As we recently reported, the FBI (and so the Federal government) is trying to force Apple to assist them in unlocking the iPhone that belonged to San Bernardino shooter Syed Farook. A Federal court ordered Apple to do so, and so far Apple has resisted. Part of the heart of the FBI’s argument is that this will affect only one phone, while Apple has insisted that it’s much larger than that – that an order to help unlock one phone will lead to a dangerous precedent of being ordered to help unlock any number of phones. The Feds have steadfastly insisted it is “just this one.” However, recent court filings have revealed that in fact there are as many as a dozen iPhones in other cases just waiting for Apple to be ordered to unlock them.
[For a full explanation of the case and court order, see here, and then go here for the latest about how the Feds failed to disclose crucial information in their motion in the case.]
Now it has come to light that in fact there are already several other cases pending before various Federal courts in which the courts are being asked to order Apple to assist with unlocking several different iPhones, most of which don’t even having to do with terrorism cases.
This despite the fact that in the documents filed by the government in the San Bernardino shooting case, the government makes a point of leaning heavily on the need for this because it’s a terrorism case, and that it is “just this one phone.”
In fact, in the first several pages of the Feds’ motion which led to the court order, the Feds repeatedly reassured that this action would apply only to the San Bernardino shooter’s iPhone (“the SUBJECT DEVICE”).
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
Now, it may be a case of one hand not knowing what the other is doing, but as the Washington Post [Page no longer available – we have linked to the archive.org version instead] reported yesterday afternoon, there are cases pending against as many as a dozen other iPhones, in various Federal courts.
This information came to light at least in part owing to a letter written by Apple counsel Marc Zwillinger, in which, in response to the Court’s order that “Apple provide certain additional details regarding other requests it has received” through the courts for assistance with unlocking/unblocking iPhones, he pointed to cases in Illinois, New York, Ohio, and California, all requiring the same thing (and all predicated on the All Writs Act). (Read here for the EFF’s explanation of the All Writs Act as it relates to encryption.)
Mr. Zwillinger’s letter to the Court indicates that there are at least nine different court actions, regarding a dozen or more iPhones, all involving demands for Apple to “let us in.”
Here’s Mr. Zwillinger’s letter:
In re Order Requiring Apple Inc. to Assist in the Execution of a Search Warrant Issued by the Court, No. 15-MC-1902
Dear Judge Orenstein: I write in response to this Court’s February 16, 2016 order (the “Order”) requesting that Apple provide certain additional details regarding other requests it has received during the pendency of this matter that are of a similar nature to the one at issue in the instant case. As recently as yesterday, Apple was served with an order by the United States Attorney’s Office for the Central District of California. (See Exhibit A.) The government obtained that order on the basis of an ex parte application pursuant to the All Writs Act (see Exhibit B), regarding which Apple had no prior opportunity to be heard (despite having specifically requested from the government in advance the opportunity to do so). The attached order directs Apple to perform even more burdensome and involved engineering than that sought in the case currently before this Court— i.e., to create and load Apple-signed software onto the subject iPhone device to circumvent the security and anti-tampering features of the device in order to enable the government to hack the passcode to obtain access to the protected data contained therein. (See Exhibit A.) As invited by the California court’s order, Apple intends to promptly seek relief. But, as this recent case makes apparent, the issue remains quite pressing. In addition to the aforementioned order, Apple has received other All Writs Act orders during the pendency of this case, certain details of which are set forth in the table below.
In particular, for each such request Apple provides the following categories of information requested in the Order:
(1) the jurisdiction in which the request was made, (2) the type of device at issue in the request, (3) the version of iOS being used on that device, and (4) Apple’s response to the request and/or its current status, as applicable. Date Received
Jurisdiction
Device Type
iOS Version
Status
10/8/2015
Southern District of New York
iPhone 4S
7.0.4
Apple objected (12/9/2015)
10/30/2015 Southern District of New York
iPhone 5S
7.1
Apple objected (12/9/2015)
11/16/2015 Eastern District of New York
iPhone 6 Plus
8.1.2
Apple objected (12/9/2015)
iPhone 6
8.1.2
11/18/2015 Northern District of Illinois
iPhone 5S
7.1.1
12/4/2015
iPhone 6
8.0 (or higher) Apple objected (12/9/2015)
iPhone 3
4.2.1
iPhone 3
6.1.6
Northern District of California
12/9/2015
Northern District of Illinois
iPhone 5S
7.0.5
Apple requested copy of underlying Motion but has not received it yet (2/1/2016)
1/13/2016
Southern District of California
N/A (device ID not yet provided)
N/A (device ID not yet provided, but the requesting agent advised device is preiOS 8)
Apple was advised by the requesting agent that she is seeking a new warrant. Apple has not yet received this warrant.
2/2/2016
Northern District of Illinois
iPad 2 Wifi
7.0.6
Apple objected (2/5/2016)
2/9/2016
District of Massachusetts
iPhone 6 Plus
9.1
Apple objected (2/11/2016)
2
Apple objected (12/9/2015)
With respect to the other categories of information sought in the Order (specifically, categories 4-6), Apple responds that following its objection or other response to each request there has not been any final disposition thereof to Apple’s knowledge, and Apple has not agreed to perform any services on the devices to which those requests are directed.1 Sincerely, /s/ Marc J. Zwillinger Marc J. Zwillinger
cc: All Counsel of Record (via ECF)
1 Apple further notes that shortly preceding the pendency of the instant case, it received additional All Writs Act orders—specifically, two from the Southern District of Ohio (both on September 24, 2015) and Northern District of Illinois (on October 6, 2015). Apple objected to each of these orders, and to Apple’s knowledge there have been no further developments since such objections were lodged.
Now, arguably it’s true that the FBI in the San Bernardino shooter’s case is only interested in that one iPhone, and that their request in the San Bernardino shooter’s case affects “only the SUBJECT DEVICE”.
But there is simply no way that one can say with a straight face, let alone believe, that the outcome in that case will not be used to set precedent for the other, and future, cases.
As Apple CEO Tim Cook said in his open letter, in response to and refusing to comply with the Court order in the San Bernardino iPhone case, “The government suggests this tool could only be used once, on one phone. But that’s simply not true. Once created, the technique could be used over and over again, on any number of devices. In the physical world, it would be the equivalent of a master key, capable of opening hundreds of millions of locks — from restaurants and banks to stores and homes. No reasonable person would find that acceptable.”
Or, perhaps, even more to the point, as Zwillnger says in another letter to the Court in one of those other cases, “Apple takes no position on whether and to what extent information from the Apple device in the government’s possession is relevant to any ongoing investigation, or necessary for the criminal defendant’s sentencing. But Apple has received additional requests similar to the one underlying the case before this Court. Apple has also been advised that the government intends to continue to invoke the All Writs Act in this and other districts in an attempt to require Apple to assist in bypassing the security of other Apple devices in the government’s possession. To that end, in addition to the potential reasons this matter is not moot that the government identifies, this matter also is not moot because it is capable of repetition, yet evading review.”
Here is the government’s full motion, in which they promise not to *** in Apple’s mouth it is only for one iPhone:
Full Text of Goverment’s (FBI’s) Motion to Compel and Memorandum of Points and Authorities in FBI San Bernardino Shooter’s Apple iPhone Case
[Note: While we have made the effort to provide a text-based version of these documents, for purposes of being able to search the full text of the documents, we do not have the time and resources to hand-edit these OCRed conversions of the original PDFs, hence the odd formatting.]
