Tag: location
How to Change or Reset Your Country Location for Your GoDaddy Account
If GoDaddy has changed the country in which they have your account located, and you are looking to set or reset it to the correct country, here’s how.
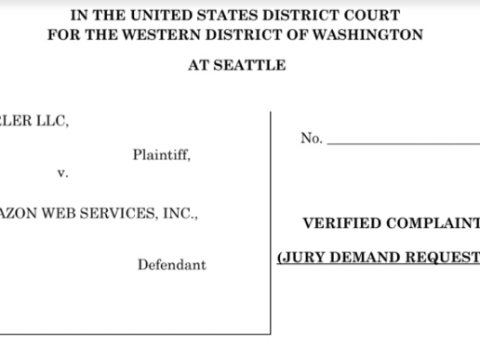
Parler Shut Down but Not Before Massive Data Scrape of its Users and Their Posts, Videos and Pictures
As Parler sues Amazon for shutting them down, more than 70 TB of identifying Parler user data revealed to have been grabbed and archived.
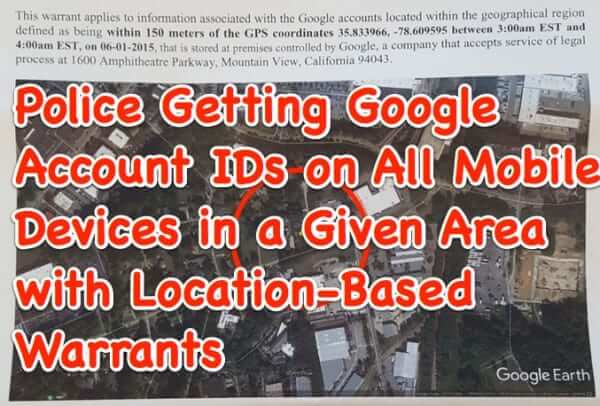
Geofence Warrants and Google’s Huge Sensorvault Location Database Provide Law Enforcement with Lists of All People Near a Crime Scene
While in the news currently, geofence warrants (also referred to as ‘geo-fence warrants’) are nothing new (and our article includes a real example of a geofence warrant). We first wrote about geofence warrants and how Google is providing law enforcement agencies with lists of devices it has identified as being in the area of a crime scene at the time of the crime almost exactly 3 years ago to the day. Once serving the geofence warrant, and receiving the data from Google’s massive device location database called Sensorvault, law enforcement agencies can then create lists of possible suspects and witnesses, all based on their knowing that the person was simply in the area, based on the tracking of their device.
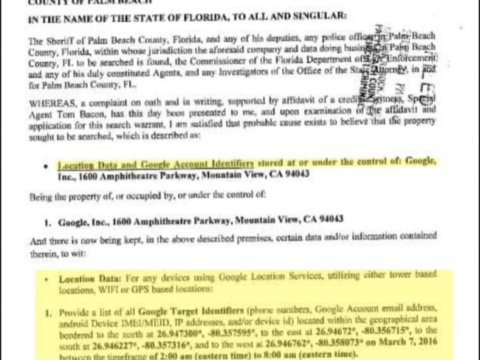
Warrants for Google Account Info on All Mobile Devices in a Given Area Now Being Served on and Responded to by Google
Law enforcement agencies have come up with a new tactic for investigating crimes: location-based warrants, served on Google, demanding that Google disclose Google accounts in use on all mobile devices that were in a given area at a certain time, thus giving detectives and other LEOs a pool of potential suspects and persons of interest who may have committed or have information about whatever crime they are trying to solve.
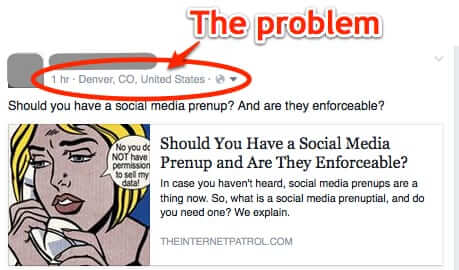
How to Stop Facebook from Posting Your Location (2016)
You may have noticed that Facebook recently started publishing the location from which you are posting when you post to Facebook via the web (with your browser), whether you want it to or not. And so you may be wondering how to stop Facebook from posting your location. Here’s how.
