For years it has been the case that the Digital Millennium Copyright Act (DMCA) has had a chilling effect on, among other things, security research. That is because the intended chilling effect on copying things, such as music, also bleeds over to research and development of anything related to any device or code which is ‘protected’ under the DMCA. Legal scholars, technologists, and security researchers have argued that the DMCA – and in particular section 1201 of the Digital Millennium Copyright Act – is unconstitutional for this very reason.
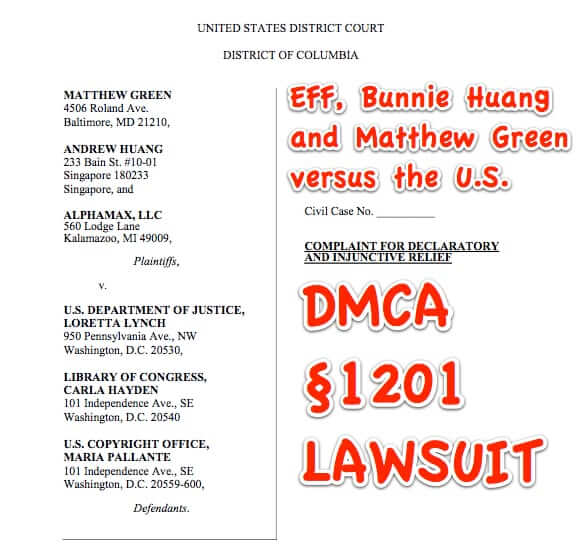
Now security darling Andrew ‘bunnie’ Huang, and the Electronic Frontier Foundation (EFF), along with attorneys at Wilson, Sonsini, Goodrich and Rosati, have filed a class-action lawsuit aimed at proving that Section 1201 of the DMCA is unconstitutional.
Section 1201 (or, in legalese, §1201) of the Digital Millennium Copyright Act is the section of the DMCA that deals with anti-circumvention and access control (digital rights management, or ‘DRM’), and which makes it illegal to circumvent such access control measures.
§1201 provides that, among other things, it is a violation of the DMCA to circumvent a technological measure that effectively controls access to a protected work. DVDs are a great example (see below).
Section 1201 defines ‘circumvent a technological measure’ as “to descramble a scrambled work, to decrypt an encrypted work, or otherwise to avoid, bypass, remove, deactivate, or impair a technological measure, without the authority of the copyright owner.” DVD players are another great example (also see below).
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.
“Effectively controlling access” means “if the measure, in the ordinary course of its operation, requires the application of information, or a process or a treatment, with the authority of the copyright owner, to gain access to the work.”
17 U.S. Code § 1201 – Circumvention of copyright protection systems (in part)
Violations Regarding Circumvention of Technological Measures.—
(1)(A) No person shall circumvent a technological measure that effectively controls access to a work protected under this title.and
2) No person shall manufacture, import, offer to the public, provide, or otherwise traffic in any technology, product, service, device, component, or part thereof, that –
(A) is primarily designed or produced for the purpose of circumventing a technological measure that effectively controls access to a work protected under this title;
(B) has only limited commercially significant purpose or use other than to circumvent a technological measure that effectively controls access to a work protected under this title; or
(C) is marketed by that person or another acting in concert with that person with that person’s knowledge for use in circumventing a technological measure that effectively controls access to a work protected under this title.
The Guardian has a great article that explains what this all means to the average security researcher – and to the average Joe. Basically, as they explain, “Originally, this was used exclusively by the entertainment industries: by adding DRM to DVDs, they could prevent companies from making DVD players that accepted DVDs bought abroad. It’s not illegal to bring a DVD home from an overseas holiday and watch it, but if your DVD player recognises the disc as out-of-region, it is supposed to refuse to play it back, and the act of altering the DVD player to run out-of-region discs is unlawful under the DMCA’s section 1201. It could even be a crime carrying a five-year prison sentence and a $500,000 fine for a first offense (the act of offering a region-free DVD player for sale, or even the neighbour’s kid helping you to deregionalise your DVD player, can be criminal acts).”