FILED
1 EILEEN M. DECKER
United States Attorney FE 16 .,!11: 00
2 PATRICIA A. DONAHUE
Assistant United States Attorney C.!FF.KU.S.MS.T!lf:TCO!'U
3 Chief, National Security Division
TRACY L. WILKISON (California Bar No. 184948)1"E=DE
4 Assistant United States Attorney
Chief, Cyber and Intellectual Property Crimes Sectidn
5 ALLEN W. CHIU (California Bar No. 240516)
Assistant United States Attorney FILED
CLERK, U S. DIS.qiICT COURT
6 Terrorism and Export Crimes Section
1500 United States Courthouse
7 312 North Spring Street FEB I 6 2016
Los Angeles, California 90012
8 Telephone: (213) 894-0622/2435 Ca4TRALUISil
Facsimile: (213) 894-8601
9 Email: Tracy.Wilkison@usdoj.gov
Allen.Chiu@usdoj.gov
10
Attorneys for Applicant
11 UNITED STATES OF AMERICA
12 UNITED STATES DISTRICT COURT
13 FOR THE CENTRAL DISTRICT OF CALIFORNIA
14 IN THE MATTER OF THE SEARCH OF ED No. 15-0451M
AN APPLE IPHONE SEIZED DURING
15 THE EXECUTION OF A SEARCH GOVERNMENT'S EX PARTE APPLICATION
WARRANT ON A BLACK LEXUS IS300, FOR ORDER COMPELLING APPLE INC. TO
16 CALIFORNIA LICENSE PLATE ASSIST AGENTS IN SEARCH;
35KGD203 MEMORANDUM OF POINTS AND
17 AUTHORITIES; DECLARATION OF
CHRISTOPHER PLUHAR; EXHIBIT
18
19
20 The United States of America, by and through its counsel,
21 Assistant United States Attorneys Tracy L. Wilkison and Allen W.
22 Chiu, hereby applies to the Court ex parte pursuant to the All Writs
23 Act, 28 U.S.C. 1651, for an order that Apple Inc. ("Apple") provide
24 assistance to agents of the Federal Bureau of Investigation ("FBI")
25 in their search of a cellular telephone, Apple make: iPhone 5C,
26 Model: A1532, P/N: MGFG2LL/A, S/N: FFMNQ3MTG2DJ, IMEI:
27 358820052301412, on the Verizon Network (the "SUBJECT DEVICE"). The
28 search and seizure of the SUBJECT DEVICE was authorized through a
1 search warrant which was obtained on December 3, 2015, Docket Number
2 ED No. 15-0451M, and was executed on the same day.
3 This application is based on the attached declaration of FBI
4 Supervisory Special Agent Christopher Pluhar, and the files and
5 records of this case, including the underlying search warrant, which
6 is attached hereto as Exhibit 1.
7 Dated: February 16, 2016 Respectfully submitted,
8 EILEEN M. DECKER
9 United States Attorney
PATRICIA A. DONAHUE
10 Assistant United States Attorney
11 Chief, National Security Division
12
13 TRACY L. ILKISON
ALLEN W. CHIU
14 Assistant United States Attorneys
15 Attorneys for Applicant
16 UNITED STATES OF AMERICA
17
18
19
20
21
22
23
24
25
26
27
28
2
1 MEMORANDUM OF POINTS AND AUTHORITIES
2I. INTRODUCTION
3 In the hopes of gaining crucial evidence about the December 2,
42015 massacre in San Bernardino, California, the government has
5sought to search a lawfully-seized Apple iPhone used by one of the
6mass murderers. Despite both a warrant authorizing the search and
7the phone owner's consent, the government has been unable to
8complete the search because it cannot access the iPhone's encrypted
9content. Apple has the exclusive technical means which would assist
10the government in completing its search, but has declined to provide
11that assistance voluntarily. Accordingly, the government
12respectfully requests that this Court issue an order compelling
13Apple to assist in enabling the search commanded by the warrant.
14II. FACTUAL BACKGROUND
15 The Federal Bureau of Investigation ("FBI") is in possession of
16a cellular telephone that was used by Syed Rizwan Farook ("Farook"),
17one of the terrorists who caused the December 2, 2015 shooting death
18of 14 people, and the shooting and injuring of 22 others, at the
19Inland Regional Center ("IRC") in San Bernardino, California. The
20cellular telephone is of Apple make: iPhone 5C, Model: A1532, P/N:
21MGFG2LL/A, S/N: FFMNQ3MTG2DJ, IMEI: 358820052301412, on the Verizon
22Network ("the SUBJECT DEVICE"). The SUBJECT DEVICE was seized
23pursuant to a federal search warrant for a black Lexus IS300 in
24Docket Number ED 15-0451M, which was issued by the Honorable David
25T. Bristow, United States Magistrate Judge, on December 3, 2015.
26The underlying search warrant, which authorizes the search of the
27contents of the SUBJECT DEVICE, is attached hereto as Exhibit 1 and
28incorporated herein by reference.
1 As explained in the attached declaration of FBI Supervisory
2 Special Agent ("SSA") Christopher Pluhar, the underlying search
3 warrant for the SUBJECT DEVICE arose out of an investigation into
4 the IRC shootings, and the participation by Farook and his wife,
5 Tafsheen Malik ("Malik"), in that crime. Subsequent to execution of
6 the search warrant at issue, the FBI obtained numerous search
7 warrants to search the digital devices and online accounts of Farook
8 and Malik. Through those searches, the FBI has discovered, for
9 example, that on December 2, 2015, at approximately 11:14 a.m., a
10post on a Facebook page associated with Malik stated, "We pledge
11allegiance to Khalifa bu bkr al bhaghdadi al quraishi," referring to
12Abu Bakr Al Baghdadi, the leader of Islamic State of Iraq and the
13Levant ("ISIL"), also referred to as the Islamic State ("IS"), the
14Islamic State of Iraq and al-sham ("ISIS"), or Daesh. ISIL,
15formerly known as Al-Qai'da in Iraq ("AQI"), has been designated a
16foreign terrorist organization by the United States Department of
17State, and has been so designated since December 2004. Farook and
18Malik died later that same day in a shoot-out with law enforcement.
19The government requires Apple's assistance to access the SUBJECT
20DEVICE to determine, among other things, who Farook and Malik may
21have communicated with to plan and carry out the IRC shootings,
22where Farook and Malik may have traveled to and from before and
23after the incident, and other pertinent information that would
24provide more information about their and others' involvement in the
25deadly shooting.
26 The SUBJECT DEVICE is owned by Farook's employer, the San
27Bernardino County Department of Public Health ("SBCDPH"), and was
28assigned to, and used by, Farook as part of his employment. The
2
1 SBCDPH has given its consent to the search of the SUBJECT DEVICE and
2 to Apple's assistance with that search.1
3 However, despite the search warrant and the owner's consent,
4 the FBI has been unable to search the SUBJECT DEVICE because it is
5 "locked" or secured with a user-determined, numeric passcode. More
6 to the point, the FBI has been unable to make attempts to determine
7 the passcode because Apple has written, or "coded," its operating
8 systems with a user-enabled "auto-erase function" that would, if
9 enabled, result in the permanent destruction of the required
10encryption key material after 10 erroneous attempts at the passcode
11(meaning that after 10 failed attempts at inputting the passcode,
12the information on the device becomes permanently inaccessible).
13When an Apple iPhone is locked, it is not apparent from the outside
14whether or not that auto-erase function is enabled; therefore,
15trying repeated passcodes risks permanently denying all access to
16the contents. Primarily because of this function and the delays
17that would be introduced by successive incorrect passcodes
18(discussed below), the government has not been able to attempt to
19determine the passcode and decrypt the files on the SUBJECT DEVICE
20pursuant to the search warrant, and the FBI cannot do so without
21Apple's assistance.
22 Apple is the manufacturer of the SUBJECT DEVICE, and the
23creator and owner of its operating system and software. Apple has
24the ability with older operating systems to obtain the unencrypted
25file content from phones without the passcode, and has routinely
26done so for law enforcement with a search warrant and accompanying
27
1 In addition, SBCDPH has a written policy that all digital
28devices are subject to search at any time by the SBCDPH, which
policy Farook accepted via signature upon his employment.