Location Based Reminders Now Available on iPhone for Anywhere
We’ve written before about how to set up location-based reminders in the iPhone, however until fairly recently it required you to have the address of the location at which you wanted to be reminded in your contacts. No more. Now you can tell Siri to remind you of something when you arrive anywhere, any time! Here’s how.
How to Turn Off or Disable Location Tagging and Tracking on Facebook
Recently we discovered that somehow Facebook had started including our location in posts, even though we were sure we had location tagging turned off. So we started searching for how to disable location tracking on Facebook. And guess what. At the time of this writing, there is no way on Facebook to set Location by default to “off”. That’s because you have to turn it off on your computer or smartphone, not on Facebook.
NSA Mining Data from Smartphone Apps
Turns out there is another reason for rejecting all those insidious game invitations from smartphone apps and their Facebook counterparts: the New York Times has revealed today that the NSA and its British counterpart, GCHQ, are mining the data that your smartphone apps are generating, from location data, to contact lists, to phone logs and even the data embedded in images. Dubbed the “Mobile Surge” by the Brits, the intelligence community is giddy with glee over the trove of data served up by mobile apps.
NSA Co-Traveler Program Tracking Every Cell Phone Movement and Location
The newest reveal about the NSA’s surveillance activities is the existance of the NSA Co-Traveler program, through which the NSA is tracking the location and movements of the majority of cell phones on the planet, relationship-mapping every cell phone with every other cell phone.
Stunning Example of What Cell Phone Records and Publicly Available Data Can Reveal About You
It’s amazing to us that even with the public knowing that agencies such as the NSA are accessing cell phone records, and with cautions against using location-based services or revealing your location on Twitter, people seem to choose to ignore the cautions. Well, perhaps this will convince you. Even before all of this came to light, way back in 2009, a German politician named Malte Spitz, in an effort to demonsrate just how much we have given up our privacy – just how insidious it is – decided to make public six-months’ worth of his cell phone records. And the German newspaper Die Zeit created an animation – really an animated visualization – of where Spitz went, and what he was doing, every day of that six months, with stunning accuracy.
“Girls Around Me” Girl Finding App May No Longer Be in the App Store but It’s Still Out There
Hailed as a rapist and stalker’s haven, “Girls Around Me” is not only a creepy app in its concept, it enables iPhone and android users to track nearby women based on their geographic location. The information is aggregated from check-ins through Facebook and Four Square, and perhaps what makes it the creepiest app, and why it is being called the “stalking app,” is because if a user of the app likes what he initially sees about the girl, he can see more information about her as pulled from her Four Square account and Facebook link, including more photos of her.
Google Maps Allows You to See Floor Plans of Malls, Museums, Airports and More
Google had made shopping, sight-seeing and travel even easier, by making the indoor floor plans of malls, museums, libraries, transit stations and airports, worldwide, available through Google Maps. The feature, previously exclusively available through Google Maps for Android, is now available on your desktop so that it can be used by all.
California Says “No Warrant Needed to Get Location-Based Data”, Can Other States be Far Behind?
California Governor Jerry Brown vetoed a bill on Sunday that would have required a search warrant in order to obtain location-based personal information obtained through cell towers from mobile devices such as cell phones and tablets, and also GPS systems. The veto came with the message that Brown felt that information based on a user’s location is important to the processes needed by law enforcement.
Growing Concerns Over Carrier IQ – What it Is and How to Tell If Your Phone is Likely to Have It
Cell phone companies are scrambling amid growing concerns over the Carrier IQ (or “CIQ”) software that has shipped preinstalled (and undisclosed) on many, many smartphones across several carriers, as demands for full disclosure and accountability increase, Federal representatives demand answers, and some suggest that the use of the software, which is alleged to log keystrokes, websites visited, and location, violates Federal wiretapping law. Trevor Eckhart, who first discovered and outed what Carrier IQ was doing, went so far as to call it a “rootkit”.
“Take This Lollipop” – What it Is, and Why You Should Watch It
“Take This Lollipop”, the creepy Facebook tour through your personal information, is an excellent example of something we have been trying to pound into your heads all along: putting personal information on the Internet (such as location based check ins) can be dangerous. More to the point: most people have no idea how much personal information they really have revealed online, and how easy it is to track them down, stalking them, and worse. “Take this Lollipop” is technically a Facebook app, which is how (and why) it asks for you to log in using Facebook Connect, something that we also advise against.