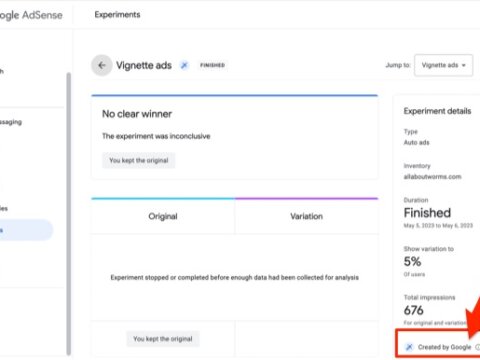
Adsense Revenue Down? This May Be Why: Adsense Experimenting on Your Site without Your Knowledge
Adsense revenue down? Google may be conducting Adsense experiments on your site without your knowledge. It’s enough to have you look for Adsense alternatives and close your Adsense account! Imagine our shock at finding that Google was experimenting on our site by placing experimental Adsense ads on our site without our knowledge or, as far as we can tell, permission.
Facebook: Getting Too Close and Personal
In a bold move that is stirring concerns over user privacy, Facebook has reportedly been granted a patent that suggests a desire to observe its users covertly through their webcam or smartphone camera. The technology aims to discern your mood as you interact with the platform, thereby serving tailored content or advertisements that align with your emotions. The somewhat intrusive concept involves analyzing people in real time via their camera as they browse online. The system is designed to identify emotions such as happiness, boredom, or sadness, and deliver advertisements that correspond with your current mood. For instance, if you’re feeling down, the technology could serve an ad designed to uplift your spirits or present products you’ve previously browsed when the timing feels just right. According to the patent application, Facebook’s system could determine user preferences based on their reactions to specific content.
Encryption: Why It Matters to You, Even If You Think You Have ‘Nothing to Hide
Have you ever wondered how your sensitive information stays secure when you’re shopping online or sending a private email? The answer lies in something called encryption, a complex system of coding that disguises your data to keep it safe from prying eyes. Some might argue, “I have nothing to hide. Why should I care about encryption?” Well, the truth is, encryption is critical for everyone, and here’s why.
BigTech is Inherently Unable to Provide Privacy
Let’s face it, big tech companies have a love-hate relationship with our privacy. On one hand, they assure us that our data is safe and secure. On the other hand, they make their fortunes by collecting, analyzing, and selling our data to third-party advertisers. It’s a classic case of mixed signals, and it’s not surprising that many people are skeptical about trusting big tech companies with their private communication.
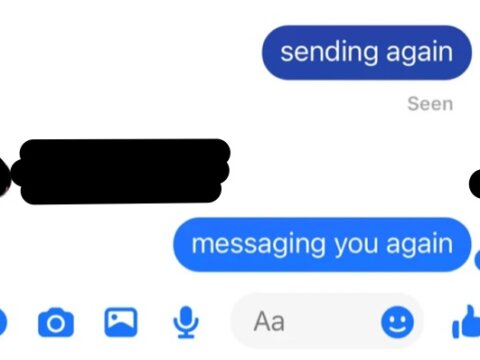
Facebook Messenger Read Receipts Huge Risk for the Abused, Bullied and Stalked
Facebook enables abusers. And they know that they do it. In a world full of online stalking, cyber bullying, and intimidation of the abused and traumatized, the fact that Facebook has never given users the ability to turn off Facebook Messenger read receipts may be one of the most egregious hand-offs of power to abusers ever to be perpetrated by a social media platform.
Google Paying $29.5 Million To Settle Lawsuits Over User Location Tracking
Google has agreed to pay a total of $29.5 million to settle two lawsuits regarding the company’s geographic tracking of their users.