3
1 All Writs Act order. While Apple has publicized that it has written
2 the software differently with respect to iPhones such as the SUBJECT
3 DEVICE with operating system ("iOS") 9, Apple yet retains the
4 capacity to provide the assistance sought herein that may enable the
5 government to access the SUBJECT DEVICE pursuant to the search
6 warrant.
7 Specifically, and as detailed below, Apple has the ability to
8 modify software that is created to only function within the SUBJECT
9 DEVICE that would ensure that the added auto-erase function is
10turned off, allow for electronic submission of test passcodes, and
11ensure additional delays are not created. This would allow the
12government multiple investigative attempts to determine the passcode
13in a timely manner, without fear that the data subject to search
14under the warrant would be rendered permanently inaccessible. It is
15this assistance from Apple, which is required to execute the search
16warrant, that the government now asks the Court to order.
17III. DISCUSSION
18 A. Assistance Sought From Apple
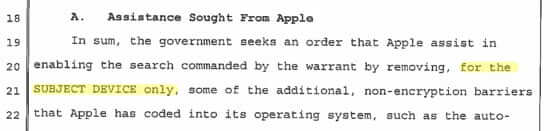
19 In sum, the government seeks an order that Apple assist in
20enabling the search commanded by the warrant by removing, for the
21SUBJECT DEVICE only, some of the additional, non-encryption barriers
22that Apple has coded into its operating system, such as the auto-
23erase function, the requirement that passwords be entered manually,
24and any software-invoked delay-upon-failure functions. While the
25government proposes a specific means of accomplishing this, the
26government requests that the order allow Apple to achieve the goals
27of the order in an alternative technical manner if mutually
28preferable.
4
1 As an initial matter, the assistance sought can only be
2 provided by Apple. As discussed in the attached declaration of SSA
3 Pluhar, the SUBJECT DEVICE is an iPhone 5c that was designed,
4 manufactured, and sold by Apple. Apple also wrote and owns the
5 software operating system marketed under the name of "iOS," and thus
6 is the owner of the operating system software for the phone at
7 issue. Apple's software licensing agreement specifies that its
8 software is "licensed, not sold," and otherwise prohibits users from
9 transferring any ownership of the iOS software.
10 Further to this point, Apple strictly and exclusively controls
11the hardware and software that is used to turn on and run its
12phones. According to Apple's "white papers" and other publicly
13available information about the security of its iOS programs, Apple
14has designed its mobile device hardware, as well as its operating
15system software, to only permit and run software that has been
16"signed" cryptographically by Apple using its own proprietary
17encryption methods. These security features prevent other persons,
18including the government, from running any other software on the
19SUBJECT DEVICE to attempt to recover data or test passcodes.
20 Apple has designed the iOS 9 operating system for its phones to
21encrypt the data files by a combination of two components - one
22user-determined passcode, and one unique 256-bit Advanced Encryption
23Standard ("AES") key (referred to as a "UID") which is fused into
24the phone itself during manufacture. Both passcode components are
25required in combination for the operating system to decrypt the
26phone's data files. When a user inputs her passcode, the phone
27conducts a complex calculation as determined by Apple's software
28
5
1 (and unknown to the government) which combines the UID with the user
2 passcode. If the result is accurate, the data is decrypted.
3 If one does not know the user-determined passcode, it is
4 possible, although time-consuming, to manually input passcodes one
5 at a time until the passcode is determined. Apple, however, has
6 also designed and written code for additional non-encryption-based
7 features which the government cannot overcome on its own.
8 First, Apple has designed a non-encryption, auto-erase function
9 as part of its iOS, which destroys the encryption key materials
10required for decryption and hence renders the contents of the device
11permanently incapable of being decrypted after ten consecutive
12incorrect passcode attempts. If this auto-erase function is
13enabled, the operating system will instantly, irrecoverably, and
14without warning erase the encryption keys necessary for accessing
15stored data. There is no way to know by examining the outside of
16the phone whether or not this function has been enabled, although,
17in this instance, the government suspects that it has, for the
18reasons explained in the attached declaration of SSA Pluhar -
19including because the SBCDPH has stated that the SUBJECT DEVICE was
20provided to Farook with that function turned on, and the most recent
21backup from the iCloud showed the function turned on. Accordingly,
22trying successive passcodes risks permanently losing the ability to
23access the data on the SUBJECT DEVICE. Because iOS software must be
24cryptographically signed by Apple, only Apple is able to modify the
25iOS software to change the setting or prevent execution of the
26function.
27 Relatedly, Apple has designed and written code for another non-
28encryption-based feature in that its iOS operating system is coded
6
1 to invoke time delays after repeated, unsuccessful passcode entries.
2 This means that after each failed passcode entry, the user must wait
3 a period of time before another attempt can be made, up to a 1-hour
4 delay after the ninth failed attempt. Additional wait times can
5 also be added into the software.
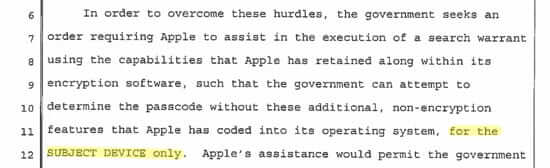
6 In order to overcome these hurdles, the government seeks an
7 order requiring Apple to assist in the execution of a search warrant
8 using the capabilities that Apple has retained along within its
9 encryption software, such that the government can attempt to
10determine the passcode without these additional, non-encryption
11features that Apple has coded into its operating system, for the
12SUBJECT DEVICE only. Apple's assistance would permit the government
13to electronically test passcodes without unnecessary delay or fear
14that the data subject to search under the warrant would be rendered
15permanently inaccessible. Given that these features were designed
16and implemented by Apple, that Apple writes and cryptographically
17signs the iOS, and that Apple routinely patches or updates its iOS
18to address security features or other functionality, modifying these
19features is well within its technical capabilities.
20 Specifically, in order to perform the search ordered in the
21warrant, the government requests that Apple be ordered to provide
22the FBI with a custom signed iPhone Software ("IPSW") file, recovery
23bundle, or other Software Image File ("SIF")2 that can be loaded onto
24the SUBJECT DEVICE. The SIF would load and run from Random Access
25
26
27
28 2 These are different terms for the essentially same thing: a
software file that will start up/"boot" an iPhone device.
7
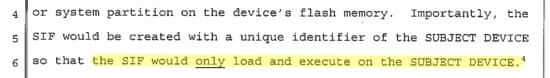
1 Memory ("RAM")3 and accordingly would not change the operating system
2 on the actual SUBJECT DEVICE, the user data partition (i.e., where
3 the contents of files created or modified by the user are stored),
4 or system partition on the device's flash memory. Importantly, the
5 SIF would be created with a unique identifier of the SUBJECT DEVICE
6 so that the SIF would only load and execute on the SUBJECT DEVICE.4
7 Once active on the SUBJECT DEVICE, the SIF would have three
8 primary functions: (1) the SIF would bypass or disable the auto-
9 erase function whether or not it has been enabled; (2) the SIF would
10enable the FBI to submit passcodes to the SUBJECT DEVICE for testing
11electronically (meaning that the attempts at the passcode would not
12have to be manually typed on the iPhone's screen; and (3) the SIF
13would not introduce any additional delay between failed passcode
14attempts beyond what is incurred by the hardware on the SUBJECT
15DEVICE. The SIF would be installed on the SUBJECT DEVICE at either
16a government facility, or alternatively, at an Apple facility (as is
17done when Apple recovers data from earlier iOS versions), but
18passcode attempts would be electronically submitted to the device by
19the government. This would allow the government to conduct the
20passcode attempts while Apple retains the SIF. The government
21further requests that the order permit Apple to satisfy these three
22
23
3 RAM is computer memory that is temporary and requires power to
24maintain the stored information; once the power is turned off, the
memory is lost.
