Tag: fbi
Twitter and the FBI, sitting in a tree –
And they aren’t just k-i-s-s-i-n-g….. It’s much worse.
What’s being disclosed in the now-weekly Twitter releases certainly doesn’t improve the image of the FBI (and, of course, other 3-letter and 4-letter agencies).
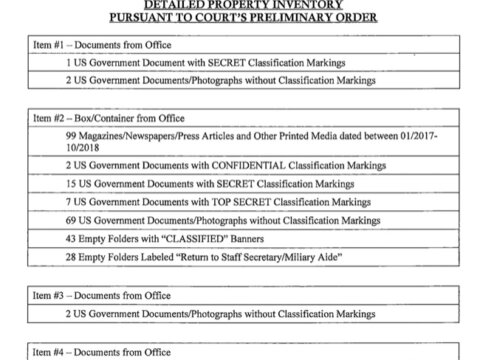
Full Detailed List of Everything Seized from Trump by the FBI at Mar-a-Lago
Here is the full, detailed list of all of the documents seized by the FBI from President Trump during their raid on Mar-a-Lago earlier this month. This list was just provided to the court and unsealed by the court yesterday. We are providing it both as a PDF and in plain text so that it can be searched. The Internet Patrol is not a political outlet, and we make this information available with no additional comment; we make it available because we have the resources and knowledge to do so, so that people who are searching for it can find it.
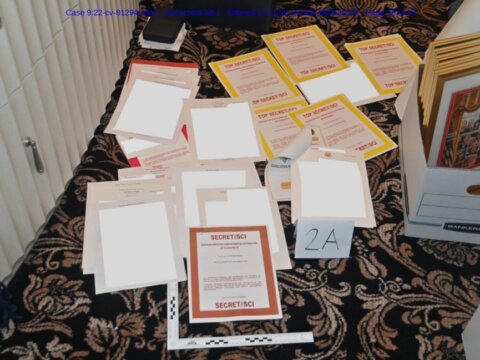
Full Text of DOJ Special Master Filing Including Damning Image
Late on Tuesday, August 31, 2022, the Department of Justice (DOJ) filed its objections to Donald Trump’s Special Master request. The information in the document is the most damning yet, including an image of the pile of documents, accumulating on the floor as the FBI conducted their search, a document with the SECRET / SCI clearly visible. Below is that picture, and the full text of the filing as both a PDF and in plain text (we are in the process of adding the plain text, so refresh frequently until we are done). The Internet Patrol is not a political outlet, and we make this information available with no additional comment; we make it available because we have the resources and knowledge to do so, so that people who are searching for it can find it.
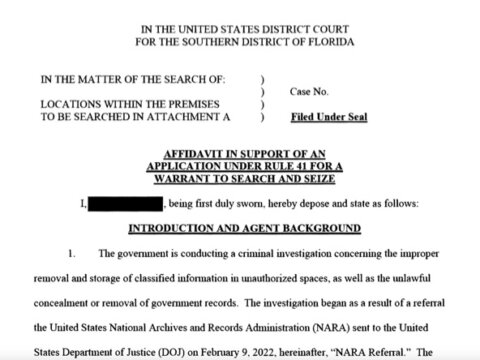
Full Text and Content of DOJ Affidavit Used to Get the Search Warrant for Trump Mar-a-Lago
Here is the original PDF of the DOJ affidavit that was released today, August 26, 2022, and that was used to secure the search warrant that the FBI used to search Mar-a-Lago for documents and evidence in the investigation of Donald Trump. Among other things, the affidavit asserts that “As described above, evidence of the SUBJECT OFFENSES has been stored in multiple locations at the PREMISES.”
