Tag: eavesdropping
Bug in FaceTime Lets Callers Hear Your Audio Even if You Haven’t Accepted the Call – Also How to Disable FaceTime
In the past 24 hours it was revealed, and then admitted by Apple, that a bug in the FaceTime app was allowing FaceTime callers to listen in on the audio of what was going on around the recipient’s device before the recipient picked up the call. And if the recipient pressed the button to reject the call, instead of ending the call it would start broadcasting video from the recipient’s device as well!
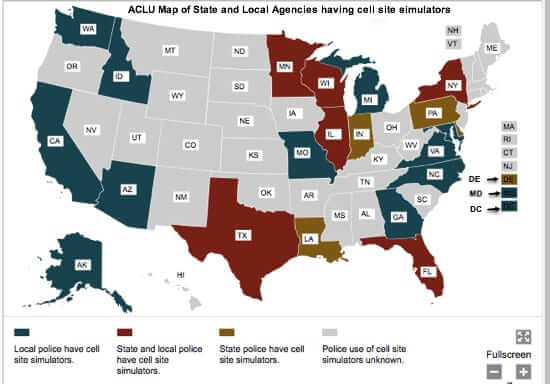
Stingray IMSI Cell Phone Tower Emulator that Grabs All Your Cell Phone Data as You Drive By Deployed by Law Enforcement Around the Country
Stringray device phone technology tricks your cellphone into connecting to the Stingray ‘phone tower’ (your phone doesn’t realize it’s connecting to a cell phone simulator interceptor rather than your provider’s tower – it’s the ultimate in cell phishing), and then sucks down all of your International Mobile Subscriber Identity (IMSI) information, including not only your call details, but even your text messages, email, and other private information. (This is also known as an IMSI catcher.) Now being deployed by local police and sheriff departments, these cell phone interception and eavesdropping devices are not only legal, but they require no warrant, and their use is jealously protected by the Feds.
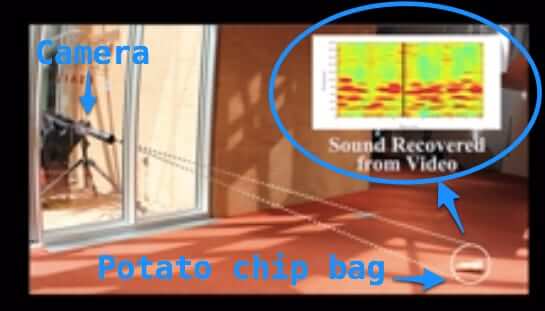
Eavesdropping by Reading Vibrations on a Potato Chip Bag
MIT grad student Abe Davis, along with colleagues, has demonstrated the ability to eavesdrop by reading the vibrations on objects such as a potato chip bag. Dubbed the “Visual Microphone”, Davis was able to use a regular digital camera to perform this feat. Which means that someone could appear to be filming the table next to you, but are actually about to decode what you are saying. Davis, along with MIT professors Frédo Durand and Bill Freeman, have also used this method to eavesdrop on the vibrations in a glass of water, and even on the leafs of a potted plant.
Feds Seek Broad Ability to Monitor All Internet Communications
According to government officials and insiders, the Federal government is seeking broad authority and discretion to monitor all Internet communications, including communications on social networking sites such as Facebook and Twitter, instant messaging systems, and even (or hey, perhaps especially) encrypted emails.