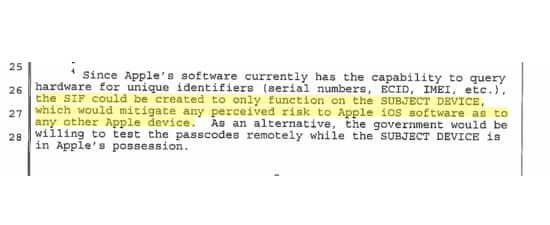
25 4Since Apple's software currently has the capability to query
26hardware for unique identifiers (serial numbers, ECID, IMEI, etc.),
the SIF could be created to only function on the SUBJECT DEVICE,
27which would mitigate any perceived risk to Apple iOS software as to
any other Apple device. As an alternative, the government would be
28willing to test the passcodes remotely while the SUBJECT DEVICE is
in Apple's possession.
8
1 goals, and installation and operation within the SUBJECT DEVICE, in
2 an alternative technical manner if mutually preferable.
3 B. The All Writs Act Permits This Order
4 The All Writs Act provides in relevant part that "all courts
5 established by Act of Congress may issue all writs necessary or
6 appropriate in aid of their respective jurisdictions and agreeable
7 to the usages and principles of law." 28 U.S.C. 1651(a). As the
8 Supreme Court explained, "[t]he All Writs Act is a residual source
9 of authority to issue writs that are not otherwise covered by
10statute." Pennsylvania Bureau of Correction v. United States
11Marshals Service, 474 U.S. 34, 43 (1985). The All Writs Act permits
12a court, in its "sound judgment," to issue orders necessary "to
13achieve the rational ends of law" and "the ends of justice entrusted
14to it." United States v. New York Telephone Co., 434 U.S. 159, 172-
153 (1977) (citations and internal quotation marks omitted). Courts
16must apply the All Writs Act "flexibly in conformity with these
17principles." Id. at 173; accord United States v. Catoggio, 698 F.3d
1864, 67 (2d Cir.2012) ("[C]ourts have significant flexibility in
19exercising their authority under the Act.") (citation omitted).
20 Pursuant to the All Writs Act, the Court has the power, "in aid
21of a valid warrant, to order a third party to provide nonburdensome
22technical assistance to law enforcement officers." Plum Creek
23Lumber Co. v. Hutton, 608 F.2d 1283, 1289 (9th Cir. 1979) (citing
24United States v. New York. Tel. Co., 434 U.S. 159 (1977)); see also
25In re U.S. for an Order Directing a Provider of Communication
26Services to Provide Technical Assistance to Agents of the U.S. Drug
27Enforcement Administration, 2015 WL 5233551 (D.P.R. August 27, 2015)
28(granting government's request pursuant to the All Writs Act for
9
1 technical assistance from provider of electronic communication
2 services to provide information, facilities, and technical
3 assistance to facilitate the consensual recording of all electronic
4 communication to and from a particular mobile phone); United States
5 v. Fricosu, 841 F.Supp.2d 1232, 1238 (D.Colo. 2012) (order issued
6 under All Writs Act requiring defendant to provide password to
7 encrypted computer seized pursuant to a search warrant). In New
8 York Telephone Co., the Supreme Court held that courts have
9 authority under the All Writs Act to issue supplemental orders to
10 third parties to facilitate the execution of search warrants. The
11 Court held that "[t]he power conferred by the Act extends, under
12 appropriate circumstances, to persons who, though not parties to the
13 original action or engaged in wrongdoing, are in a position to
14 frustrate the implementation of a court order or the proper
15 administration of justice, . and encompasses even those who have
16 not taken any affirmative action to hinder justice." Id. at 174.
17 In particular, the Court upheld an order directing a phone company
18 to assist in executing a pen register search warrant issued under
19 Rule 41. See id. at 171-76; see also Application of U.S. for an
20 Order Authorizing an In-Progress Trace of Wire Commc'ns over Tel.
21 Facilities (Mountain Bell), 616 F.2d 1122, 1132-33 (9th Cir. 1980)
22 (affirming district court's order compelling Mountain Bell to trace
23 telephone calls on grounds that "the obligations imposed . . . were
24 reasonable ones." (citing New York Tel. Co., 434 U.S. at 172)).
25 New York Telephone Co. also held that "Rule 41 is not limited
26 to tangible items but is sufficiently flexible to include within its
27 scope electronic intrusions authorized by a finding of probable
28 cause." 434 U.S. at 170. The Court relied upon the authority of a
10
1 search warrant pursuant to Rule 41 to predicate an All Writs Act
2 order commanding a utility to implement a pen register and trap and
3 trace device before Congress had passed a law that specifically
4 authorized pen registers by court order. Under New York Telephone
5 Co. and Mountain Bell, the All Writs Act provides authority for this
6 Court to order Apple to assist with steps necessary to perform the
7 search ordered by the warrant for the SUBJECT DEVICE.
8 Further, based on the authority given to the courts under the
9 All Writs Act, courts have issued orders, similar to the one the
10government is seeking here, that require a manufacturer to assist in
11accessing a cell phone's files so that a warrant may be executed as
12originally contemplated. See, e.g., In re Order Requiring [XXX],
13Inc. to Assist in the Execution of a Search Warrant Issued by This
14Court by Unlocking a Cellphone, 2014 WL 5510865, at *2 (S.D.N.Y.
15Oct. 31, 2014); see also United States v. Navarro, No. 13-CR-5525,
16ECF No. 39 (W.D. Wa. Nov. 13, 2013). Courts have also issued All
17Writs Act orders in furtherance of warrants in a wide variety of
18contexts, including: ordering a defendant to produce a copy of the
19unencrypted contents of a computer seized pursuant to a federal
20search warrant (Fricosu, 841 F.Supp. 2d at 1238); ordering a phone
21company to assist with a trap and trace device (Mountain Bell, 616
22F.2d 1122, 1129 (9th Cir. 1980)); ordering a credit card company to
23produce customer records (United States v. Hall, 583 F. Supp. 717,
24722 (E.D. Va. 1984)); ordering a landlord to provide access to
25security camera videotapes (In re Application of United States for
26an Order Directing X to Provide Access to Videotapes, No. 03-89,
272003 WL 22053105, at *3 (D. Md. Aug. 22, 2003) (unpublished order));
28and ordering a phone company to assist with consensual monitoring of
11
1a customer's calls (In re U.S., No. 15-1242 (M), 2015 WL 5233551, at
2*4-5 (D.P.R. Aug. 27, 2015) (unpublished order)). Because the
3orders are typically, as here, sought in the midst of a criminal
4investigation, they are usually obtained by way of ex parte
5application and not noticed motion. See, e.g., New York Telephone
6Co., 434 U.S. at 162; In re U.S., 2015 WL 5233551, at *1; In re
7 [XXX], 2014 WL 5510865, at *1; Application of U.S., 616 F.2d at
81122; In re Application of United States, 2003 WL 22053105, at *1.
9The government is not aware of any case in which the government
10obtained a Rule 41 search warrant but was denied an All Writs Act
11Order when necessary to facilitate the execution of the warrant.5
12 In New York Telephone Co., the Supreme Court considered three
13factors in concluding that the issuance of the All Writs Act order
14to the phone company was appropriate. First, it found that the
15phone company was not "so far removed from the underlying
16controversy that its assistance could not be permissibly compelled."
17Id. at 174. Second, it concluded that the order did not place an
18undue burden on the phone company. See id. at 175. Third, it
19determined that the assistance of the company was necessary to
20
21 5 The government is also aware of multiple other unpublished
orders in this district and across the country (obtained by ex parte
22application) compelling Apple to assist in the execution of a search
warrant by accessing the data on devices running earlier versions of
23iOS, orders with which Apple complied. The only exception known to
the government is litigation pending before a Magistrate Judge in
24the Eastern District of New York, where that court sua sponte raised
the issue of whether it had authority under the All Writs Act to
25issue a similar order. That out-of-district litigation remains
pending without any issued orders, nor would any such order be
26binding on this court. In any event, those proceedings represent a
change in Apple's willingness to access iPhones operating prior iOS
27versions, not a change in Apple's technical ability. However, based
on that litigation and communications with Apple, the government
28anticipates that Apple will avail itself of its ability to apply for
relief pursuant to the proposed order.