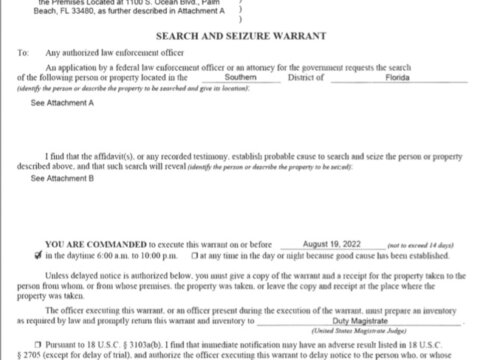
Full Text of Donald Trump Search Warrant and Full Text of Receipt List of Documents Recovered from Mar-a-Lago
Here is the full text of the search warrant executed at Mar-a-Lago this week, as well as the full text of the list of the documents that the FBI took, known as a “receipt” list. We are in the process of cleaning it up, however you can also find a PDF of the Donald Trump search warrant and receipt list at the bottom of this page. One of the things that we find very interesting is that there are two receipt lists, if you look at the item numbers in each list, taken together they are in numerical sequence, but broken up between the two lists. Note that the case ID in each is redacted. This suggests to us that there are two separate, but related, cases going on, some of the documents recovered satisfying the warrant with respect to one case, and others satisfying the warrant with respect to the other case.
FBI Urges 2022 China Olympics Athletes to Leave Phones at Home and Use Temporary ‘Burner’ Phones (Includes Full Text of Warning)
The FBI is warning U.S. Olympic athletes who are attending the 2022 Olympics in Beijing, China, to leave their cell phones at home, and instead pick up and bring temporary mobile phones, so-called ‘burner phones’ or disposable phones. The warning, put out last night (January 1, 2022), came from the FBI’s Cyber Division, and was announced as a warning to private industry. While the warning was also geared towards network operators and other industries, the warning specifically, and unusually, speaks directly to individuals as well.
The Truth about the FBI USPS idHSC Voluntary Fingerprint Submission Program
There’s a lot of confusion around the Internet about the FBI’s recently announced idHSC program (seen by some as ldHSC), where you can voluntarily submit your fingerprints at the post office (USPS) to find out what agencies have associated with your fingerprints. Here’s the real info.
Federal Court Holds “No Expectation of Privacy on Personal Computer”
In a stunning decision, a Federal court has held that a user has no expectation of privacy for their personal computer if they have connected that computer to the Internet. While the case and holding is fairly complex, this part of the holding boils down to this: in this day and age we know that computers that are connected to the Internet can be hacked, and knowing this, we are not entitled to an expectation of privacy on our personal computers.
Apple: It Seems Disagreeing with DOJ Means You Must be Evil and anti-American
In the latest round over the Feds’ effort to force Apple to help them break into the San Bernardino shooter’s iPhone, and Apple’s refusal to do so, Apple has come out with both fists up. The Feds most recent court filing accuses that “Apple’s rhetoric is not only false, but also corrosive of the very institutions that are best able to safeguard our liberty and our rights.” In response, Apple’s general counsel, attorney Bruce Sewell, said during a press conference call that “…it seems like disagreeing with the Department of Justice means you must be evil and anti-American.” (Full text below.)
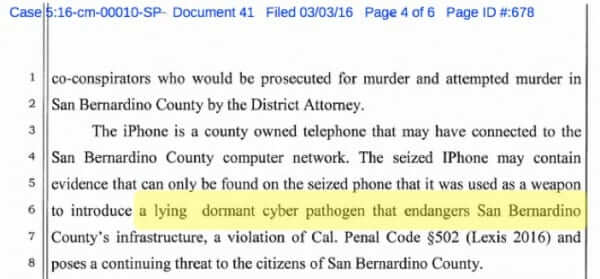
San Bernardino DA Suggests “lying dormant cyber pathogen” on Shooter’s iPhone
In a novel twist in the FBI versus Apple iPhone case, the San Bernardino District Attorney’s office has filed a motion (full text below) to submit an Amicus Curiae brief, stating that, among other things, the phone could harbor a “lying dormant cyber pathogen.” Of course, there’s no such thing as a lying dormant cyber pathogen, but why let a little thing like the facts get in the way of a good argument?