In case your mind isn’t boggled enough yet, this also means that if security researchers discover a security hole that happens to also be a hole in the DRM scheme, which then… wait for it … circumvents the DRM, they can be facing a whole world of hurt.
For example the Secure Digital Music Initiative (a working group of about 200 companies who wanted to further and strengthen DRM) issued a public challenge for researchers to find holes in their DRM scheme. Then, when a group of computer and security researchers, led by Ed Felten, actually discovered such defects, and were planning to present their findings at USENIX, SDMI and the RIAA sued them under the DMCA to shut them up! (The EFF stood up for Felten.)
Plaintiffs bring this action to enjoin enforcement of the DMCA Anti- Circumvention Provisions, on their face and as applied to them, as violating the First Amendment to the U.S. Constitution.
So, this brings us to the instant lawsuit, by Bunnie Huang and Matthew Green, and for all those similarly situated.
Green is a security researcher who researches, among other things, the security of cryptography used for securing financial transactions such as ATM transactions and credit card processing. Under §1201, even this obviously important – indeed critical – sort of research can be seen as violating the DMCA.
Huang, who is perhaps best known among consumers as the inventor of the much-beloved Chumby (R.I.P.) is developing a device that allows users to record and manipulate digital video images, and of course with the threat of §1201 hanging over his head, there is an innovation-crippling effect.
Some ways in which the lawsuit states that §1201 violates the First Amendment include:
- Restricting the public “from making routine, personal uses of lawfully acquired copyrighted works, such as transferring an ebook to a new device or by converting a Blu-ray disc to a format that can be viewed on a particular device.”
- Burdening a “substantial range of protected speech that is disproportionate to its legitimate sweep.”
- Being an unconstitutional prior restraint on speech, which prevents legitimate speech before it occurs.”
- Being used to thwart Green’s right to publish information related to security research that involves circumvention.
- Prohibiting Huang “from building or using the NeTVCR even in order to engage in circumventions that would not infringe copyright and without regard for the traditional safeguards that harmonize copyright law with the First Amendment, such as fair use.”
The lawsuit is asking for:
A. A declaration that the anti-circumvention rule and the anti-trafficking rule are facially overbroad in violation of the First Amendment.
B. A declaration that the anti-circumvention rule and the triennial rulemaking process are a facially unlawful prior restraint and licensing regime in violation of the First Amendment.
C. An injunction that enjoins the DOJ and Lynch from enforcing the criminal prohibitions on circumvention and trafficking.
D. A declaration that the anti-circumvention rule and the anti-trafficking rule violate the First Amendment as applied to Green.
E. An injunction that enjoins the DOJ and Lynch from enforcing the criminal prohibitions on circumvention and trafficking against Green.
F. A declaration that the anti-circumvention rule and the anti-trafficking rule violate the First Amendment as applied to Huang.
G. An injunction that enjoins the DOJ and Lynch from enforcing the criminal prohibitions on circumvention and trafficking against Huang.
H. A declaration that the anti-circumvention rule and the anti-trafficking rule violate the First Amendment as applied to Alphamax.
I. An injunction that enjoins the DOJ and Lynch from enforcing the criminal prohibitions on circumvention and trafficking against Alphamax.
J. A declaration that the Rulemaking Defendants, by refusing to grant the pertinent exemptions, violated the First Amendment and the APA.
K. An injunction that enjoins the Rulemaking Defendants to grant the pertinent exemptions.
L. A declaration that the Rulemaking Defendants, by considering factors that do not concern copyright as a basis to deny or narrow exemptions, violated the First Amendment and the DMCA.
M. An award of attorney fees, costs, and expenses under 42 U.S.C. 1988.
N. Such other relief as the Court deems proper.
You can read the entire complaint here, courtesy of the EFF:
The Internet Patrol is completely free, and reader-supported. Your tips via CashApp, Venmo, or Paypal are appreciated! Receipts will come from ISIPP.