12
1achieve the purpose of the warrant. See id. Each of these factors
2supports issuance of the order directed to Apple in this case.
3 1. Apple is not "far removed" from this matter
4 First, Apple is not "so far removed from the underlying
5controversy that its assistance could not be permissibly compelled."
6Apple designed, manufactured and sold the SUBJECT DEVICE, and wrote
7and owns the software that runs the phone which software is
8preventing the execution of the warrant. Indeed, Apple has
9positioned itself to be essential to gaining access to the SUBJECT
10DEVICE or any other Apple device, and has marketed its products on
11this basis. Apple designed and restricts access to the code for the
12auto-erase function the function that makes the data on the phone
13permanently inaccessible after multiple failed passcode attempts and
14thus effectively prevents the government from attempting to execute
15the search warrant without Apple's assistance. The same software
16Apple is uniquely able to modify also controls the delays Apple
17implemented between failed passcode attempts -- which makes the
18process take too long to enable the access ordered by the court.
19Especially but not only because iPhones will only run software
20cryptographically signed by Apple, and because Apple restricts
21access to the code of the software that creates these obstacles,
22there is no other party that has the ability to assist the
23government in preventing these features from obstructing the search
24ordered by the court pursuant to the warrant.
25 Apple is also not made "far removed" by the fact that it is a
26non-government third party. While New York Telephone Co. involved a
27public utility, that was not the source of the holding that the All
28Writs Act order was appropriate. New York Telephone Co. emphasized
13
1that "the Company's facilities were being employed to facilitate a
2criminal enterprise on a continuing basis," and the company's
3noncompliance "threatened obstruction of an investigation which
4would determine whether the Company's facilities were being lawfully
5used." New York Telephone Co., 434 U.S. at 174. By analogy, where
6Apple manufactured and sold a phone used by a person at the center
7of a terrorism investigation, where it owns and licensed the
8software used to "facilitate the criminal enterprise," where that
9very software now must be used to enable the search ordered by the
10warrant, compulsion of Apple is permissible under New York Telephone
11Co. Moreover, other courts have directed All Writs Act orders based
12on warrants to entities that are not public utilities. For example,
13neither the credit card company in Hall nor the landlord in Access
14to Videotapes was a public utility. See Hall, 583 F. Supp. at 722;
15Access to Videotapes, 2003 WL 22053105, at *3. Apple's close
16relationship to the iPhone and its software which are by Apple's
17design makes compelling assistance from Apple permissible and the
18only means of executing the warrant.
19 2. The order does not place an unreasonable burden on
20 Apple
21 Second, the order is not likely to place any unreasonable
22burden on Apple. Where, as here, compliance with the order would
23not require inordinate effort, and reasonable reimbursement for that
24effort is available, no unreasonable burden can be found. New York
25Telephone, 434 U.S. at 175 (holding that All Writs Act order was not
26burdensome because it required minimal effort by the company,
27provided for reimbursement for the company's efforts, and did not
28disrupt its business operations); Mountain Bell, 616 F.2d at 1132
14
1 (rejecting telephone company's argument that unreasonable burden
2 would be imposed because of a drain on resources and possibility of
3 system malfunctions because the "Order was extremely narrow in
4 scope, restricting the operation to [electronic switching system]
5 facilities, excluding the use of manual tracing, prohibiting any
6 tracing technique which required active monitoring by company
7 personnel, and requiring that operations be conducted 'with a
8 minimum of interference to the telephone service'").
9 While the order in this case requires Apple to provide modified
10software, modifying an operating system - writing software code - is
11not an unreasonable burden for a company that writes software code
12as part of its regular business. In fact, providers of electronic
13communications services and remote computing services are sometimes
14required to write code in order to gather information in response to
15subpoenas or other process. In addition, the order is tailored for
16this particular phone, and because it involves preparing a single
17SIF, it presents no danger of system malfunctions or disrupting
18business operations. As noted above, Apple designs and implements
19all of the features discussed, writes and cryptographically signs
20the iOS, and routinely patches security or functionality issues in
21its operating system and releases new versions of its operating
22system to address issues. By comparison, writing a program that
23turns off non-encryption features that Apple was responsible for
24writing to begin with would not be unduly burdensome.6
25
26
27 6 It is worth noting as well that the user of the phone is now
dead, the user was made aware of his lack of privacy in the work
28phone while alive, and the owner of the phone consents to both the
search of the phone and to Apple's assistance in this matter.
15
1 However, to the extent that Apple believes that compliance with
2the order would be unreasonably burdensome, it can make an
3application to the Court for relief prior to being compelled to
4provide the assistance. See In re XXX, 2014 WL 5510865, at *2
5 (including in the issued All Writs Act Order a provision that states
6that "to the extent [the manufacturer] believes that compliance with
7this Order would be unreasonably burdensome, it may delay compliance
8provided it makes an application to the Court for relief within five
9business days of receipt of the Order."). The proposed order in
10this case includes a similar directive.
11 3. Apple's assistance is necessary to effectuate the
12 warrant
13 Third, Apple's assistance is necessary to effectuate the
14warrant. In New York Telephone Co., the Court held that the order
15met that standard because "[t]he provision of a leased line by the
16Company was essential to the fulfillment of the purpose to learn
17the identities of those connected with the gambling operation for
18which the pen register order had been issued." 434 U.S. at 175.
19Here, the proposed All Writs Act order in this matter also meets
20this standard, as it is essential to ensuring that the government is
21able to perform the search ordered by the warrant.
22 In this case, the ability to perform the search ordered by the
23warrant on the SUBJECT DEVICE is of particular importance. The user
24of the phone, Farook, is believed to have caused the mass murder of
25a large number of his coworkers and the shooting of many others, and
26to have built bombs and hoarded weapons for this purpose. The
27government has been able to obtain several iCloud backups for the
28SUBJECT DEVICE, and executed a warrant to obtain all saved iCloud
16
1 data associated with the SUBJECT DEVICE. Evidence in the iCloud
2 account indicates that Farook was in communication with victims who
3 were later killed during the shootings perpetrated by Farook on
4 December 2, 2015, and toll records show that Farook communicated
5 with Malik using the SUBJECT DEVICE. Importantly, however, the most
6 recent backup of the iCloud data obtained by the government was
7 dated October 19, 2015, approximately one-and-a-half months before
B the shooting. This indicates to the FBI that Farook may have
9 disabled the automatic iCloud backup function to hide evidence, and
10demonstrates that there may be relevant, critical communications and
11data around the time of the shooting that has thus far not been
12accessed, may reside solely on the SUBJECT DEVICE, and cannot be
13accessed by any other means known to either the government or Apple.
14 As noted above, assistance under the All Writs Act has been
15compelled to provide decrypted contents of devices seized pursuant
16to a search warrant. In Fricosu, a defendant's computer whose
17contents were encrypted was seized, and defendant was ordered
18pursuant to the All Writs Act to assist the government in producing
19a copy of the unencrypted contents of the computer. 841 F.Supp. 2d
20at 1237 ("There is little question here but that the government
21knows of the existence and location of the computer's tiles. The
22fact that it does not know the specific content of any specific
23documents is not a barrier to production."). Here, the type of
24assistance does not even require Apple to assist in producing the
25unencrypted contents, the assistance is rather to facilitate the
26FBI's attempts to test passcodes.