Latest in Apple FBI iPhone Wranglings: Just 1 Phone Turns Out to Already be at least 12 Phones (plus Full Text of FBI Motion)
As we recently reported, the FBI (and so the Federal government) is trying to force Apple to assist them in unlocking the iPhone that belonged to San Bernardino shooter Syed Farook. A Federal court ordered Apple to do so, and so far Apple has resisted. Part of the heart of the FBI’s argument is that this will affect only one phone, while Apple has insisted that it’s much larger than that – that an order to help unlock one phone will lead to a dangerous precedent of being ordered to help unlock any number of phones. The Feds have steadfastly insisted it is “just this one.” However, recent court filings have revealed that in fact there are as many as a dozen iPhones in other cases just waiting for Apple to be ordered to unlock them.
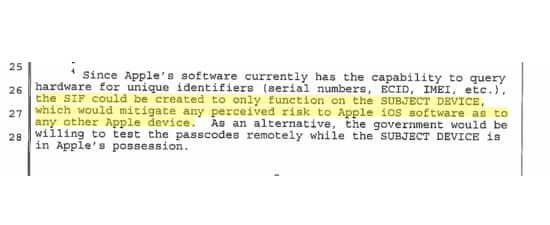
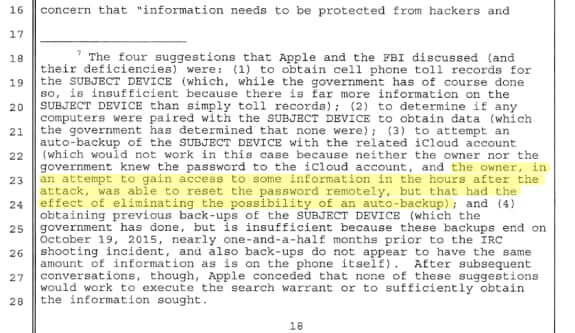
Feds Bury New Potentially Crucial Information in Footnote in Apple Terror iPhone Dispute
In Round 2 of the Apple iPhone FBI court dispute, in which the court ordered Apple to alter the iPhone used by San Bernardino shooter Syed Farook, the Feds have filed a Motion to Compel Apple to comply with the order, in which they mention, in passing in a footnote, that the San Bernardino County Department of Public Health (SBCDPH) actually changed the password to the iCloud account to which the phone was backing up, thwarting any further backups of the phone’s data, between the time it was recovered from Farook’s vehicle, and handing it over to the FBI.
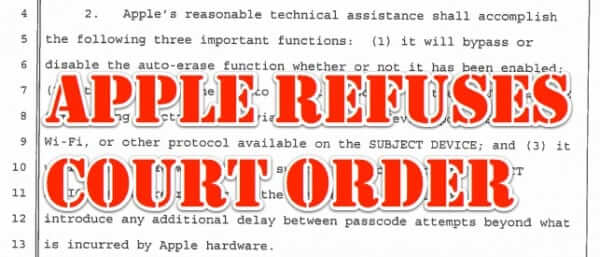
Full Explanation of Court Order to Apple to Unlock San Bernardino Shooters’ iPhone and Apple Refusal (Full text of court order and Tim Cook’s letter included)
Late yesterday afternoon a Federal court ordered Apple to assist the FBI in their investigation into the San Bernardino shootings by unlocking the iPhone belonging to the shooters. In response, this morning, Apple CEO Tim Cook released a public statement in which Apple refuses to comply, explaining the reasons that even if Apple can comply with the order, they will refuse to do so.
Law Enforcement is Searching Ancestry.com and 23andMe DNA Databases
We’ve always said that submitting your DNA for DNA analysis at services like 23andMe, and AncestryDNA by Ancestry.com, is a bad idea, because regardless of what ‘good’ can come from it, the potential for bad is just too great. Having unknown actors have access to your DNA information is a violation of privacy of the most basic, and intimate, kind. Sadly, we were right. Law enforcement agencies are now using what is known as “familial DNA search” to go on DNA fishing expeditions, searching for near matches to DNA found at a crime scene.
What the Darkode Cybercrime Ring Sting and Bust Means for You
Last month the U.S. Justice department announced the takedown of the Darkode (get it? DarkCode – Dark Code?) international cybercrime ring, which the DOJ called one of the “gravest threats” to the security of online data. But what exactly does that mean to you, the average user sitting at home behind your computer?