Tag: data
Walmart Looking to Offer Walmart-Branded Vizio TVs to Further Exploit Customer Data
Walmart is rumored to be looking to acquire smart television company Vizio (the potential deal is said to be around $2billion), so that they can enhance their own line of Walmart-branded television sets. Lest you think that this is simply an ego move on Walmart’s part, let us disabuse you of that notion right now: smart TVs are an incredibly rich source of consumer data – your data – just ripe for the mining.
Google Search Introduces ‘Perspectives’ Filter for More Personal and Human-Centric Results
Google Search is introducing a new feature called “Perspectives”, a specific filter designed to bring you information sourced from individuals on forums and social media platforms. This innovative tool appears on qualifying search queries that could be enriched by the experiences and insights of others, supplementing the existing array of tabs including Images, Maps, and various topic-based filters.
Your Deepest Secrets are Not Safe with Your ISP
If you were expecting a piece of feel-good news, unfortunately this isn’t it. Unless you are like me, and find relaxation in reading articles which are gravely concerning for the future of privacy and digital human rights. Either way, we got you covered: A recent study conducted by the Federal Trade Commission (FTC) put major league internet service providers on the line; and what they found might have you logging off. The FTC issued orders for information on consumer data practices, privacy, and the companies transparency in regards to such practices, and what they found was pretty horrifying.
Yes, Facebook’s Data Mining is a Problem
Yes, Facebook has once again admitted that there is seriously a problem with the way they are handling user data. Are we really that surprised? Maybe this is the first time you’ve seen the news that Facebook’s privacy issues are spiraling out of control. Or perhaps this is the first time you’ve cared to search for it. This isn’t a new occurrence.
Data Broker was Selling Location-Tracking Data of People Visiting Abortion Providers
So a date broker was selling the location-tracking data of people visiting abortion providers. Data about all sorts of things holds value, and in today’s world, your data holds plenty. Like it or not, your data has almost definitely already been bought and sold. Just like mine, just like nearly every other person’s in the good ol’ US of A. Of course, it would be nice if you or I had some say in the matter. Personally, I would not freely consent to my data being bought or sold without providing me a benefit, and that is precisely the reason why I don’t have any say in the matter.
Massive T-Mobile Data Breach of User Personal Information Includes Social Security Numbers
A massive security breach at T-Mobile has exposed the personal private data of nearly 50million T-Mobile customers and prospects, including social security numbers and drivers license numbers. And it doesn’t matter whether you are a current, past, or even prospective customer of T-Mobile, your data has been compromised. By “prospective” we mean someone who has applied for an account with T-Mobile even if they never actually signed up. And that is because the T-Mobile data breach includes those social security numbers which are, of course, required for just about every service that is going to extend credit to you.
How to Have Your Email Address and Other Personal Data Removed from Square in 2021
It can be frustrating trying to figure out how to remove your email address from Square, especially if you never gave it to them in the first place, and you are trying to invoke a ‘right to be forgotten’.
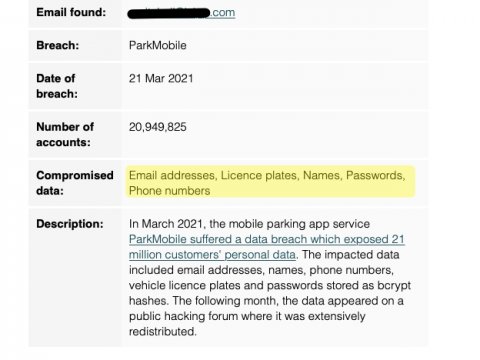
Updated Information about the Massive ParkMobile Data Breach
The personal data of more than 20million ParkMobile customers has been hacked, and put up for sale in a hacking forum.
Here’s What’s Up with All Those ‘Do Not Sell My Personal Information’ Links and Pages that are Cropping Up
If you are wondering “What does Do Not Sell My Personal Information mean?” after seeing it all over the Internet on links and pages, here’s what it’s about.
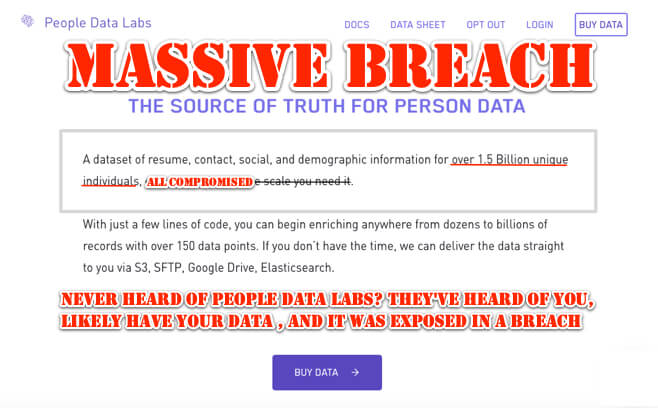
Never Heard of People Data Labs? They’ve Heard of You, Likely Have Your Data and It Was Exposed in a Breach
People Data Lab (PDL), a data “enrichment” company, boasts that they have data on 1.5 billion people, almost certainly including you. That data, stored on an Elasticsearch server, was all breached in November.
Juice Jacking – When Your Data is Stolen Through a Public USB Charging Port
Juice Jacking: the LA DA’s office is warning about it, Snopes says it’s real, alright. But just what is juice jacking? And how real is the threat? Here’s all of the info you need about juice jacking and the threat it poses to you.
Tesla: Data Security Hell on Wheels?
The same data uploads and downloads that make Teslas dream cars for some Tesla owners also may make them security hell for all Tesla drivers. That’s because Tesla vehicles are big, wheeled Internet of Things devices.
Largest Set of Sky Survey Astronomical Data in History Made Available Online
The largest data set of astronomical sky survey data in history has just been made available on the Internet, for free, and for anyone to access. The data, the second edition of data from the Panoramic Survey Telescope and Rapid Response System (Pan-STARRS), comprises over 1.6 petabytes of data.
Quora Announces First Major Data Breach of December
Quora has just announced that it discovered a data breach on Friday, November 30th. Taking a move from the playbook of, apparently, nobody else, Quora did not wait weeks or months or even days to announce the breach – going from discovery to notifying their users in no more than 72 hours. Thank you for that, Quora!
Colorado Second State to Enact New Consumer Data Protection Law in 90 Days
Hot on the heels of California passing their California Consumer Protection Act (CCPA) which is actually a consumer data protection law, and on the slightly more distant heels of the passage and enactment of the General Data Protection Regulation (GDPR), Colorado has both passed and enacted the Colorado Consumer Data Protection Act (CCDPA).