27
28
17
1 IV. CONCLUSION
2 For the foregoing reasons, the government respectfully requests
3 that the Court order Apple to assist the FBI in the search of the
4 SUBJECT DEVICE as detailed in the proposed order.
5
6 Dated: February 16, 2016 Respectfully submitted,
7 EILEEN M. DECKER
United States Attorney
8 PATRICIA A. DONAHUE
9 Assistant United States Attorney
Chief, National Security Division
10
11 riOi vv(IyA_---___
12 TRACY L. WILKISON
ALLEN W. CHIU
13 Assistant United States Attorneys
14 Attorneys for Applicant
UNITED STATES OF AMERICA
15
16
17
18
19
20
21
22
23
24
25
26
27
28
18
1 DECLARATION OF CHRISTOPHER PLUHAR
2 I, Christopher Pluhar, being duly sworn, declare and state as
3follows:
4I. INTRODUCTION
5 1. I am a Supervisory Special Agent ("SSA") with the Federal
6Bureau of Investigation ("FBI"), and Director of the Orange County
7Regional Computer Forensics Laboratory, Orange, California
8 ("OCRCFL"). The OCRCFL is a state of the art computer forensics
9laboratory comprised of task force officers from 15 agencies in
10Orange, Los Angeles, San Bernardino, and Riverside Counties. The
11laboratory specializes in the archival, preservation, and analysis
12of items of digital evidence, including computers, mobile devices,
13removable media (thumb drives, CDs etc) and Audio/Video equipment.
14 2. I have been a computer forensic examiner for the FBI since
152001, have attended 700+ hours of specialized training in
16computer/device forensics, and have certifications to conduct
17forensic analysis on Windows, Macintosh, and Linux/Unix systems, as
18well as mobile devices and cell phones. I have been the Director of
19the OCRCFL since November of 2013.
20 3. I have consulted extensively with the FBI's Cryptographic
21and Electronic Analysis Unit ("CEAU") in this matter, and bring
22their experience to bear in this declaration.
23II. PURPOSE OF DECLARATION
24 4. This declaration is made in support of an application for
25an order by the Court compelling Apple Inc. ("Apple") to assist the
26FBI in its effort to search of a cellular telephone, Apple make:
27iPhone 5C, Model: A1532, P/N:MGFG2LL/A, S/N:FFMNQ3MTG2DJ,
28IMEI:358820052301412, on the Verizon Network ("SUBJECT DEVICE").
1III. SEIZURE AND EXAMINATION OF SUBJECT DEVICE
2 5. The SUBJECT DEVICE was seized pursuant to the search
3warrant in Case No. ED 15-0451M, issued by the Honorable David T.
4Bristow, United States Magistrate Judge, on December 3, 2015. The
5SUBJECT DEVICE was found inside of the SUBJECT VEHICLE identified in
6the warrant. The underlying search warrant is attached hereto as
7Exhibit 1 and incorporated by reference.
8 6. I know based on my participation in this investigation and
9conversations with other involved agents and San Bernardino County
10Information Technology personnel, that the search warrant arose out
11of an investigation into the December 2, 2015 shooting death of 14
12people, and the shooting and injuring of 22 others, at the Inland
13Regional Center ("IRC") in San Bernardino, California, and the
14participation by Syed Rizwan Farook ("Farook") and his wife Tafsheen
15Malik ("Malik") in that crime. Subsequent to the search warrant at
16issue, the FBI has obtained numerous warrants to search the digital
17devices and online accounts of Farook and Malik. Through those
18searches the FBI has discovered, for example, that on December 2,
192015, at approximately 11:14 a.m., a post on a Facebook page
20associated with Malik stated, "We pledge allegiance to Khalifa bu
21bkr al bhaghdadi al quraishi," referring to Abu Bakr Al Baghdadi,
22the leader of Islamic State of Iraq and the Levant ("ISIL"), also
23referred to as the Islamic State ("IS"), or the Islamic State of
24Iraq and al-sham ("ISIS"), or Daesh. ISIL, formerly known as Al-
25Qa'ida in Iraq ("AQI"), has been designated a foreign terrorist
26organization by the United States Department of State and has been
27so designated since December 2004. Farook and Malik died later that
28same day in a shoot-out with law enforcement.
2
1 7. The SUBJECT DEVICE is owned by Farook's employer at the
2San Bernardino County Department of Public Health ("SBCDPH"), and
3was assigned to, and used by, Farook as part of his employment.
4While the SBCDPH does not have access to the passcode to the phone,
5it has given its consent to the search of it and to Apple's
6assistance with that search.
7 8. The SUBJECT DEVICE is "locked" or secured with a numeric
8passcode. I have been very involved in the attempts to gain access
9to the locked phone and comply with the search warrant. With the
10consent of the SBCDPH, I and other agents have been able to obtain
11several iCloud backups for the SUBJECT DEVICE, and I am aware that a
12warrant was executed to obtain from Apple all saved iCloud data
13associated with the SUBJECT DEVICE. I know from speaking with other
14FBI agents that evidence in the iCloud account indicates that Farook
15was in communication with victims who were later killed during the
16shootings perpetrated by Farook on December 2, 2015. In addition,
17toll records show that Farook communicated with Malik using the
18SUBJECT DEVICE between July and November 2015, but this information
19is not found in the backup iCloud data. Importantly, the most
20recent backup is dated October 19, 2015, which indicates to me that
21Farook may have disabled the automatic iCloud backup feature
22associated with the SUBJECT DEVICE. I believe this because I have
23been told by SBCDPH that it was turned on when it was given to him,
24and the backups prior to October 19, 2015 were with almost weekly
25regularity. I further believe that there may be relevant, critical
26communications and data on the SUBJECT DEVICE around the time of the
27shooting which has thus far not been accessed, may reside solely on
28the SUBJECT DEVICE, and cannot be accessed by any other means known
3
1to either the government or Apple. In addition, I have personally
2examined two other mobile devices belonging to Farook that were
3physically destroyed and discarded in a dumpster behind the Farook
4residence.
5 9. I have explored other means of obtaining this information
6with employees of Apple and with technical experts at the FBI, and
7we have been unable to identify any other methods feasible for
8gaining access to the currently inaccessible data stored within the
9SUBJECT DEVICE.
10IV. REQUESTED ASSISTANCE
11 10. I know based on my training and experience, knowledge of
12this case and review of Apple's publicly available information that
13the SUBJECT DEVICE is an iPhone 5c that was designed, manufactured,
14and sold by Apple. Apple also wrote and owns the software operating
15system marketed under the name of "iOS," and thus is the owner of
16the operating system for the phone at issue. Apple's software
17licensing agreement specifies that its software is "licensed, not
18sold," and otherwise prohibits users from transferring any ownership
19of the iOS software.
20 11. Apple strictly controls the hardware and software that is
21used to turn on and run its phones. According to Apple's "white
22papers" and other publicly available information about the security
23of its iOS programs, Apple has designed its mobile device hardware
24as well as its operating system software to only permit and run
25software that has been "signed" cryptographically by Apple using its
26own proprietary encryption methods. Apple has also added hardware-
27enforced features to the A6 processor found in the iPhone 5C which
28verifies software using Apple's cryptographic signature, ensuring
4
1that Apple devices can only run verified/signed software during the
2booting process (when the phone is being turned on). These features
3prevent the government from running any other software on the
4SUBJECT DEVICE to attempt to recover data.
5 12. In addition, an iPhone 5c is encrypted by a combination of
6two components - one user-determined passcode, and one unique 256-
7bit Advanced Encryption Standard ("AES") key (referred to as a
8"UID") fused into the phone itself during manufacture. Both
9passcode components are required in combination for the phone to
10decrypt its contents. When a user inputs the user-determined
11passcode, the phone conducts a complex calculation as determined by
12Apple's software (and unknown to the government) which combines the
13UID with the user passcode. If the result is accurate, the data is
14decrypted.
15 13. If one does not know the user-determined passcode, it is
16possible, although time-consuming, to manually input passcodes one
17at a time until the passcode is determined. Apple, however, has
18also designed and written code for additional non-encryption-based
19features which the government cannot overcome on its own. First,
20Apple has designed a non-encryption, auto-erase function as part of
21its iOS, which destroys encryption key material required for
22decryption, and hence renders the contents of the device incapable
23of being decrypted after ten consecutive incorrect passcode
24attempts. If this erase function is enabled, iOS will instantly,
25irrecoverably, and without warning erase the encryption keys
26necessary for accessing stored data. Because iOS software must be
27cryptographically signed by Apple, only Apple is able to modify the
28iOS software to change the setting or prevent execution of the
5
1 function. There is no way to know by examining the outside of the
2 phone whether or not this function has been turned on in the SUBJECT
3 DEVICE, although, in this instance, I suspect that it has because I
4 am told by an employee of SBCDPH that the SUBJECT DEVICE was
5 provided to Farook with the auto-erase function turned on, and I
6 know from my review of the most recent backup from the iCloud that
7 it showed the function turned on.
8 14. Relatedly, Apple has designed and written code for another
9 non-encryption based feature in that its iOS operating system is
10coded to invoke time delays which escalate after repeated,
11unsuccessful passcode entries. This means that after each failed
12passcode entry, the user must wait a period of time before another
13attempt can be made. From Apple documentation and testing, the time
14delays for the iPhone 5C are invoked by Apple software upon failed
15login attempts. Apple documentation states that the software
16invokes no delay for the first four attempts; a 1-minute delay after
17the fifth attempt; a 5-minute delay after the sixth attempt; a
18fifteen minute delays after the seventh and eight attempt; and a 1-
19hour delay after the ninth attempt. Additional wait times can also
20be added into the software.
21 15. In order to allow the government to perform the search
22ordered in the warrant, and the ability to test passcodes to decrypt
23the SUBJECT DEVICE without unnecessary delay or fear that the data
24subject to search under the warrant would be rendered permanently
25inaccessible, the government requests that Apple be ordered to
26provide the FBI with a signed iPhone Software file, recovery bundle,
27or other Software Image File ("SIF") that can be loaded onto the
28SUBJECT DEVICE. The SIF would load and run from Random Access
6
1Memory ("RAM") and would not modify the iOS on the actual phone, the
2user data partition or system partition on the device's flash
3memory. The SIF would be coded by Apple with a unique identifier of
4the phone so that the SIF would only load and execute on the SUBJECT
5DEVICE. Since Apple's software currently has the capability to
6query hardware for unique identifiers (serial numbers, ECID, IMEI,
7etc.), the SIF could be created to only function on the SUBJECT
8DEVICE, which would mitigate any perceived security risk to Apple
9iOS software. The SIF would be loaded via Device Firmware Upgrade
10 ("DFU") mode, recovery mode, or other applicable mode available to
11the FBI. In addition, Apple could run the SIF from within its
12facility, allowing passcodes to be tested electronically via remote
13network connection.
14 16. Once active on the SUBJECT DEVICE, the SIF would have
15three important functions: (1) the SIF would bypass or disable the
16auto-erase function whether or not it has been enabled on the
17SUBJECT DEVICE, meaning that multiple attempts at the passcode could
18be made without fear that the data subject to search under the
19warrant would be rendered permanently inaccessible; (2) the SIF
20would enable the FBI to submit passcodes to the SUBJECT DEVICE for
21testing electronically via the physical device port, Bluetooth, Wi-
22Fi, or other protocol available on the SUBJECT DEVICE (meaning that
23the attempts at the passcode would not have to be manually typed on
24the phone's screen), or alternately, Apple could be given the phone
25as is done when Apple recovers data from earlier iOS versions, but
26provide the government remote access to the SUBJECT DEVICE through a
27computer allowing the government to conduct passcode recovery
28analysis. This would allow the government to conduct the analysis
7
1without Apple actually providing the government with the SIF; and
2(3) the SIF would not introduce any additional delay between
3passcode attempts beyond what is incurred by the Apple hardware.
4 17. Based on my (and the CEAU's) review of available
5information about Apple's programs, Apple has the technological
6capability of providing this software without it being an undue
7burden. Apple routinely patches security or functionality issues in
8its iOS operating system and releases new versions of its operating
9system to address issues. I know from my training and experience,
10and that of my fellow agents, that providers of electronic
11communications services and remote computing services sometimes must
12write code in order to gather the information necessary to respond
13to subpoenas and other process, and that this is not a large burden.
14 18. However, in an abundance of caution, the government also
15requests that the order permit Apple to satisfy the three goals of
16the SIF and the loading of the SIF onto the SUBJECT DEVICE in an
17alternative technical manner if mutually preferable.
18 I declare under penalty of perjury that the foregoing is true
19and correct to the best of my knowledge and belief.
20Executed on February 16, 2016, Riverside, California.
21
22
23 C to uhar
24 FBI Supervisory Special Agent
25
26
27
28
8
EXHIBIT 1
U ND el- -T)L
AO 93 (Rev 12/09) Search and Seizure Warrant (USA() COCA Rev 01/2013)
UNITED STATES DISTRICT COURT
for the
Central District of California
In the Matter of the Search of
(Briefly describe the property to be searched
or identify the person by name and address)
Black Lexus 1S300 California License Plate #5KGD203,
handicap placard 360466F, Vehicle Identification Number 0354)4511i
JTHBD192X50094434
SEARCH AND SEIZURE WARRANT
To: Any authorized law enforcement officer
An application by a federal law enforcement officer or an attorney for the government requests the search
of the following person or property located in the Central District of California
(identify the person or describe the properly to be searched and give its location):
See Attachment A-2
The person or property to be searched, described above, is believed to conceal (identify the person or describe the
property to be seized):
See Attachment B
I find that the affidavit(s), or any recorded testimony, establish probable cause to search and seize the person or
property.
YOU ARE COMMANDED to execute this warrant on or before 14 days from the date of its issuance
(not to exceed 14 days)
CI in the daytime 6:00 a.m. to 10 p.m. at any time in the day or night as I find reasonable cause has been
established.
Unless delayed notice is authorized below, you must give a copy of the warrant and a receipt for the property
taken to the person from whom, or from whose premises, the property was taken, or leave the copy and receipt at the
place where the property was taken.
The officer executing this warrant, or an officer present during the execution of the warrant, must prepare an
inventory as required by law and promptly return this warrant and inventory to United States Magistrate Judge
on duty at the time of the return through a filing with the Cleric's Office.
(name)
0 1 find that immediate notification may have an adverse result listed in 18 U.S.C. 2705 (except for delay
of trial), and authorize the officer executing this warrant to delay notice to the person who, or whose property, will be
searched or seized (check the appropriate box) CI for days (not to exceed 30)
Cl until, the facts justifying, date
Date and time issued: /2 1,3 bc 2:Z
s signatur
City and state: Riverside, California David T. Bris tT , U.S. Magistrate Judge
Printed name and title
AUSA: AWC, MPT /it
AO 93 (Rev. 12/09) Search and Seizure Warrant (Page 2)
Return
Case No.: Date and time warrant executed..Copy of warrant and inventory left with:
Inventory made in the presence of .
Inventory of the property taken and name of any person(s) seized:
[Please provide a description that would be sufficient to demonstrate that the items seized fall within the items authorized to be
seized pursuant to the warrant (e.g., type of documents, as opposed to "miscellaneous documents") as well as the approximate
volume of any documents seized (e.g., number of boxes). If reference is made to an attached description of property, specify the
number of pages to the attachment and any case number appearing thereon.]
Certification (by officer present during the execution of the warrant)
I declare under penalty of perjury that I am an officer who executed this warrant and that this inventory is correct and
was returned along with the original warrant to the designated judge through a filing with the Clerk's Office.
Date: _ ..
Executing officer's signature
Printed name and tale
AUSA: AWC, MPT pk\--
ATTACHMENT A-2
PROPERTY TO BE SEARCHED
Black Lexus IS300 California license plate #5KGD203, handicap
placard 360466F, vehicle identification number
JTHBD192X50094434.
17 INSTRUMENTALITY PROTOCOL
ATTACHMENT B
I. ITEMS TO BE SEIZED
1. The items to be seized are evidence, contraband,
fruits, or instrumentalities of violations of (1) 18 U.S.C.
844(d) (Transportation or Receipt of Explosive Devices with the
Intent to Injure or Kill); (2) 18 U.S.C. 844(i) (Attempted
Destruction by Explosives of Any Building, Person, or Property); and
(3) 18 U.S.C. 844(n) (Conspiracy):
a. Explosives, smokeless powder, black powder,
gunpowder, or any other item that can be pipes, and wires;
b. Pipes and any items that may cause fragmentation;
c. Initiating devices to include burning fuse, hobby
fuse, blasting caps, manual or electrical timers, dry cell
batteries, electrical wire, alligator clips, electrical tape of
assorted colors commonly used to secure exposed electrical
wiring;
d. Books related to the construction of explosives;
e. Tools used in the construction of explosives such
as include hand held vise grips, table mounted vise grips, pipe
cutters, electrical; and non-electrical drills and drill bits.
f. Address and/or telephone books, telephones,
pagers, answering machines, customer lists, and any papers
reflecting names, addresses, telephone numbers, pager numbers,
18 INSTRUMENTALITY PROTOCOL
fax numbers and/or identification numbers of sources of supply
of explosives;
g. No more than 5 documents and records, including
electronic mail and electronic messages, reflecting the
ownership, occupancy, possession, or control of the SUBJECT
LOCATION, including lease/rental agreements, rent receipts,
registration documents, bank records, utility bills, telephone
bills, other addressed envelopes, and correspondence;
h. Any digital device used to facilitate the above-
listed violations and forensic copies thereof.
i. With respect to any digital device used to
facilitate the above-listed violations or containing evidence
falling within the scope of the foregoing categories of items to
be seized:
i. evidence of who used, owned, or controlled
the device at the time the things described in this warrant were
created, edited, or deleted, such as logs, registry entries,
configuration files, saved usernames and passwords, documents,
browsing history, user profiles, e-mail, e-mail contacts, chat
and instant messaging logs, photographs, and correspondence;
ii. evidence of the presence or absence of
software that would allow others to control the device, such as
viruses, Trojan horses, and other forms of malicious software,
19 INSTRUMENTALITY PROTOCOL
as well as evidence of the presence or absence of security
software designed to detect malicious software;
iii. evidence of the attachment of other devices;
iv. evidence of counter-forensic programs (and
associated data) that are designed to eliminate data from the
device;
v. evidence of the times the device was used;
vi. passwords, encryption keys, and other access
devices that may be necessary to access the device;
vii. applications, utility programs, compilers,
interpreters, or other software, as well as documentation and
manuals, that may be necessary to access the device or to
conduct a forensic examination of it;
viii. records of or information about
Internet Protocol addresses used by the device;
ix. records of or information about the device's
Internet activity, including firewall logs, caches, browser
history and cookies, "bookmarked" or "favorite" web pages,
search terms that the user entered into any Internet search
engine, and records of user-typed web addresses.
2. As used herein, the terms "records," "documents,"
"programs," "applications," and "materials" include records,
documents, programs, applications, and materials created,
20 INSTRUMENTALITY PROTOCOL
modified, or stored in any form, including in digital form on
any digital device and any forensic copies thereof.
3. As used herein, the term "digital device" includes any
electronic system or device capable of storing or processing
data in digital form, including central processing units;
desktop, laptop, notebook, and tablet computers; personal
digital assistants; wireless communication devices, such as
telephone paging devices, beepers, mobile telephones, and smart
phones; digital cameras; peripheral input/output devices, such
as keyboards, printers, scanners, plotters, monitors, and drives
intended for removable media; related communications devices,
such as modems, routers, cables, and connections; storage media,
such as hard disk drives, floppy disks, memory cards, optical
disks, and magnetic tapes used to store digital data (excluding
analog tapes such as VHS); and security devices.
II. SEARCH PROCEDURE FOR DIGITAL DEVICES
4. In searching digital devices or forensic copies
thereof, law enforcement personnel executing this search warrant
will employ the following procedure:
a. Law enforcement personnel or other individuals
assisting law enforcement personnel (the "search team") will, in
their discretion, either search the digital device(s) on-site or
seize and transport the device(s) to an appropriate law
enforcement laboratory or similar facility to be searched at
21 INSTRUMENTALITY PROTOCOL
that location. The search team shall complete the search as
soon as is practicable but not to exceed 60 days from the date
of execution of the warrant. If additional time is needed, the
government may seek an extension of this time period from the
Court on or before the date by which the search was to have been
completed.
b. The search team will conduct the search only by
using search protocols specifically chosen to identify only the
specific items to be seized under this warrant.
i. The search team may subject all of the data
contained in each digital device capable of containing any of
the items to be seized to the search protocols to determine
whether the device and any data thereon falls within the list of
items to be seized. The search team may also search for and
attempt to recover deleted, "hidden," or encrypted data to
determine, pursuant to the search protocols, whether the data
falls within the list of items to be seized.
ii. The search team may use tools to exclude
normal operating system files and standard third-party software
that do not need to be searched.
c. When searching a digital device pursuant to the
specific search protocols selected, the search team shall make
and retain notes regarding how the search was conducted pursuant
to the selected protocols.22 INSTRUMENTALITY PROTOCOL
d. If the search team, while searching a digital
device, encounters immediately apparent contraband or other
evidence of a crime outside the scope of the items to be seized,
the team shall immediately discontinue its search of that device
pending further order of the Court and shall make and retain
notes detailing how the contraband or other evidence of a crime
was encountered, including how it was immediately apparent
contraband or evidence of a crime.
e. If the search determines that a digital device
does not contain any data falling within the list of items to be
seized, the government will, as soon as is practicable, return
the device and delete or destroy all forensic copies thereof.
f. If the search determines that a digital device
does contain data falling within the list of items to be seized,
the government may make and retain copies of such data, and may
access such data at any time.
g. If the search determines that a digital device is
(1) itself an item to be seized and/or (2) contains data falling
within the list of items to be seized, the government may retain
forensic copies of the digital device but may not access them
(after the time for searching the device has expired) absent
further court order.
h. The government may retain a digital device itself
until further order of the Court or one year after the23 INSTRUMENTALITY PROTOCOL
conclusion of the criminal investigation or case (whichever is
latest), only if the device is determined to be an
instrumentality of an offense under investigation or the
government, within 14 days following the time period authorized
by the Court for completing the search, obtains an order from
the Court authorizing retention of the device (or while an
application for such an order is pending). Otherwise, the
government must return the device.
i. Notwithstanding the above, after the completion
of the search of the digital devices, the government shall not
access digital data falling outside the scope of the items to be
seized absent further order of the Court.
5. In order to search for data capable of being read or
interpreted by a digital device, law enforcement personnel are
authorized to seize the following items:
a. Any digital device capable of being used to
commit, further or store evidence of the offense(s) listed
above;
b. Any equipment used to facilitate the
transmission, creation, display, encoding, or storage of digital
data; c. Any magnetic, electronic, or optical storage
device capable of storing digital data;
24 INSTRUMENTALITY PROTOCOL
d. Any documentation, operating logs, or reference
manuals regarding the operation of the digital device or
software used in the digital device;
e. Any applications, utility programs, compilers,
interpreters, or other software used to facilitate direct or
indirect communication with the digital device;
Any physical keys, encryption devices, dongles,
or similar physical items that are necessary to gain access to
the digital device or data stored on the digital device; and
g. Any passwords, password files, test keys,
encryption codes, or other information necessary to access the
digital device or data stored on the digital device.
6. The special procedures relating to digital devices
found in this warrant govern only the search of digital devices
pursuant to the authority conferred by this warrant and do not
apply to any search of digital devices pursuant to any other
court order.
7. The government is allowed to share the information
obtained from this search (to include copies of digital media)
with any government agency investigating, or aiding in the
investigation of, this case or related matters.
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.









